Sam Sanoop 리트윗함

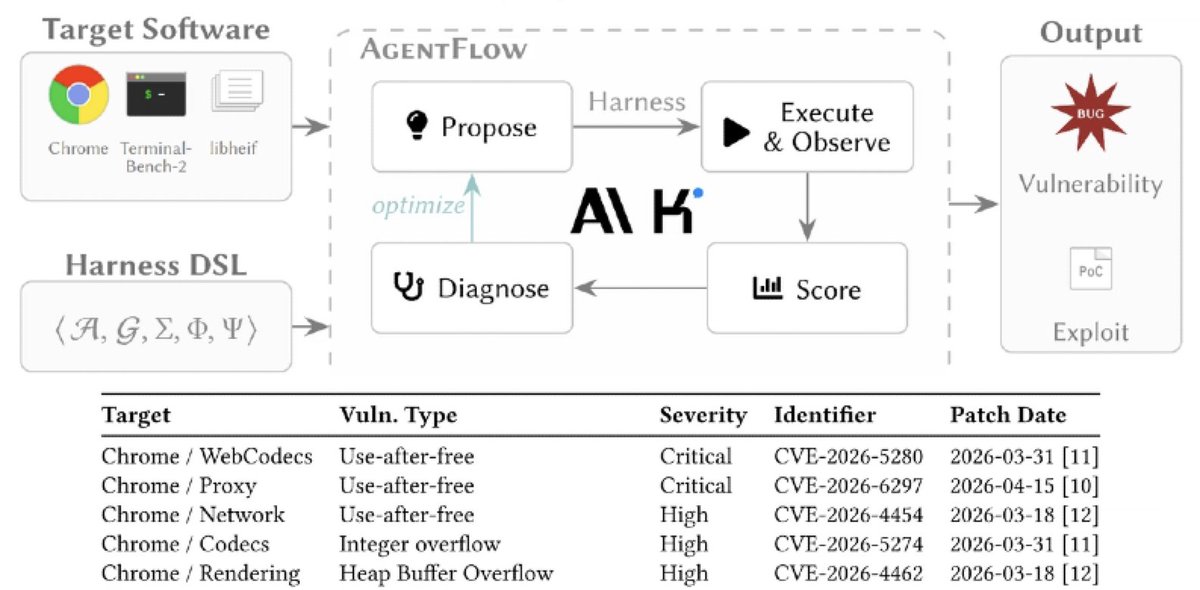
Tomorrow, we’re releasing the full technical walkthrough for CVE-2026-5865, a chrome v8 0-day found by our AI security agent "Vega".
More Linux kernel and Chrome 0-day writeups are coming later this month. Stay tuned, and follow our bug list for updates: nebusec.ai/buglist/
English