Felix Bilstein 리트윗함
Felix Bilstein
105 posts


Felix Bilstein
@fxb_b
Security Researcher | YARA-Rules for @malpedia using YARA-Signator
Bonn, Germany 가입일 Eylül 2015
551 팔로잉288 팔로워
Felix Bilstein 리트윗함

I have just published a new data set revision of MalpediaFLOSSed, now aggregating 5.6m unique strings gathered from 2.100 malware families. github.com/malpedia/malpe…
Byte Atlas@ByteAtlas
[blog post] MalpediaFLOSSed danielplohmann.github.io/blog/2024/03/0…
English
Felix Bilstein 리트윗함

Felix Bilstein 리트윗함

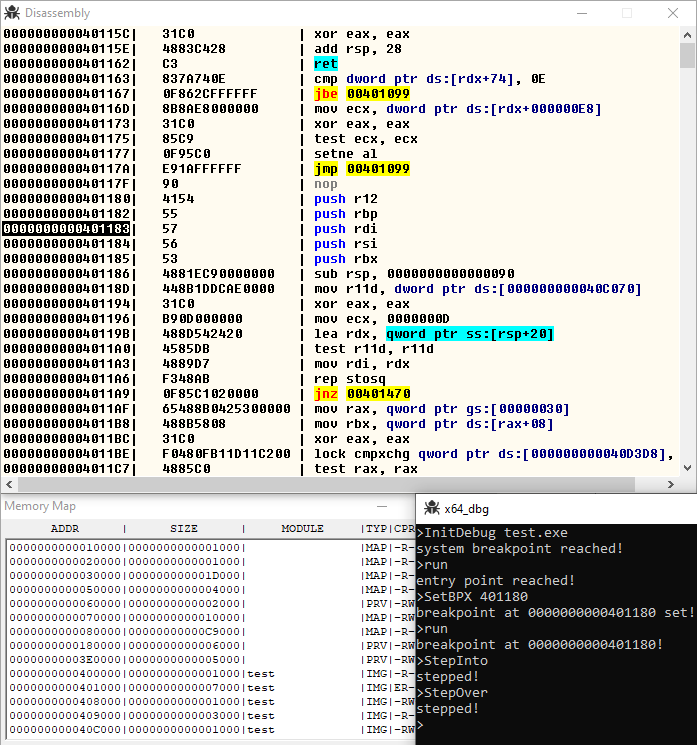
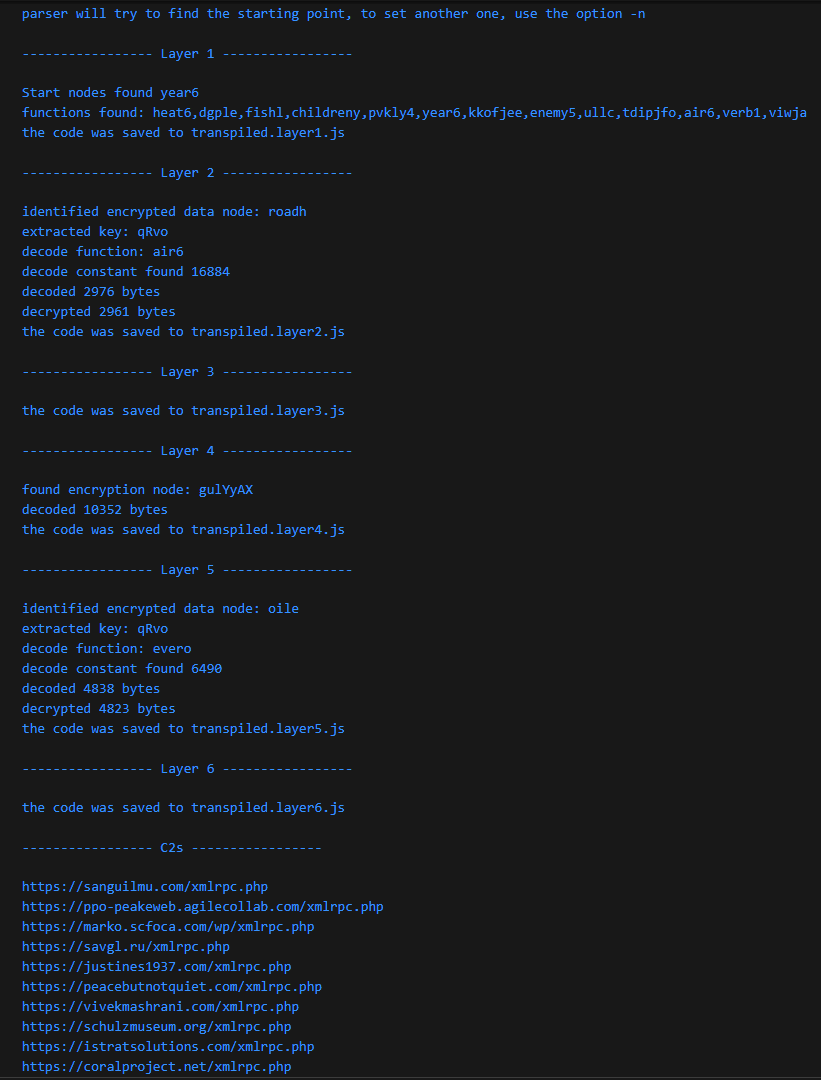
I have spent way too much time on writing this #GootLoader JS unpacker and C2 extractor with abstract syntax tree manipulation. 🌳
But I could not stop at having it half done and this malware has 6 layers.
I am sorry for the terrible code.
github.com/struppigel/hed…

English
Felix Bilstein 리트윗함

Awesome project by malpedia creator @push_pnx presented at VB2023
Applied one-to-many code similarity analysis using MCRIT
Talk:
youtube.com/watch?v=CMu1r5…

YouTube
English
Felix Bilstein 리트윗함

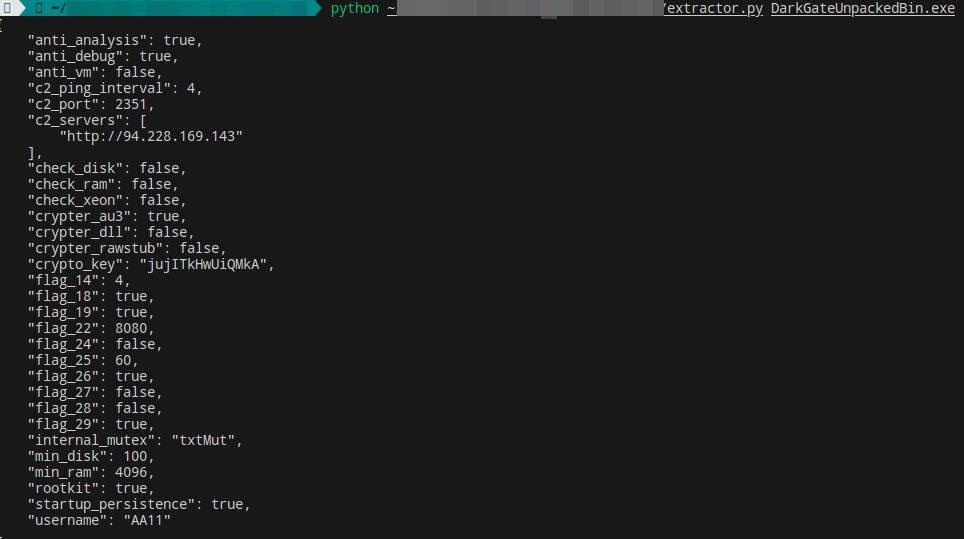
Extractor updated 🎉 Should now support recent #DarkGate samples and can dump complete config and strings. Still some more Ghidra sessions needed to find out what all the new flags do 😂 github.com/telekom-securi…
English
Felix Bilstein 리트윗함

I wrote a blog on new features in the IDA plugin for MCRIT, most notably being able to query basic blocks or the whole currently viewed function against a dataset like Malpedia in mere seconds, making it viable as a live companion while analyzing malware.
Byte Atlas@ByteAtlas
[blog post] Upgraded MCRIT Feature: IDA Plugin danielplohmann.github.io/blog/2023/08/0…
English
Felix Bilstein 리트윗함

@mec314 As a follow-up to my previous response, I have now started populating another Github repo with ready-to-use reference data: github.com/danielplohmann… I'm currently running automated extraction for all available MinGW versions and back-process my MSVC symbols for a first milestone.
English
Felix Bilstein 리트윗함
Felix Bilstein 리트윗함

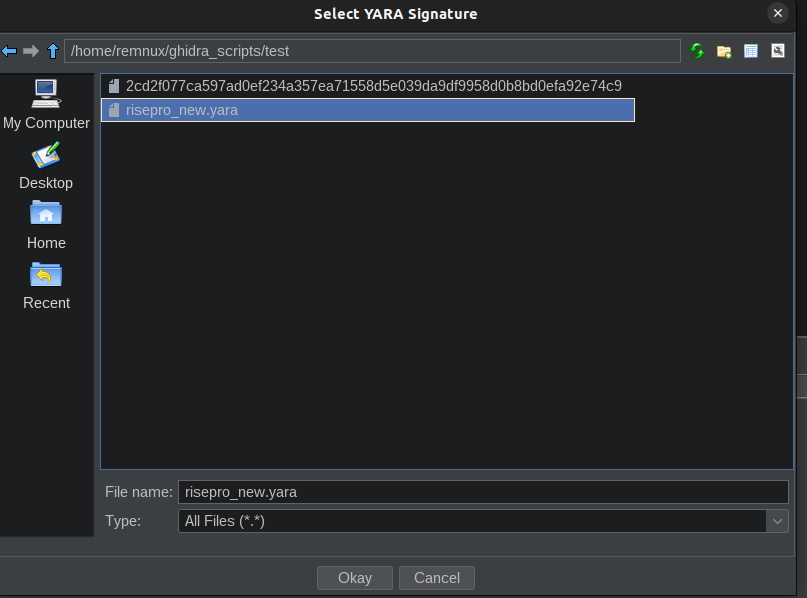
I wrote a tool to find #YARA matches in #Ghidra using #Ghidrathon and Python, get it here! 👇
gist.github.com/c3rb3ru5d3d53c…

English
Felix Bilstein 리트윗함

I wrote a short blog post on MCRIT, the one-to-many code similarity analysis framework that we released as open source recently at @Botconf.
Byte Atlas@ByteAtlas
[blog post] MCRIT: The MinHash-based Code Relationship & Investigation Toolkit danielplohmann.github.io/blog/2023/06/0…
English
Felix Bilstein 리트윗함
Felix Bilstein 리트윗함

After years of hard work, we finally open-sourced Wattson, our research testbed for investigating and analyzing the effects of cyberattacks on power grids: github.com/fkie-cad/watts…
Kudos to @bader_lennart and team @RWTH @Fraunhofer_FKIE @Fraunhofer_FIT
English
Felix Bilstein 리트윗함
Felix Bilstein 리트윗함
Felix Bilstein 리트윗함

I was always searching for a cool open source replacement for the 010 Editor. Since I rarely need it, buying it seemed a waste. But it seems my search is at an end. A colleage just send me github.com/WerWolv/ImHex and the first impression is great!
English
Felix Bilstein 리트윗함

After a great boat ride in the Rhine last night the Forensic Rodeo took place courtesy of the NFI Forensic Rodeo team!
Congratulations to the winning team JimmyThreePockets 🥇🥇
#DFRWSEU2023 #DFIR

English
Felix Bilstein 리트윗함

2023 Global Threat Report - by @CrowdStrike
"2022 was a year of explosive, adaptive and damaging threats. Adversaries continue to be relentless in their attacks as they become faster and more sophisticated."
crowdstrike.com/global-threat-…
#dailydarkweb #cybersecurity
English
Felix Bilstein 리트윗함

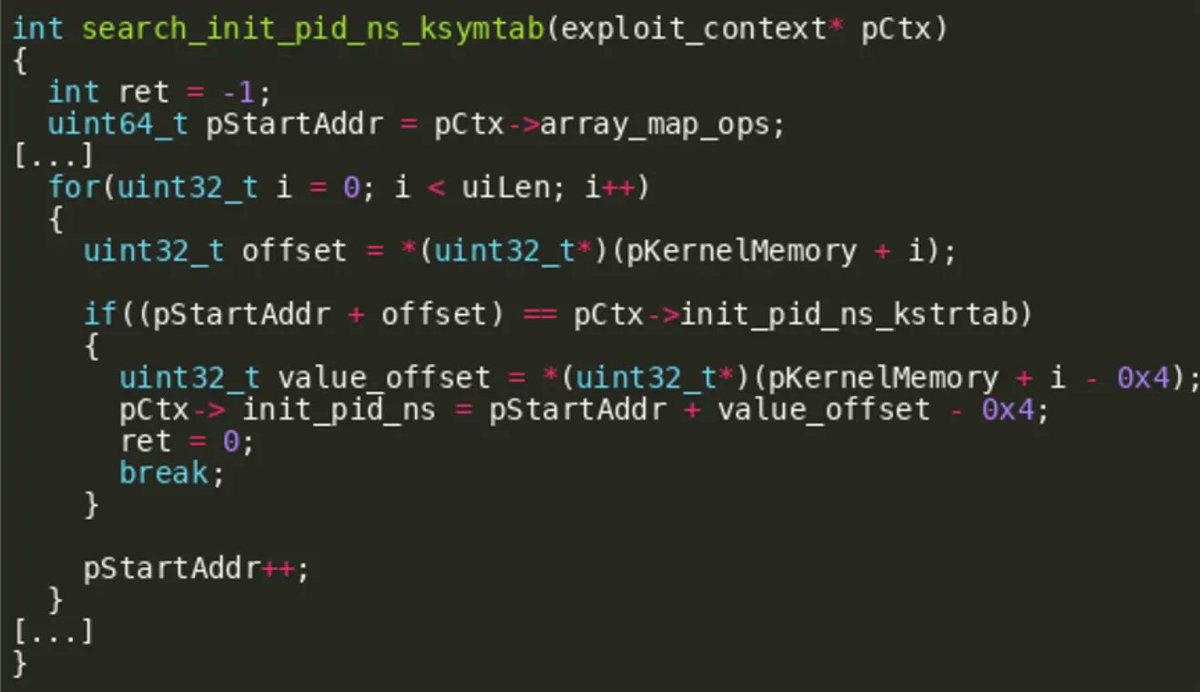
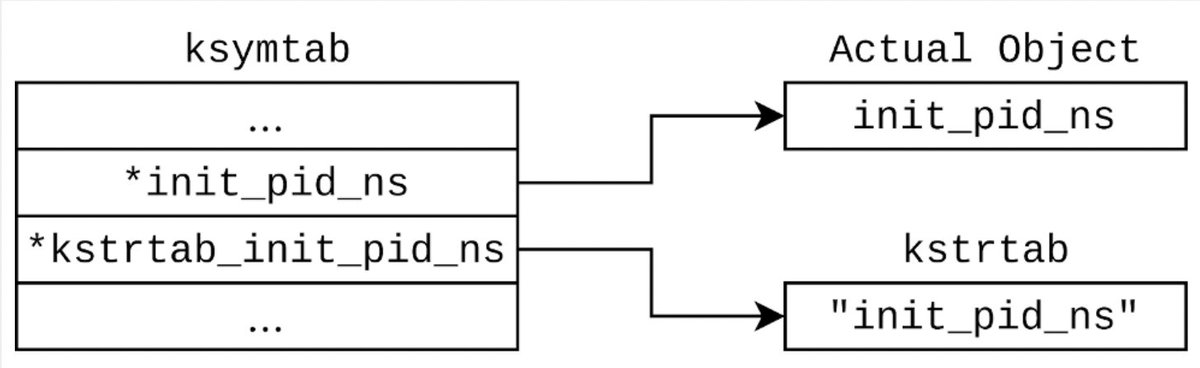
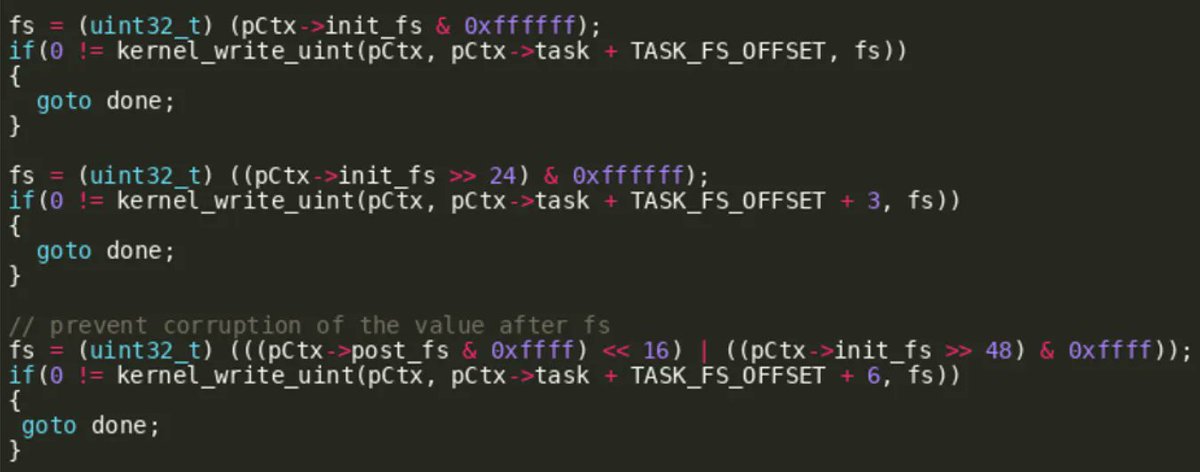
Cool blog post by Karsten König (@CrowdStrike) showing how to modify an existing Linux kernel exploit (CVE-2021-3490) to achieve container escape
crowdstrike.com/blog/exploitin…
English
Felix Bilstein 리트윗함

[THREAD] Finding the real IP of a Cloudflare-hidden website has always been challenging. There are interesting tools out there such as fav-up, written by @noneprivacy, which leverages Shodan to find the real IP address via a favicon lookup. However, you can often find the IP...
English