Network23 retweetou

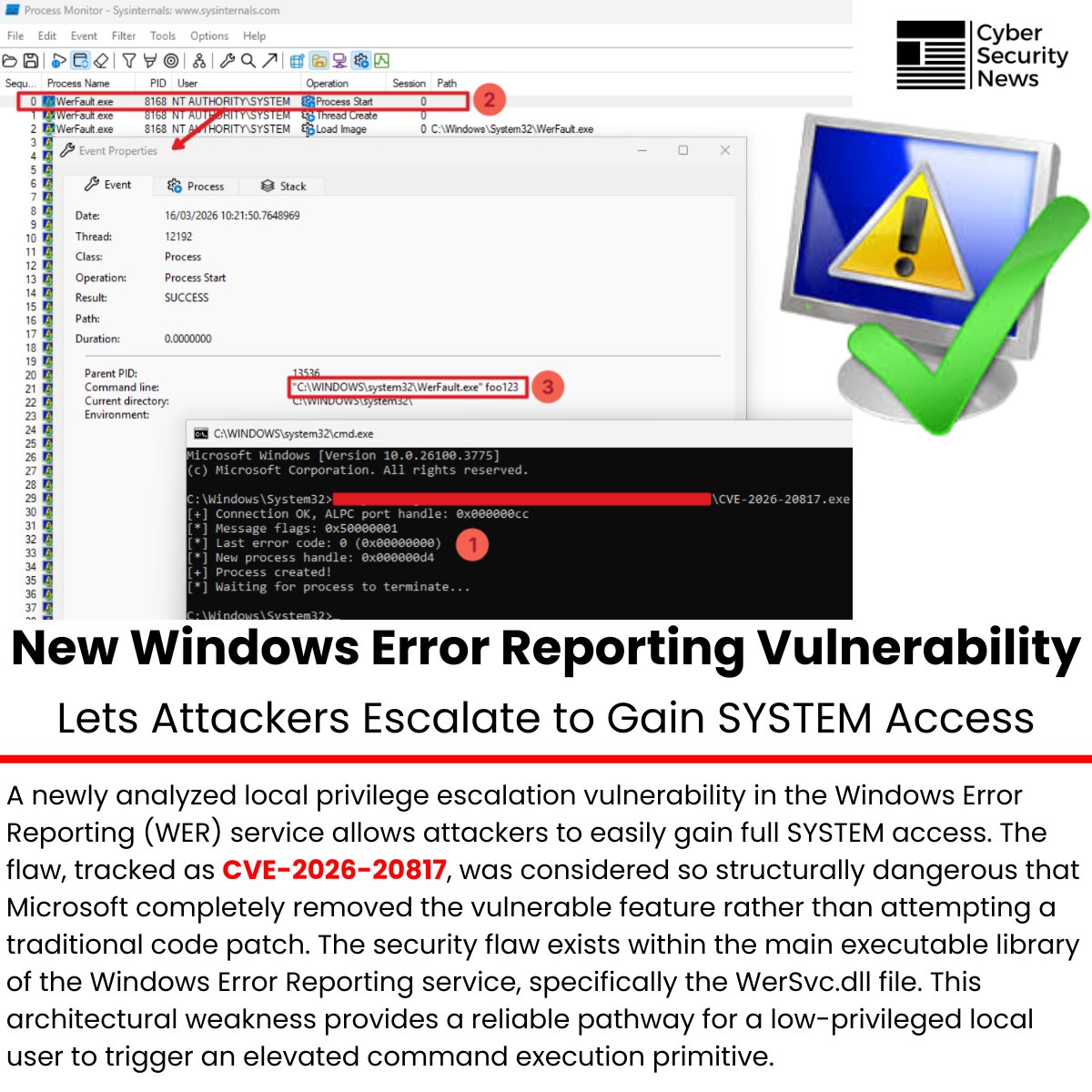
🛡️ New Windows Error Reporting Vulnerability Lets Attackers Escalate to Gain SYSTEM Access
Source: cybersecuritynews.com/new-windows-er…
A newly analyzed local privilege escalation vulnerability in the Windows Error Reporting (WER) service allows attackers to easily gain full SYSTEM access.
The flaw, tracked as CVE-2026-20817, was considered so structurally dangerous that Microsoft completely removed the vulnerable feature rather than attempting a traditional code patch.
The security flaw exists within the main executable library of the Windows Error Reporting service, specifically the WerSvc.dll file. This architectural weakness provides a reliable pathway for a low-privileged local user to trigger an elevated command execution primitive.
#cybersecuritynews
English