Krzysztof Marciniak 리트윗함
Krzysztof Marciniak
248 posts

Krzysztof Marciniak
@__0kami
Security Consultant interested in Reverse Engineering, Binary Exploitation and much more. Co-founder of the Poznań Security Meetup. Coffee++
가입일 Ağustos 2016
234 팔로잉94 팔로워
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함

1/ In one ransomware case, the attackers started an EXE file that dropped the vulnerable GIGABYTE driver to C:\Windows\System\gdrv.sys.
The TA used the vulnerable driver to load a malicious driver as a kernel driver, who hunted and killed Symantec processes. 🧵
#CyberSecurity

English
Krzysztof Marciniak 리트윗함

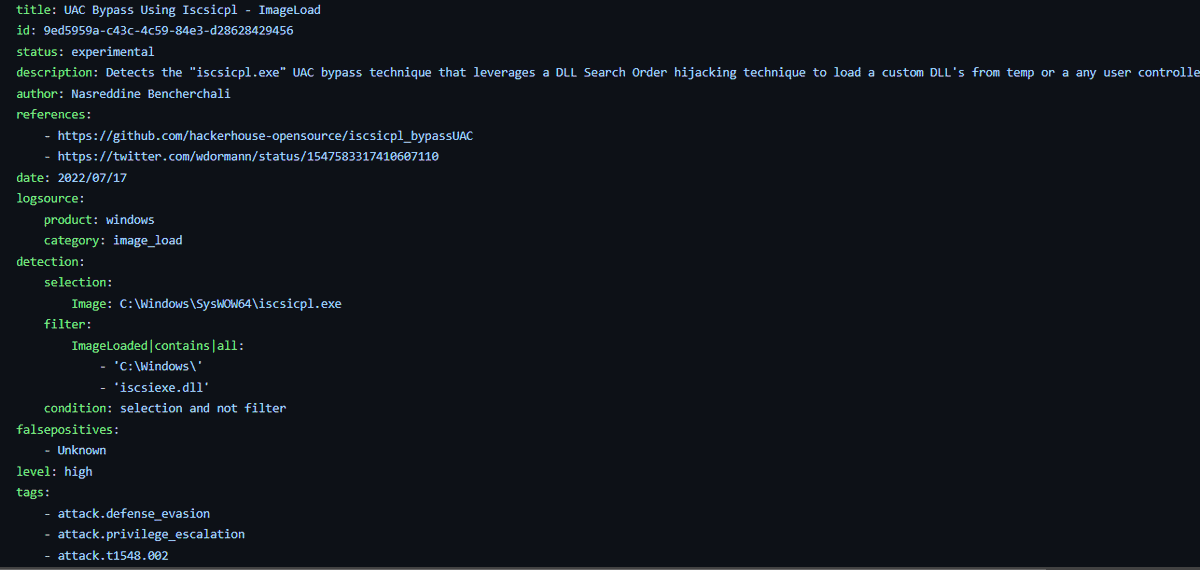
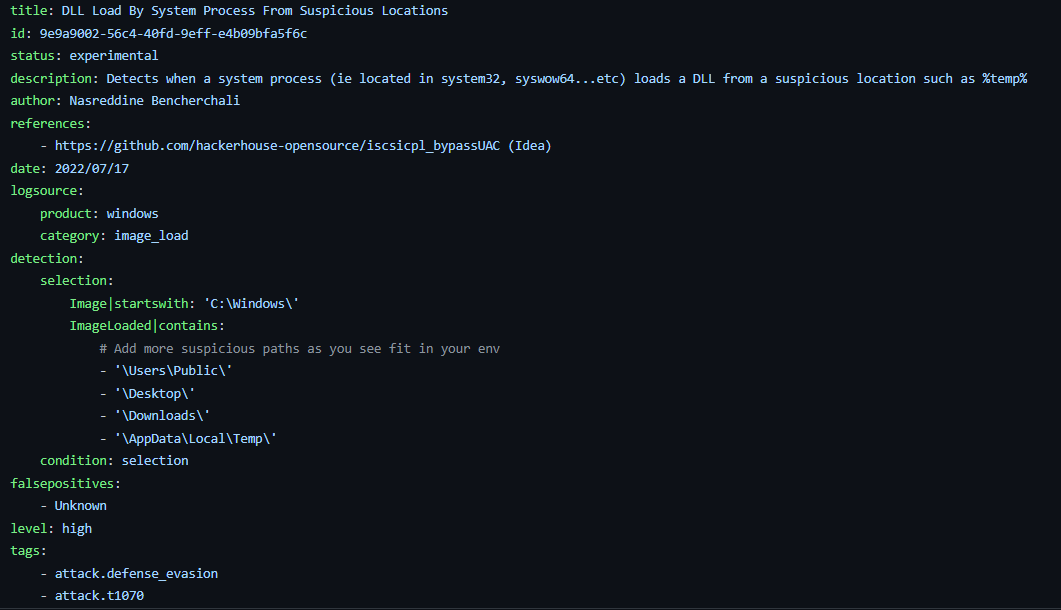
A new Sigma rule to detect this new UAC bypass technique and a generic one to detect DLL side loading were added to the public repo.
LINK - github.com/SigmaHQ/sigma/…
English
Krzysztof Marciniak 리트윗함

At @Mandiant we have put together a vulnerable-by-design Azure Lab to test your red team attacking and blue team detecting capabilities.
Access the lab and instructions here: github.com/mandiant/Azure…
#redteam #blueteam #Azure #azureAD #Pentesting #cloud #cloudsecurity
English
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함

New blog post about an UEFI firmware bootkit!
securelist.com/cosmicstrand-u…
Research was led by our dearly missed @_marklech_
English
Krzysztof Marciniak 리트윗함

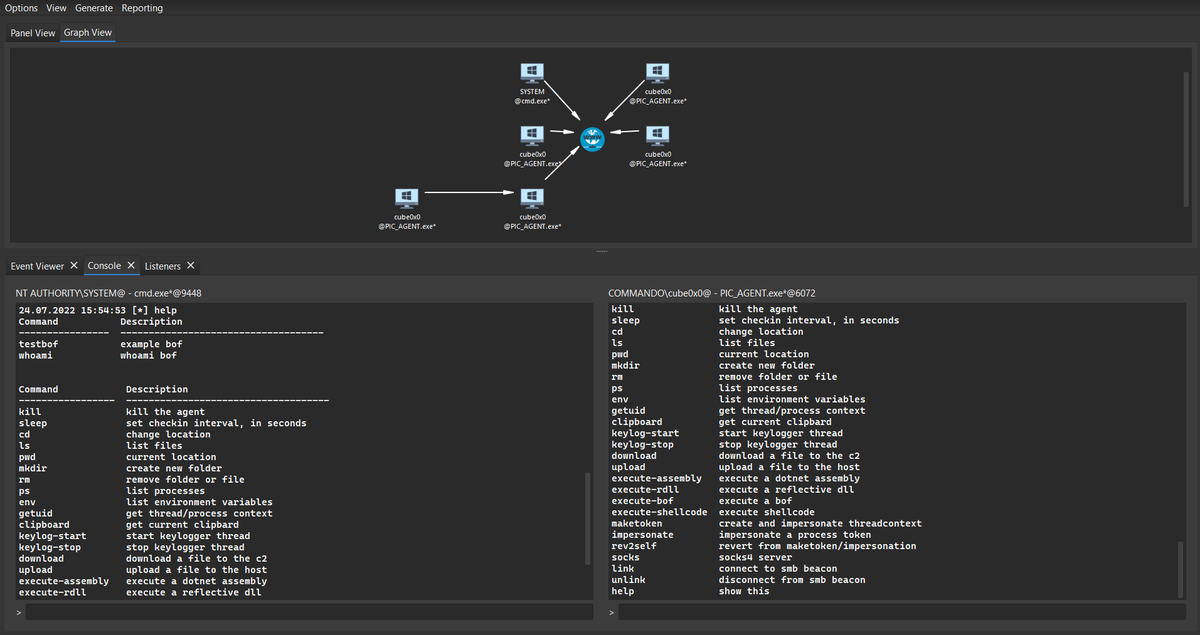
In part 2 of the How I Met Your Beacon series, we look at some strategies for detecting Cobalt Strike mdsec.co.uk/2022/07/part-2… by @domchell
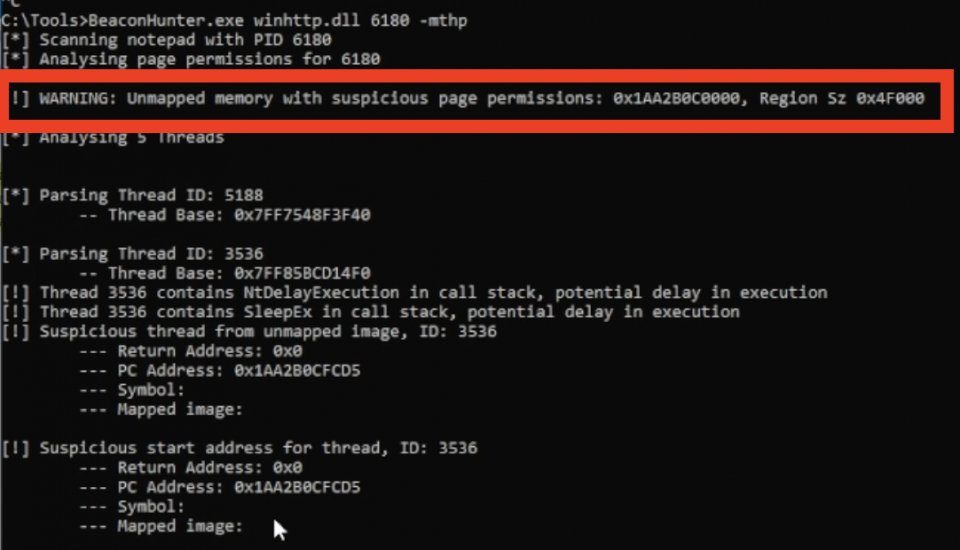
English
Krzysztof Marciniak 리트윗함

🎉 This is a huge feature all orgs should be using. All of my recent M365 IRs (BEC, UNC and APT) have started with the TA registering the first MFA for a dormant 😴 account.
#dfir #microsoft365
Merill Fernando@merill
A neat capability you unlock with combined registration is that you can now use conditinal access policies to control access to this page. For example you can limit MFA config to just trusted devices and locations or block access from countries where you don't have users.
English
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함

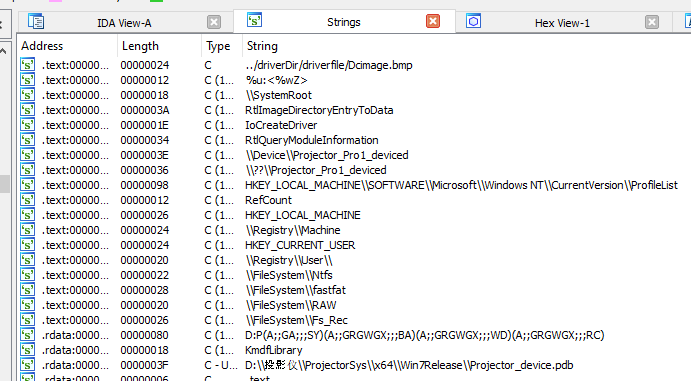
Microsoft signed rootkit #FuRootkit 🌳
Created and submitted in May, still only 4/10
\\Device\\Projector_Pro1_deviced
🧬analyze.intezer.com/analyses/337ed…
🕵️virustotal.com/gui/file/0f5e3…

English
Krzysztof Marciniak 리트윗함

Welcome the new version of Token Universe - an advanced tool for experimenting with Windows security mechanisms! 🎉🌟
It supports viewing, creating, impersonating, and modifying access tokens, spawning processes, and much more.
github.com/diversenok/Tok…
English
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함

Krzysztof Marciniak 리트윗함

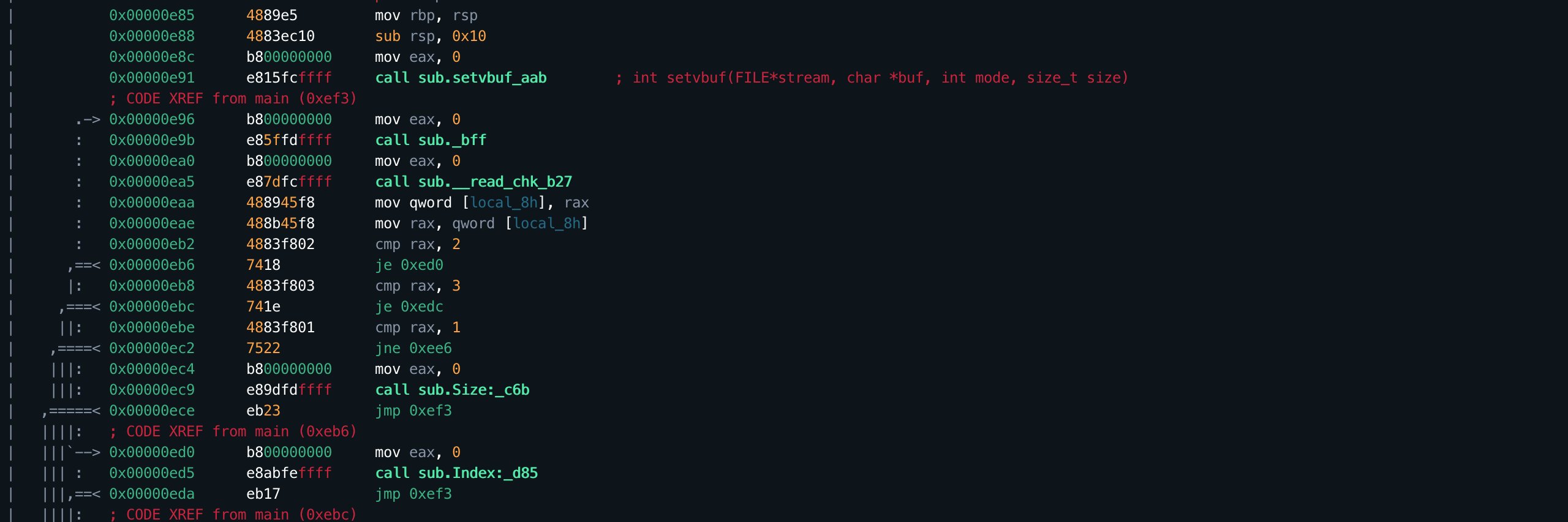
#VMWARE #ESXi OpenSLP heap-overflow CVE-2021-21974 walkthrough + poc
straightblast.medium.com/my-poc-walkthr…
github.com/straightblast/…

English
Krzysztof Marciniak 리트윗함
#over-the-air-baseband-exploit-gaining-remote-code-execution-on-g-smartphones-23199" target="_blank" rel="nofollow noopener">blackhat.com/us-21/briefing… me and @0xKira233 at @BlackHatEvents - @keen_lab

English
Krzysztof Marciniak 리트윗함
Krzysztof Marciniak 리트윗함

I’ve written my first blog post - write-up for CVE-2021-23874! How to enumerate COM-objects attack surface, explore implemented functionality and exploit it the-deniss.github.io/posts/2021/05/…
English