LiteLLM (YC W23) 리트윗함

📣 Announcing @LiteLLM's April Townhall
Agenda:
- Product roadmap
- Reliability and security updates
- Open Q&A with the team
Register here: forms.gle/zyyHLhHEyWGo1A…

English
LiteLLM (YC W23)
976 posts
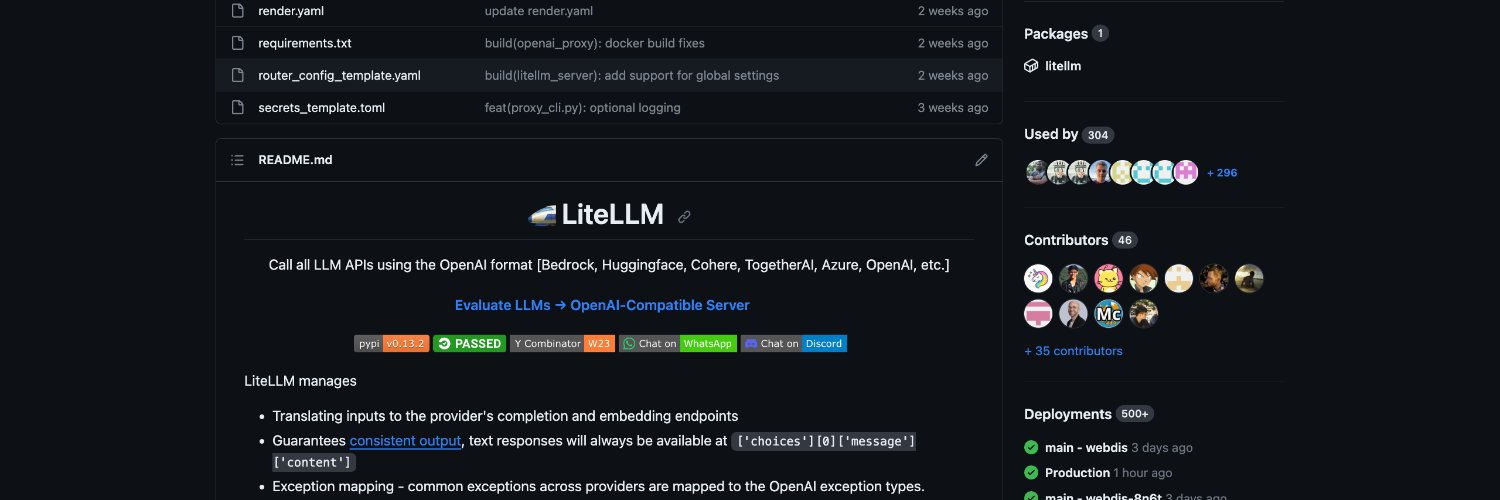

@LiteLLM
Call every LLM API like it's OpenAI 👉 https://t.co/UV2PpapQo7





@archiexzzz More customer data leaks: Amazon, Athena, Aphrodite, Meta, Apple… Athena and Aphrodite are code names






@IceSolst Crowdstrike only disclosed trivy 1/2 day after they had been analyzed by third parties, socket marked our litellm packages as clean, both releases and claim their dependency scanners could have prevented it. Everyone affected know the counter playbook, none are applying it.

TeamPCP supply chain campaign scope expanded beyond initial reports with new CISA KEV entry and detection tools now available. Campaign timeline spans Feb 28 initial access through March 24 LiteLLM PyPI compromise. #DFIR_Radar






