


Scott Lynch
20.4K posts


@packetengineer
Certified @SANSDefense Instructor | SECOPS/CERT Manager | Defcon BTV | Navy Vet | Sailor | Tweets Are My Own



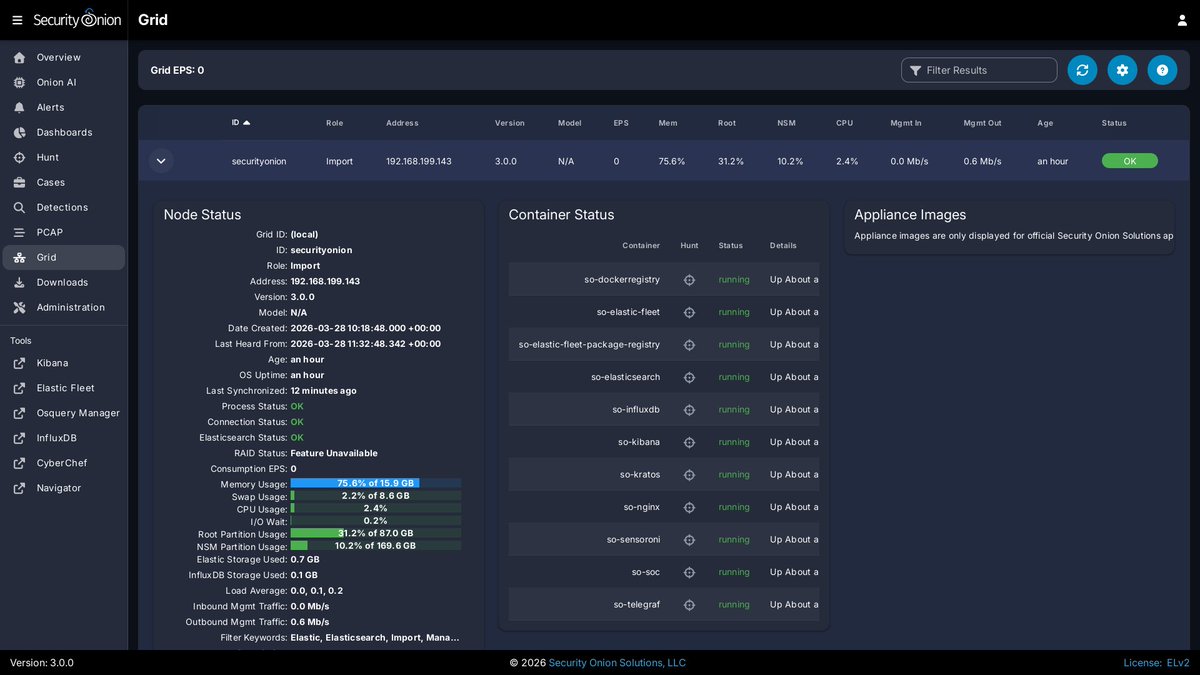


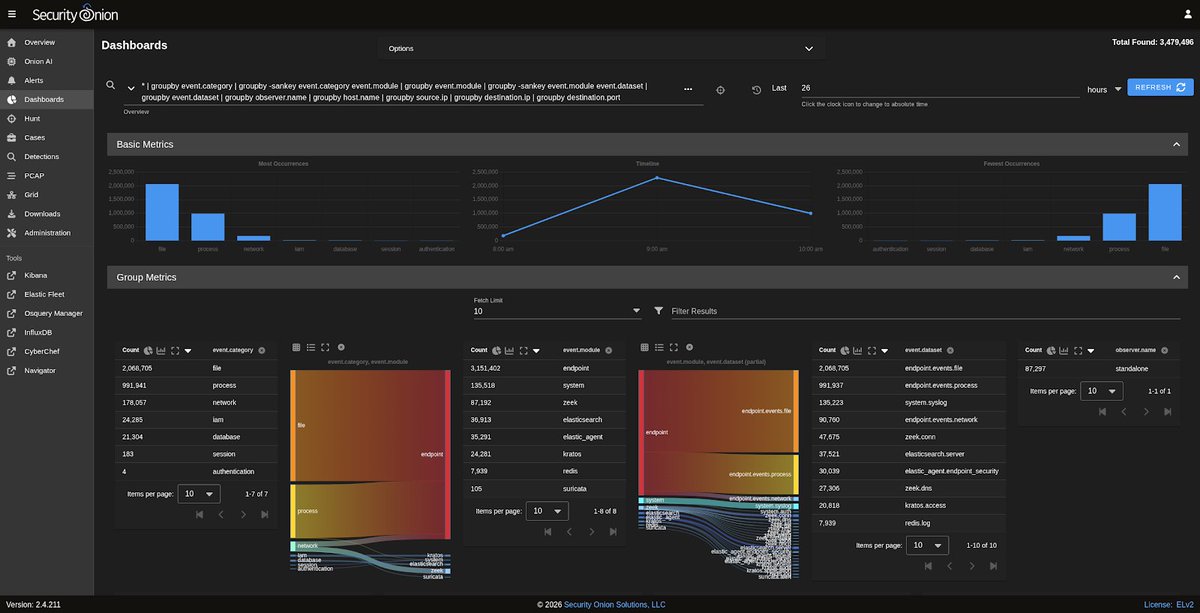
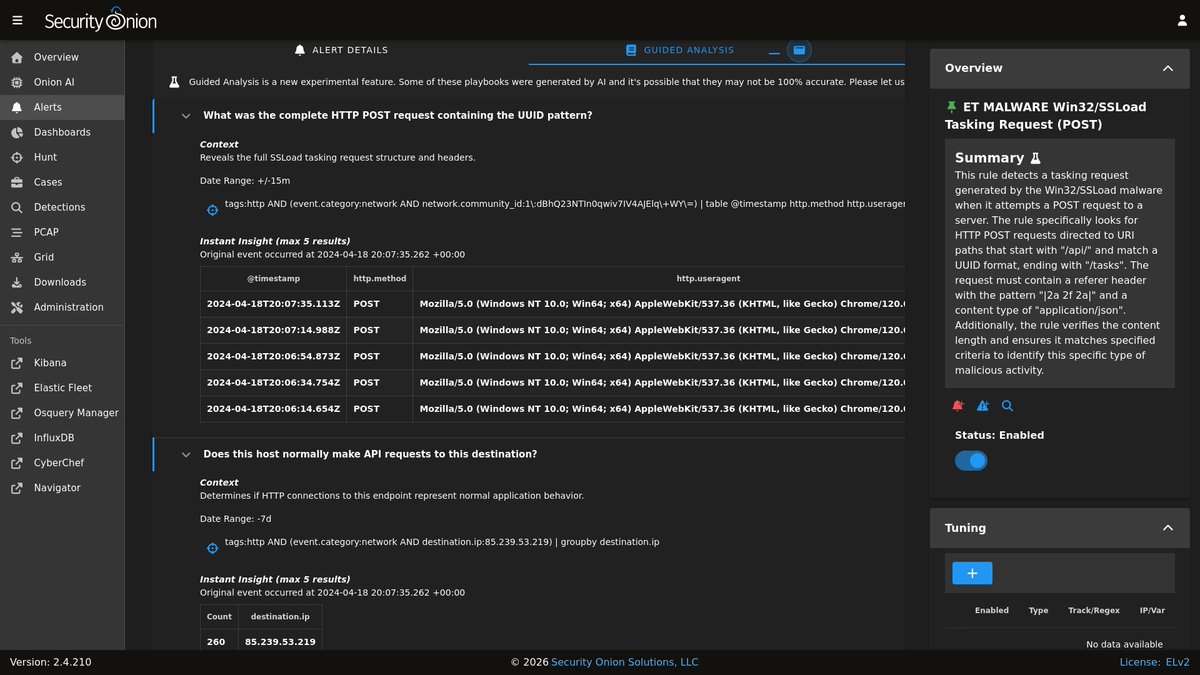


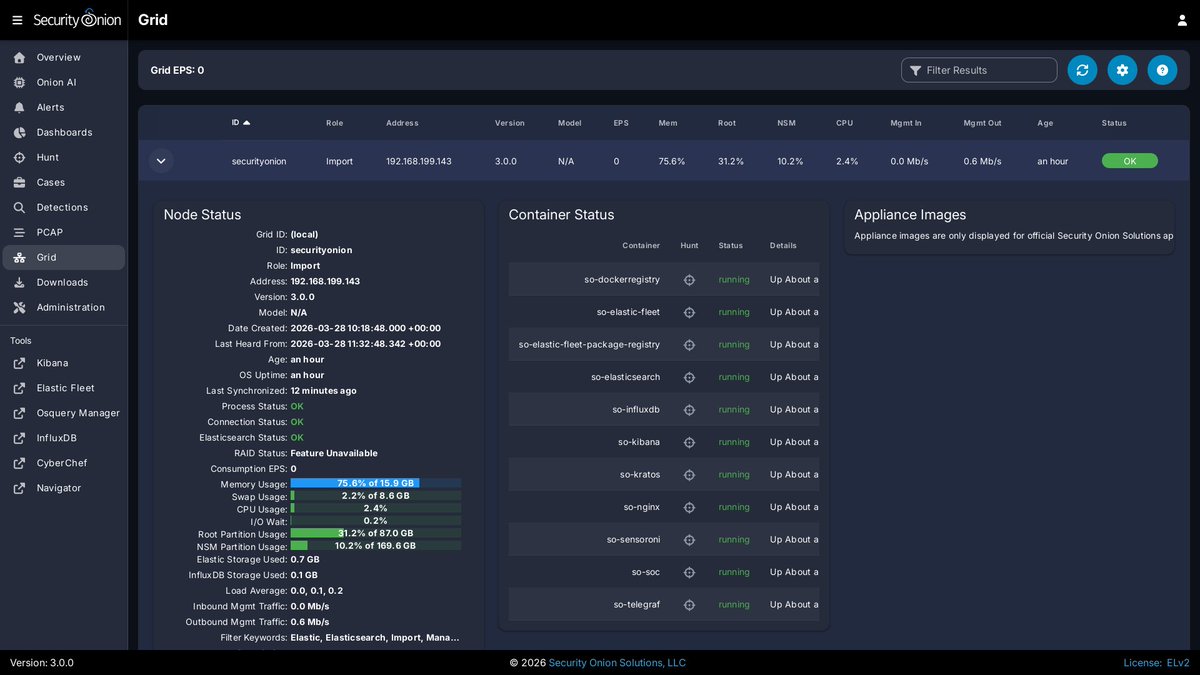
We’ve published a deep dive into how Aurora uses ETW to reconstruct structured event data for detection engineering The post covers: - ETW-based logsource mappings - Custom field enrichment (e.g., ProcessTree, GrandparentCommandLine) - Gaps in ETW coverage and where minimal Sysmon configs help - Practical detection use cases with full Sigma rules - Techniques for exploring ETW with --trace and writing custom rules 🔗 nextron-systems.com/2025/07/31/aur… by @_swachchhanda_ #Sigma #AuroraAgent #ETW #DetectionEngineering

We analyzed the top 500 most successful THOR rules – “successful” meaning: they detected samples that were either ignored or missed by nearly all AV engines on VirusTotal. Some rules detect clear malware. Others reveal dual-use tools, renamed hacktools, misused admin binaries, or forensic leftovers. Most of these samples showed 0 AV detections, the rest only minimal hits. Not all threats are payloads. Not all detections are flashy. But these rules consistently light up the blind spots in AV and EDR coverage – where attackers hide comfortably. THOR doesn’t replace existing tools. It shows you what they forgot to tell you. nextron-systems.com/2025/06/18/the…



