Kevin.m retweetet

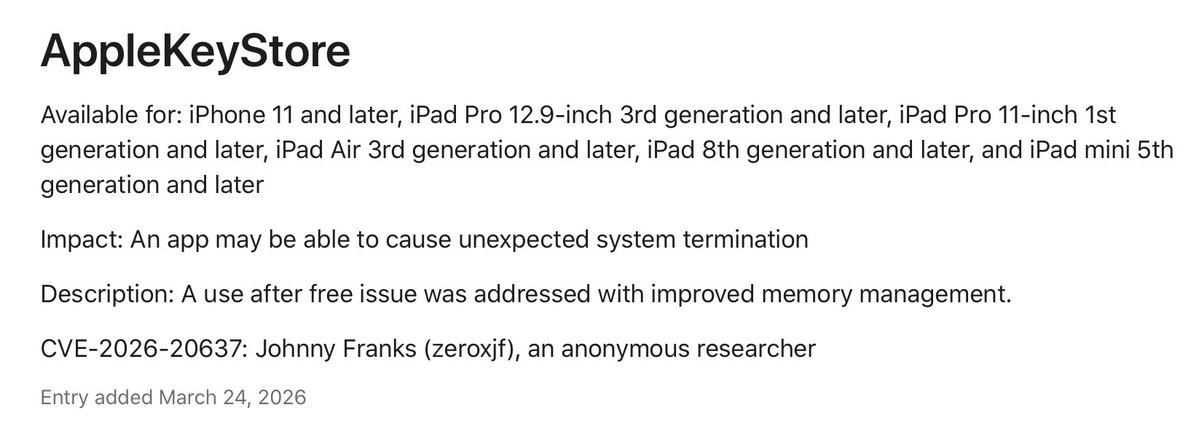
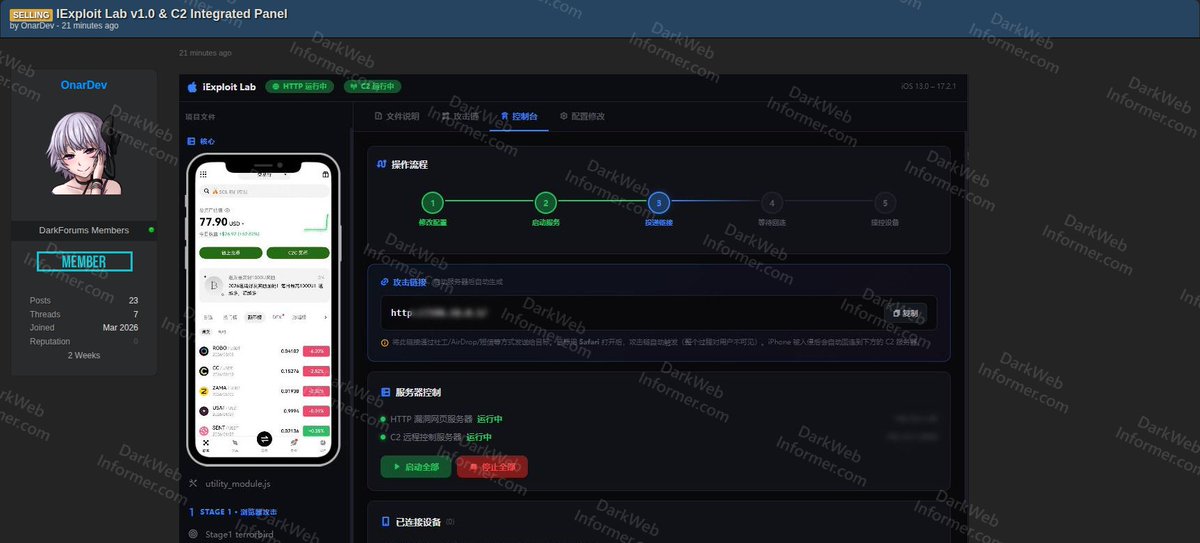
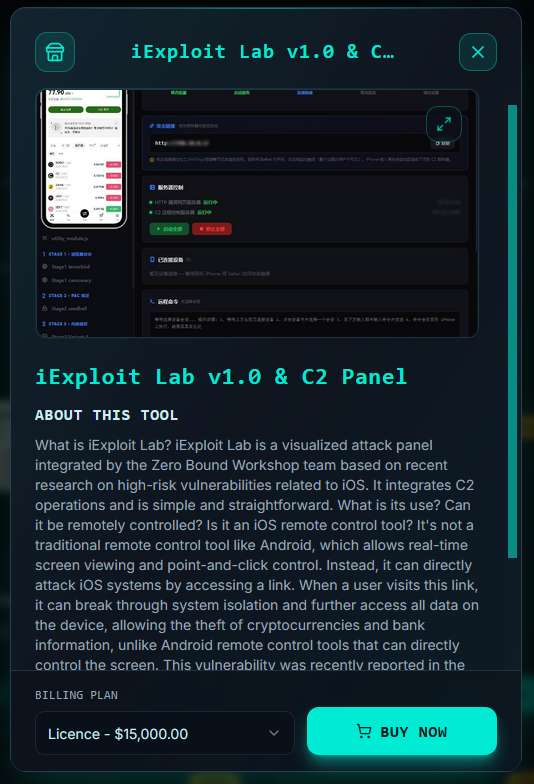
‼️An iOS exploit and C2 integrated attack panel called "iExploit Lab v1.0" is being advertised on a popular cybercrime forum, targeting iOS 13 through iOS 17.2.1 for $15,000.
‣ Threat Actor: OnarDev
‣ Category: Exploit / Tool
‣ Name: iExploit Lab v1.0
‣ Target: iOS 13 to iOS 17.2.1
‣ Developer: Zero Bound Workshop team
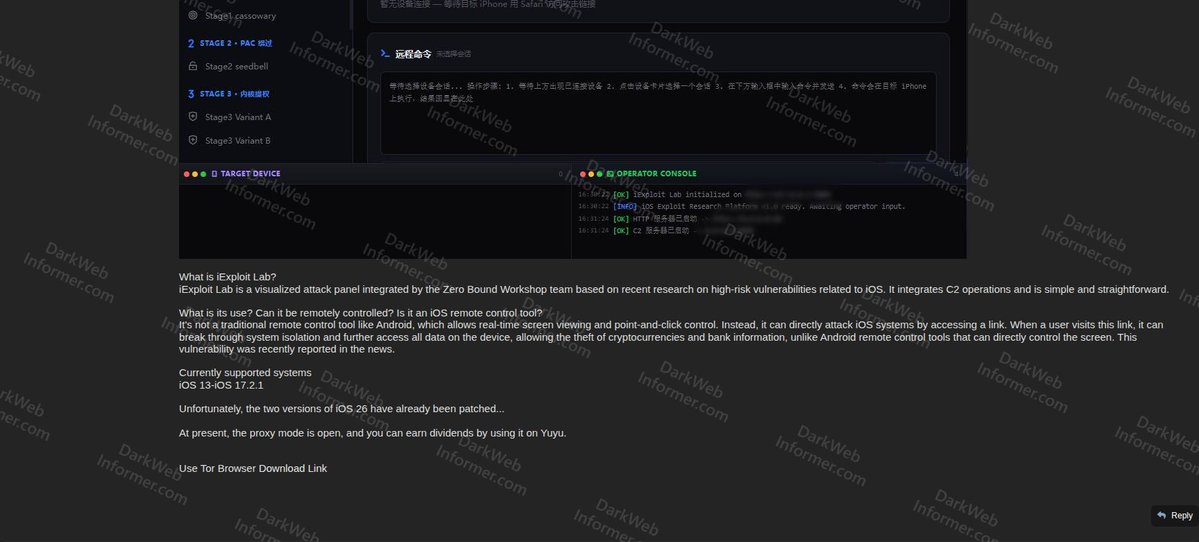
iExploit Lab is a visualized attack panel integrating C2 operations based on recent research on high-risk iOS vulnerabilities. It is not a traditional remote control tool but instead attacks iOS systems when a user visits a link via Safari.
Attack stages:
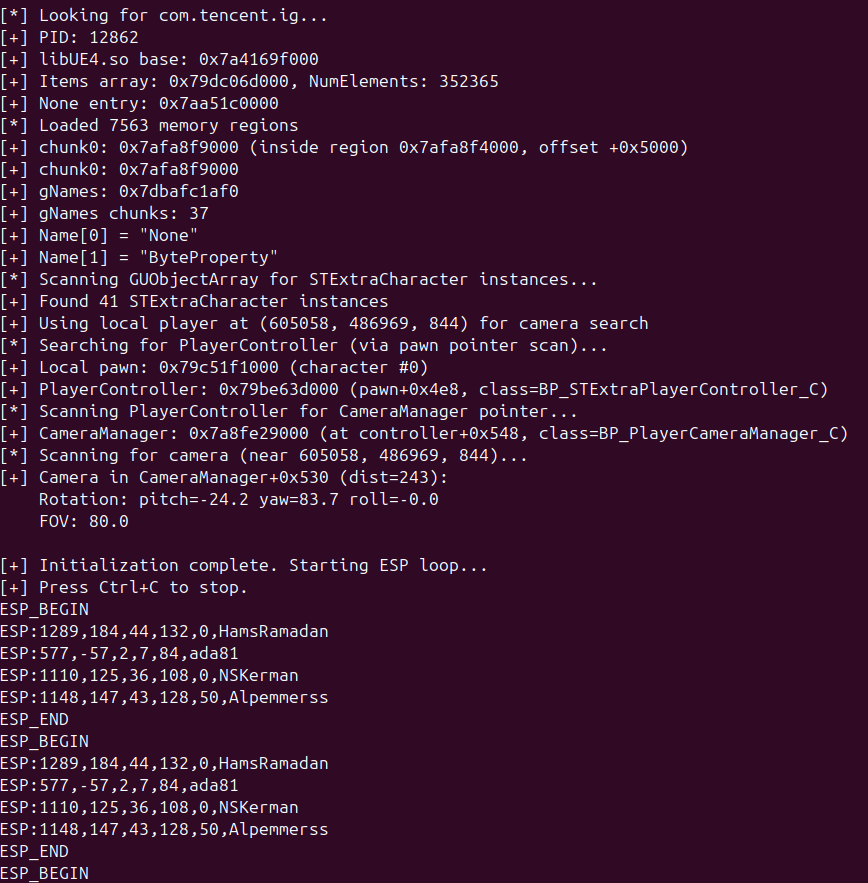
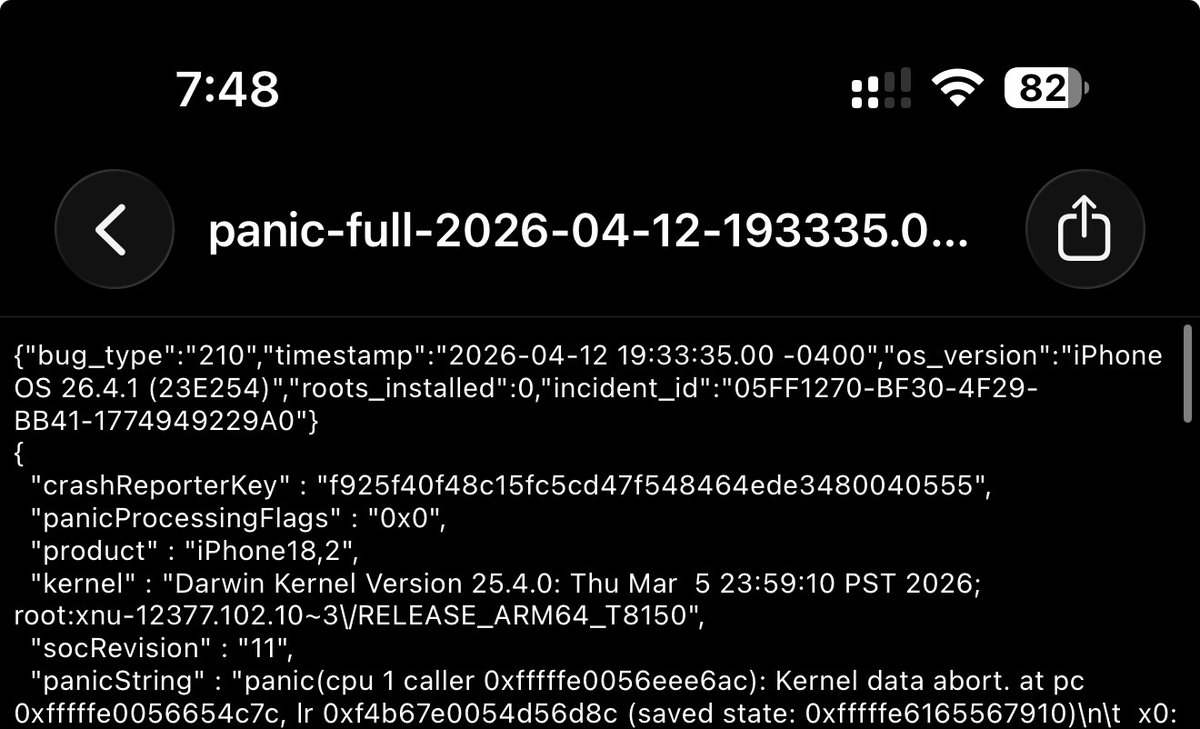
▪️ Stage 1 - Browser Attack (Stage1 terrorbird / Stage1 cassowary)
▪️ Stage 2 - PAC Bypass (Stage2 seedbell)
▪️ Stage 3 - Kernel Privilege Escalation (Stage3 Variant A / Stage3 Variant B)
Capabilities:
▪️ Break through system isolation and access all data on device
▪️ Theft of cryptocurrencies and bank information
▪️ Integrated HTTP vulnerability web server and C2 remote control server
▪️ Attack link auto-generated after server startup
▪️ Link delivered via social engineering, AirDrop, or other methods (one-click via Safari)
▪️ Connected device management panel
▪️ Operator console with real-time logging
The panel UI is in Chinese with a 5-step operational workflow: modify configuration, start services, set up connection, wait for callback, and control device. The actor notes that the two iOS 26 versions have already been patched. Proxy mode is available for earning dividends.
English