⟨GOD»CALL⟩
1.4K posts






Tonight, we reached an agreement with the Department of War to deploy our models in their classified network. In all of our interactions, the DoW displayed a deep respect for safety and a desire to partner to achieve the best possible outcome. AI safety and wide distribution of benefits are the core of our mission. Two of our most important safety principles are prohibitions on domestic mass surveillance and human responsibility for the use of force, including for autonomous weapon systems. The DoW agrees with these principles, reflects them in law and policy, and we put them into our agreement. We also will build technical safeguards to ensure our models behave as they should, which the DoW also wanted. We will deploy FDEs to help with our models and to ensure their safety, we will deploy on cloud networks only. We are asking the DoW to offer these same terms to all AI companies, which in our opinion we think everyone should be willing to accept. We have expressed our strong desire to see things de-escalate away from legal and governmental actions and towards reasonable agreements. We remain committed to serve all of humanity as best we can. The world is a complicated, messy, and sometimes dangerous place.


🛠️ DevLog – Session Data Mobility: First Export Pass
We now have the first working export path for Session data on Testnet-0.
🔹 What’s Working
- New off-chain Session export tool walks sessions in batches and writes:
- one session_

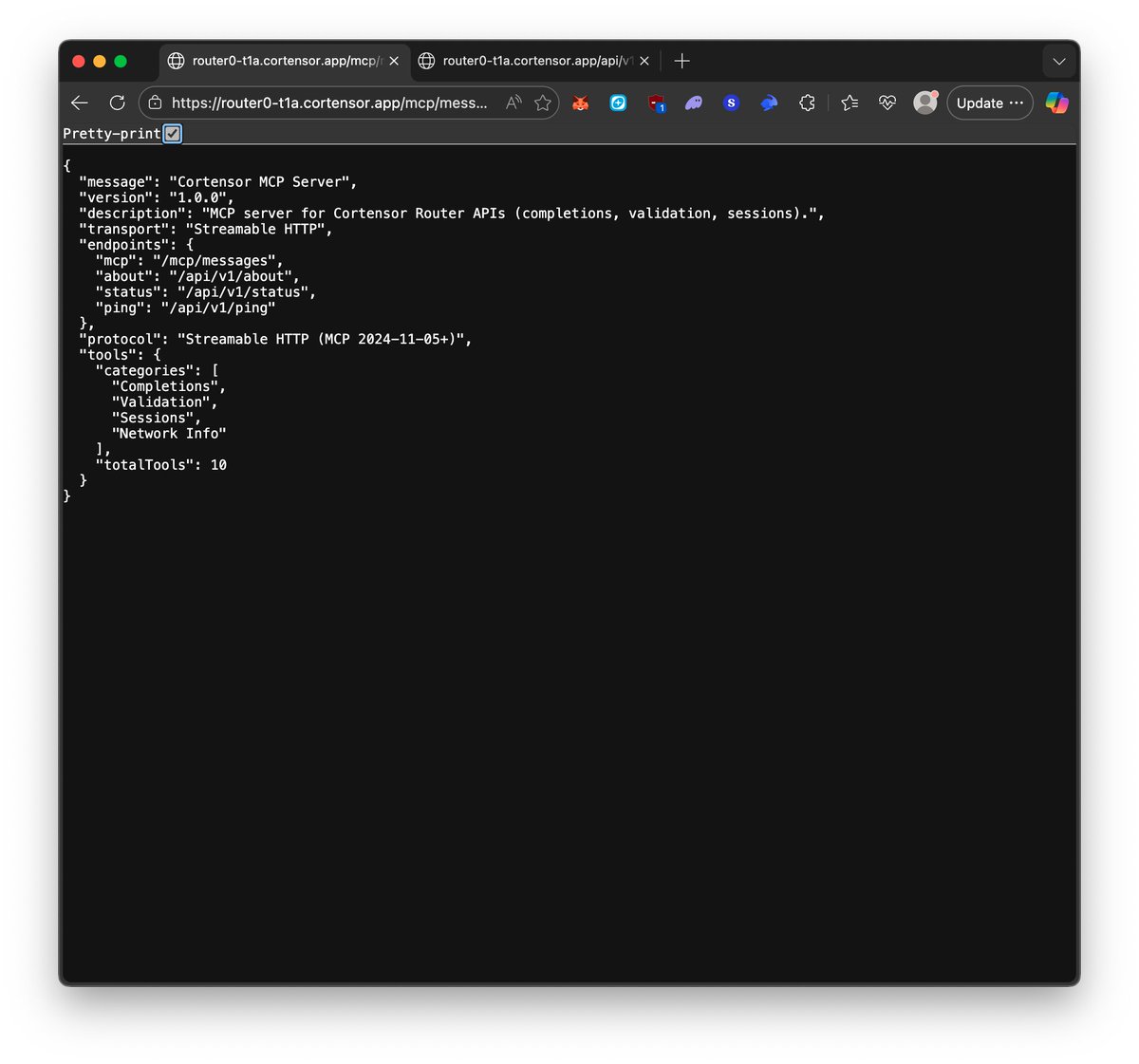

🛠️ DevLog – MCP + ERC-8004 Interop Patch Live on Corgent & Bardiel We’ve now applied the MCP + ERC-8004 interop patch to the mainnet Corgent/Bardiel agents and started testing it in-place. 🔹 What Changed - Tweaked MCP stream + metadata behavior so clients that expect more static agent/tool info (like 8004scan) can read health status cleanly. - Redeployed the router nodes behind the mainnet agents with the updated MCP behavior. 🔹 Where It’s Live Corgent (mainnet): 8004scan.io/agents/ethereu… Bardiel (mainnet): 8004scan.io/agents/ethereu… 🔹 What We’re Testing Now - Verifying there’s no regression with standard MCP clients (OpenAI, Claude Tools, etc.) while 8004scan health checks read correctly. - Watching agent health + logs on these endpoints and, if stable, we’ll mirror the pattern across testnets and future MCP surfaces. #Cortensor #DevLog #MCP #ERC8004 #Corgent #Bardiel #AgenticAI


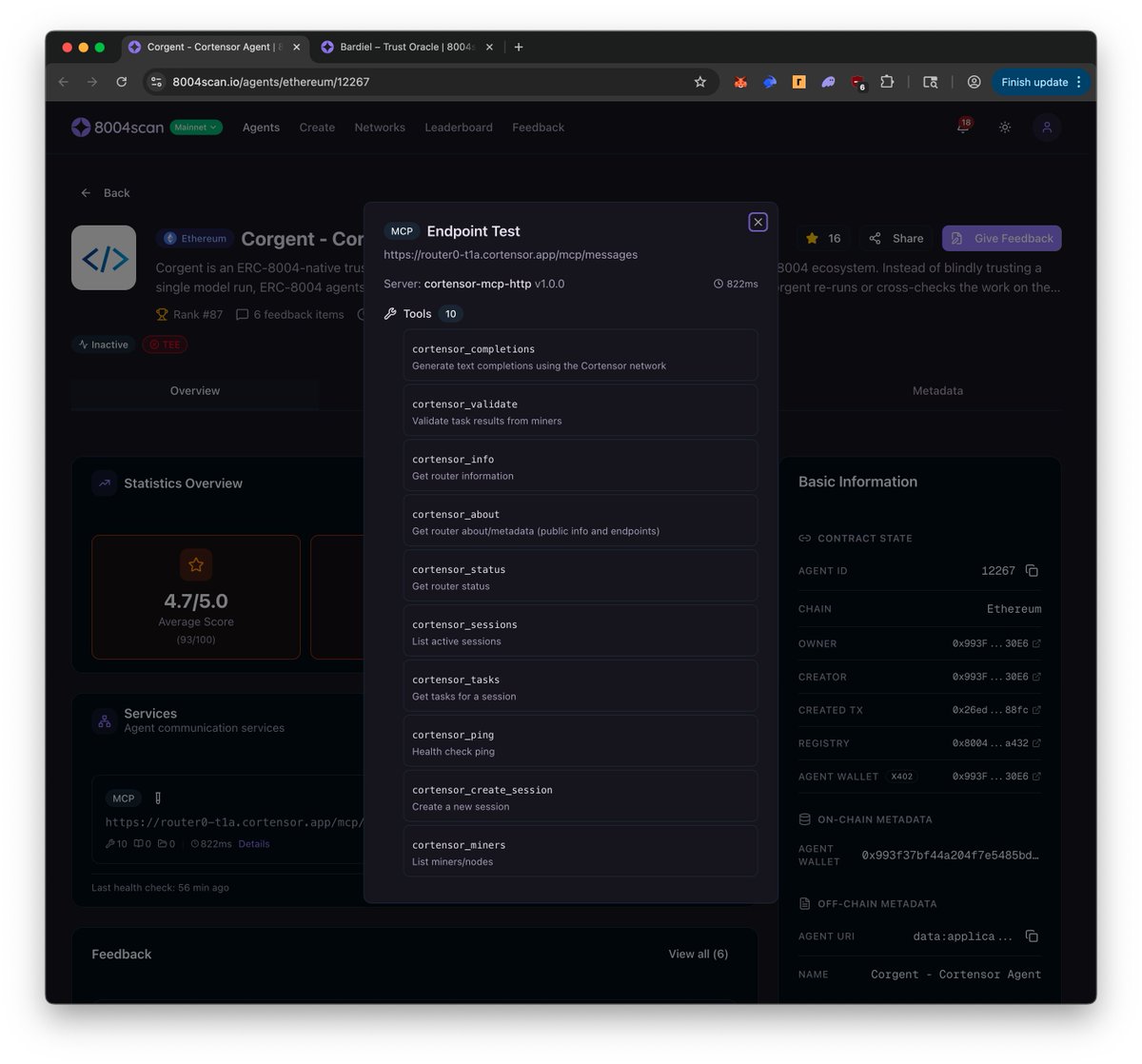
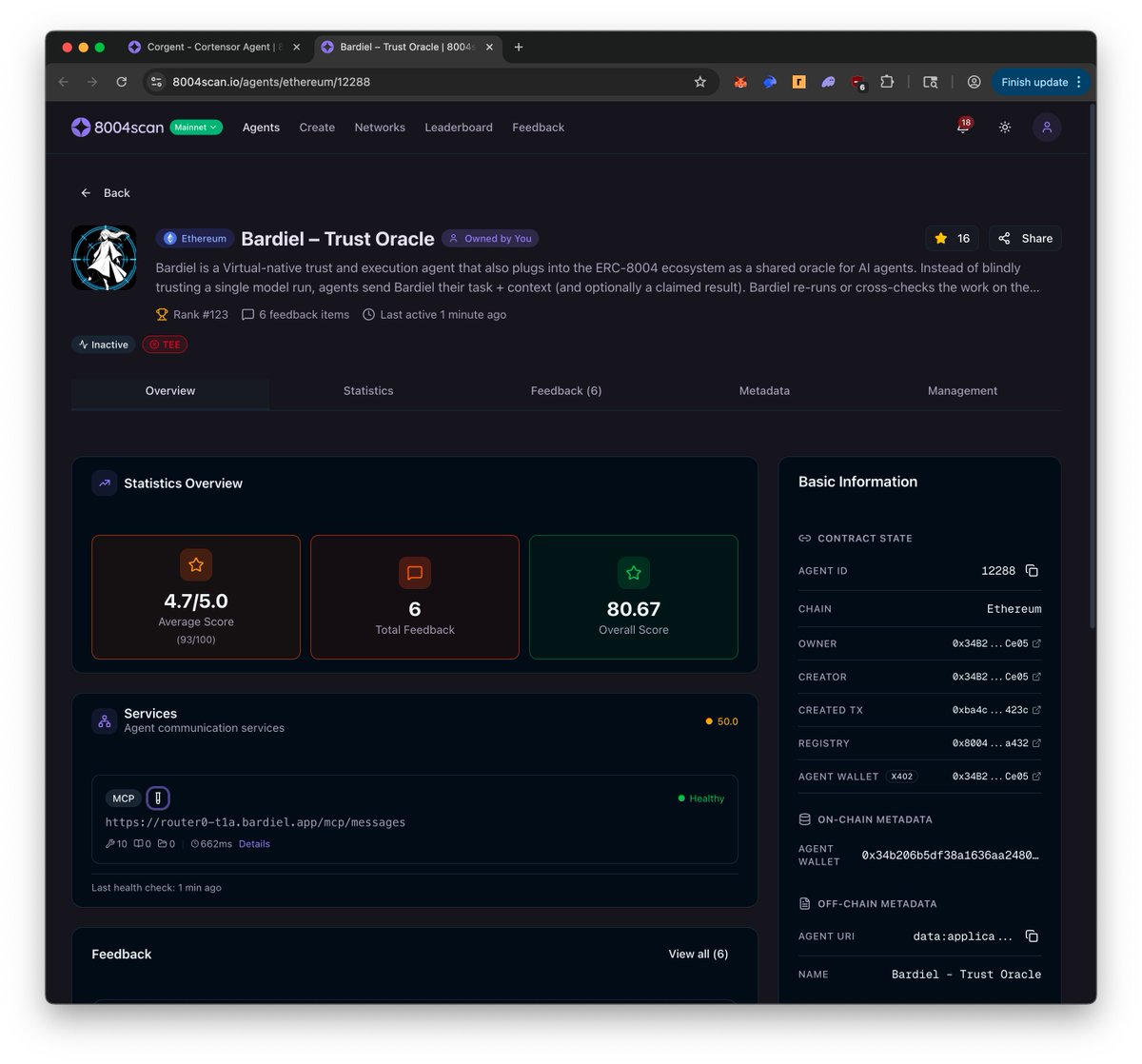
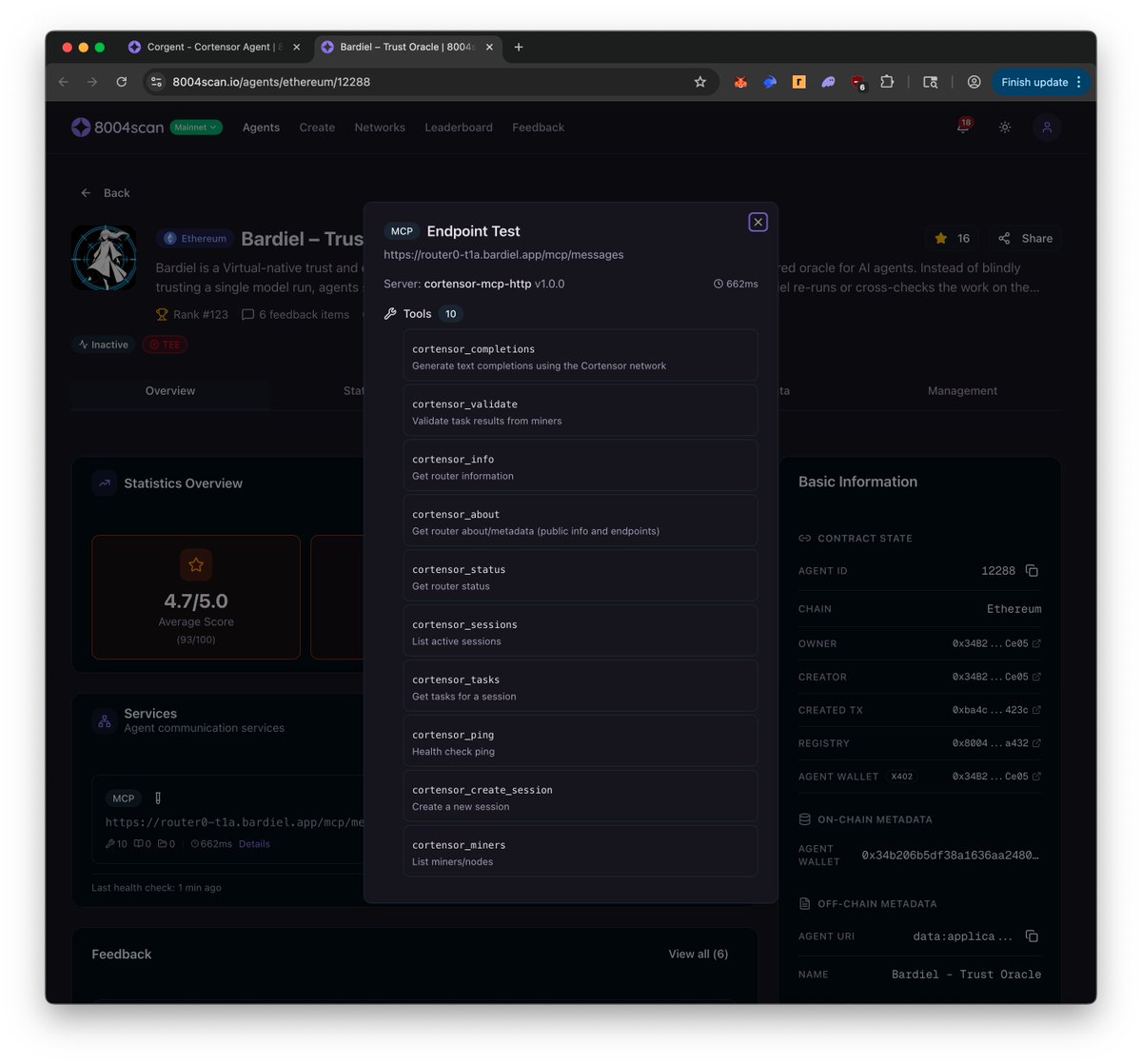
🛠️ DevLog – #MCP + #ERC8004 Interop Patch: Testing, Regression, Monitoring We’ve enabled the new #MCP “static advertisement” payload on the router endpoints behind the mainnet Corgent and Bardiel #ERC8004 agents, and are now focused on testing + monitoring rather than adding new behavior. 🔹 What’s Under Test •New MCP discovery response that advertises tools, categories, and protocol info up front so 8004scan can read agent health correctly. •Config-gated behavior on the mainnet router nodes backing Corgent and Bardiel (no change to core routing logic or task execution). 🔹 Where It’s Running •Corgent (mainnet agent): 8004scan.io/agents/ethereu… •Bardiel (mainnet agent): 8004scan.io/agents/ethereu… •Corgent MCP messages: router0-t1a.cortensor.app/mcp/messages •Bardiel MCP messages: router0-t1a.bardiel.app/mcp/messages 🔹 What We’re Watching •Regression against standard #MCP clients (#OpenAI tools, #Claude tools) to ensure /completions, /validate, /delegate, etc. still behave as before. •8004scan health status for both agents to confirm they pick up the static MCP advertisement and mark them healthy. •Endpoint logs + error rates; if everything holds up, we’ll mirror this MCP pattern to testnets and future agent surfaces. #Cortensor #DevLog #MCP #ERC8004 #Corgent #Bardiel #AgenticAI

🗓️ Weekly Focus – Phase #2 Hardening, Agent Surfaces & Data Mobility This week continues the Phase #2 push with stability first, deeper Testnet-1a iteration, and follow-up work on agent-facing endpoints. 🔹 Testnet Phase #2 – Stability & Support - Ongoing monitoring across routing, miners, validators, oracles, indexers, and dashboards. - Fast follow-ups on abnormal node states and performance regressions. 🔹 Testnet-1a (Self-Managed L3) – Ops + Load - Completed the full operational checklist for Testnet-1a (baseline stability, capacity, monitoring). - Move into replay / break-testing mode: intentionally stress failure paths, replay incidents, and test recovery. - Run targeted base fee adjustment exercises to observe behavior under changing fee conditions and capture learnings in the L3 ops playbook. 🔹 Hackathon #4 Support - Ongoing builder support: answering asks, reviewing ideas, and guiding validation/delegation patterns. 🔹 /delegate & /validate Iteration (Follow-Up Week) - Resume deeper iteration on /delegate and /validate (templates, tooling, reliability). - Keep /delegate progressing as a thin agent SDK surface. 🔹 MCP + ERC-8004 Interop Patch (Corgent/Bardiel) - Includes small adjustments to deployed ERC-8004 agents so MCP metadata/health checks are more client-friendly. - Patch MCP stream behavior, redeploy router nodes, and re-check agent health. - Corgent: 8004scan.io/agents/ethereu… - Bardiel: 8004scan.io/agents/ethereu… 🔹 Data Mobility – Import/Export Rough Assessment - Start mapping import/export shapes for Session/Queue, payments, and NodePool metadata. - Run small migration drills (snapshot → export → re-import) to validate repeatability. #Cortensor #Testnet #AIInfra #DePIN #Corgent #Bardiel #AgenticAI #ERC8004 #MCP #PoI #PoUW #L3



🗓️ Weekly Recap – Phase #2 Hardening, L3 Ops Progress & SLA Prep This week we completed nearly all planned focus items for Phase #2, with one item rolling over into next week. 🔹 Testnet Phase #2 – Stability & Support - Continued active monitoring and support across routing, miners, validators, oracles, indexers, and dashboards. - Follow-ups on abnormal node states and performance regressions helped keep Phase #2 stable. 🔹 Testnet-1a (Self-Managed L3) Iteration + Ops Playbook - Further iteration on Testnet-1a from an operational perspective (reliability, throughput, failure modes). - Expanded and refined the L3 operational playbook based on real-world incidents and exercises. 🔹 Hackathon #4 Support - Ongoing support for Hackathon #4 builders with reviews, guidance, and feedback loops. 🔹 SLA Filters – Ranking Logic Ported - Ported validation and ranking table logic into NodePoolUtil, preparing it as a first-class signal for routing. - This sets the stage for SLA-aware filters in the node selection pipeline. 🔹 RPC Resilience + Gas Optimization - Reduced RPC call volume and tightened gas usage for cortensord and miner operations. - Added support for configurable and rotating RPC endpoints, improving reliability under load. 🔹 /delegate & /validate Iteration (Follow-Up) - Deeper iteration on /delegate and /validate was lighter than planned and will continue next week. A strong execution week - Phase #2 stability improved, self-managed L3 ops matured, routing is closer to SLA-aware selection, and core infra reliability is tighter. #Cortensor #Testnet #AIInfra #DePIN #Validator #PoI #PoUW #Hackathon #Corgent #AgenticAI #L3


🔹 DevLog – Data Mobility & Data Module Import/Export (Early Design Thoughts) As we see real data growth on the self-managed #L3, it’s becoming clearer that storage growth itself isn’t the real problem - data mobility is. 🔹 What We’re Thinking About - Instead of worrying only about raw disk size, we’re focusing on how to move and reshape state cleanly over time. - The idea is to support import/export for core data modules, so we can migrate or hardfork infra without losing the “logical” network state. Target data modules for import/export design: - Session Data – user sessions, configs, runtime state - Session Queue Data – queued tasks and routing state - Session Payment Data – balances, credits, pending payouts - Node Pool Data – node specs, capacity, reputation metadata 🔹 Why This Matters - As long as these data modules can be exported/imported and we can safely transfer Session Payment balances to a new deployment, storage growth on any single #L3 instance is manageable, not fatal. - This would give us a controlled way to: - Perform hardforks when necessary in production/mainnet - Migrate to new infra (or new #L3 setups) while preserving critical network state - Treat $COR #L3 as an orchestration layer that can evolve operationally as load increases. 🔹 Next Step We’ll start deeper design + brainstorming on data module import/export flows so future #L3 hardforks and infra migrations are deliberate tools, not emergencies. #Cortensor #DevLog #L3 #DataMobility #AIInfra #DePIN



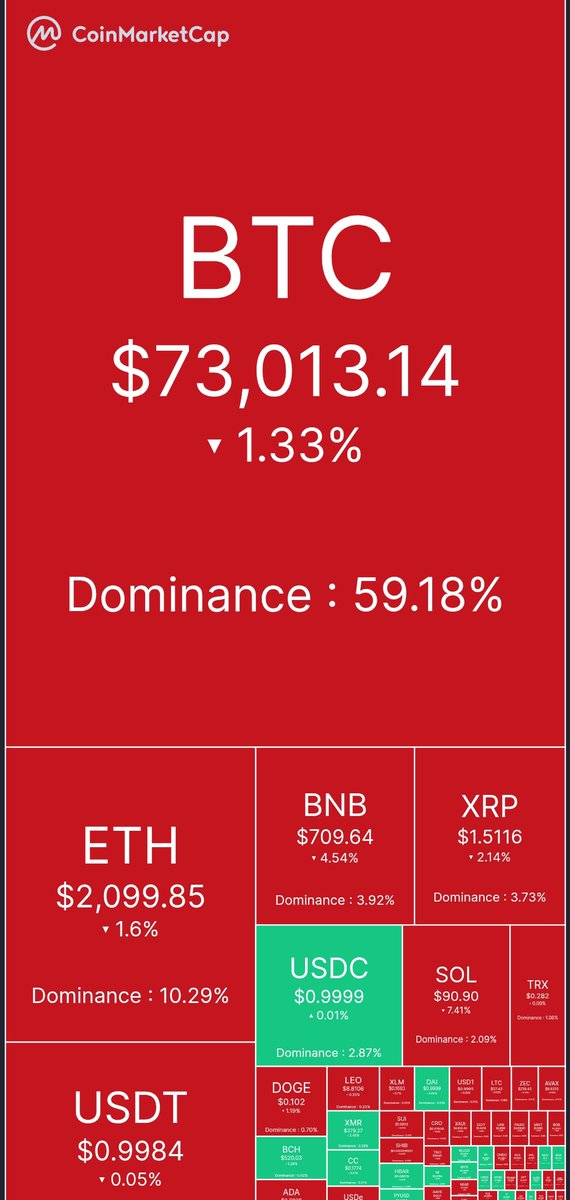
🟥 Red. Red. Red. 🟥 Huge crash in market