Daniel Engberg retweetet

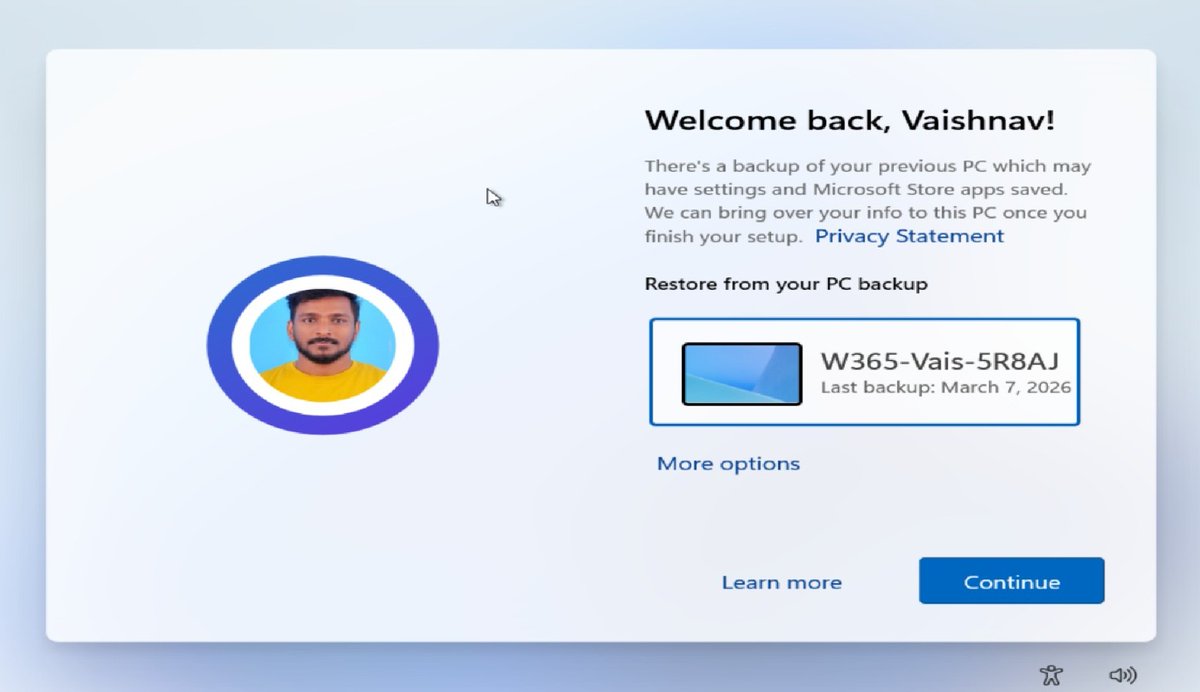
🚀 New Post Alert!
I’m excited to share my latest guide on how to create Windows 365 Frontline Dedicated Cloud PCs using Microsoft Intune. anoopcnair.com/frontline-dedi…
#MSIntune #Windows365 #Intune #Frontline #Dedicated #CloudPC #W365Community #HTMDCommunity
English









![Maurice Daly [MVP]](https://pbs.twimg.com/profile_images/1182232265255981056/RrKR33Pc.jpg)