تغريدة مثبتة
Aurélien Chalot
1.6K posts


Aurélien Chalot
@Defte_
Hacker, sysadmin and security researcher @OrangeCyberdef 💻 Calisthenic enthousiast 💪 and wannabe philosopher https://t.co/SqDDhIGGGh 📖 🔥 Hide&Sec 🔥
The grid انضم Kasım 2017
475 يتبع4.2K المتابعون

@SinSinology @thatjiaozi I'll open a farm next to you guys to provide cereals and milk if that's okay 🤣
English

@thatjiaozi pastries, cookies, breads with me
cinnamon buns too
English
Aurélien Chalot أُعيد تغريده

Stealthy WMI lateral movement - StealthyWMIExec.py
ghaleb0x317374.github.io/2026/03/15/Ste…
English
Aurélien Chalot أُعيد تغريده

Releasing one of my research tools: EVENmonitor🖥️
Inspired by LDAPmonitor, I implemented a monitoring tool for the Windows Event log in pure python. You can just attach it via the network and then filter for specific event IDs or keywords.
Available at: github.com/NeffIsBack/EVE…
GIF
English
Aurélien Chalot أُعيد تغريده

New post on the MDSec blog and another Windows EoP....
RIP RegPwn - mdsec.co.uk/2026/03/rip-re…
Saying goodbye to a much loved EoP, by @filip_dragovic
English

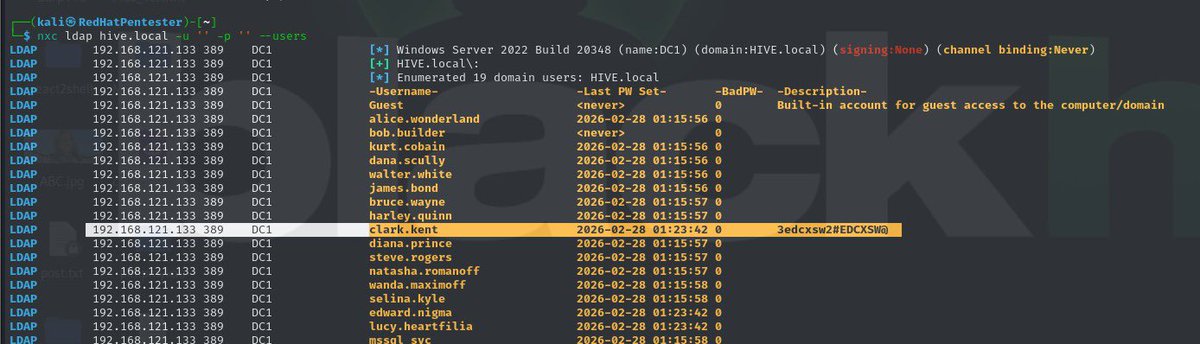
@sekurlsa_pw @RedHatPentester So from a low priv user you can determine if a PSO exists and which users it applies to but you can’t see the policy details. W/ a DA acct you can see policy details. If I see a PSO I just refuse to spray any users that it applies to unless the client will tell me the details
English

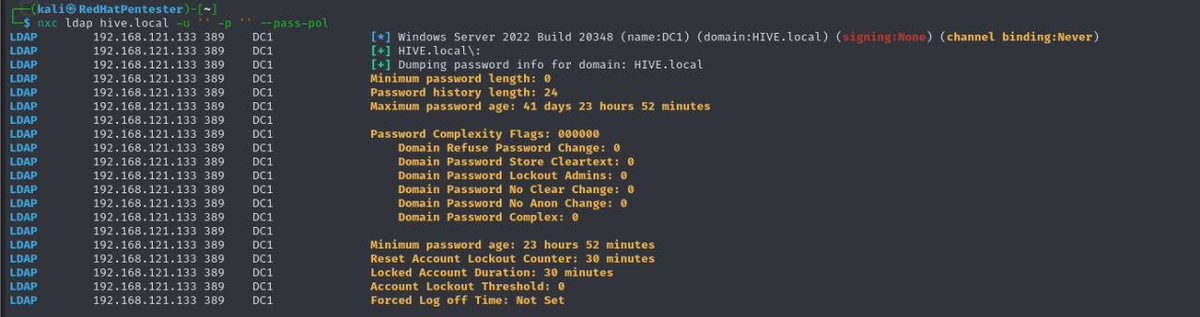
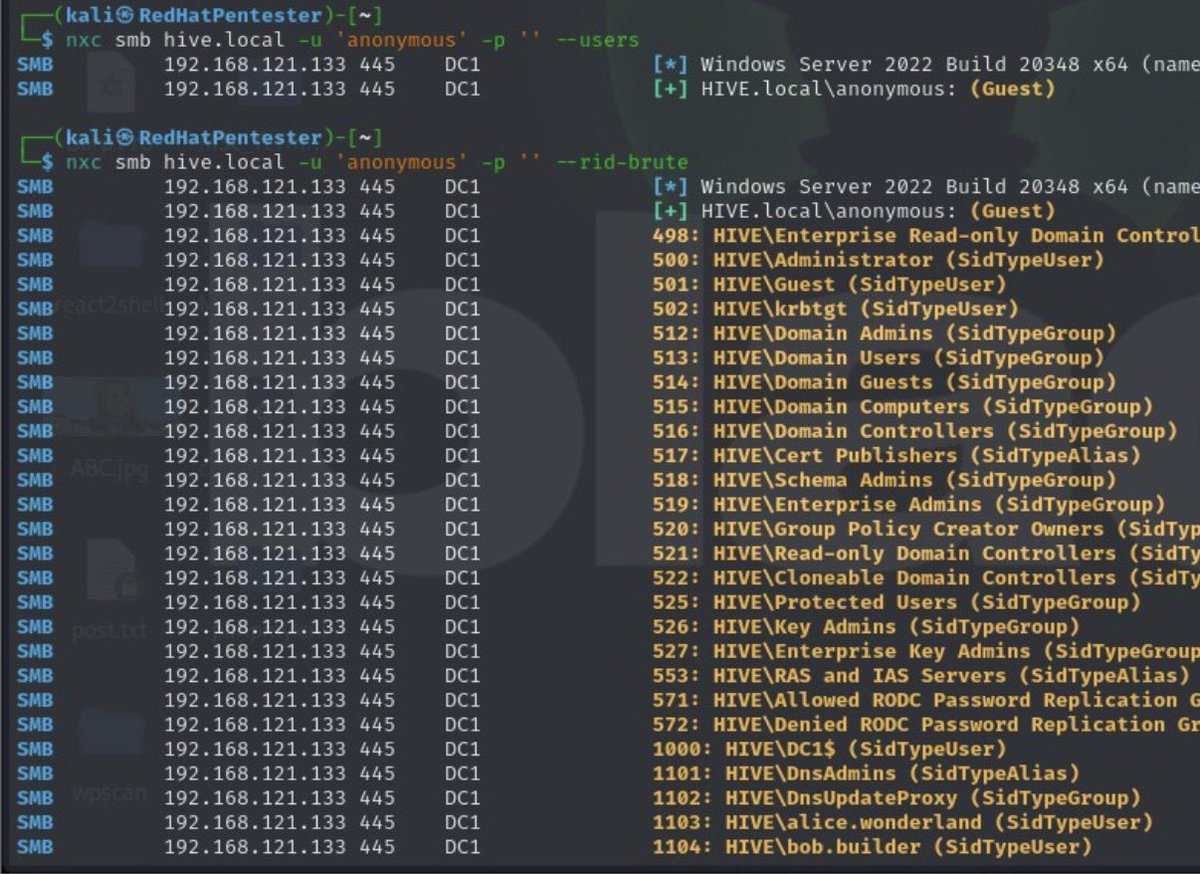
If a pentester ignores the password policy and performs password spraying blindly, they may unintentionally lock multiple user accounts. This can disrupt business operations and immediately alert system administrators to suspicious activity. For example, if the policy locks accounts after five failed login attempts, spraying several passwords too quickly across many accounts could trigger a mass lockout event.
By reviewing the password policy first, the penetration tester can design a controlled and stealthy spraying strategy. Knowing the lockout threshold allows the tester to limit attempts to safe numbers and space them out over time.
English

@unsigned_sh0rt @Sniffler0x1 Omg thank you so much dude 🥳! That's exactly what I was looking for!!
English

@Defte_ @Sniffler0x1 I'm re-reading the thread and realizing the perspective you're coming from now.
In SCCM you can enable a setting to not automatically approve unknown clients.
You can also define boundary groups for new clients which gives your some granularity on approval.
English

@unsigned_sh0rt @Sniffler0x1 But what prevents a random non domain joined computer to enroll on the MP via the self signed certificate and then get the NAA ?
English

@Defte_ @Sniffler0x1 initially it's a self-signed certificate (or PKI if they have AD CS setup) that's used by the client to start the enrollment process with the management point
management point sends the NAA, NAA gives access to shares
English

@Sniffler0x1 and ultimately, how ehttp fixes the problem ? There's no more NAA account but I don't get how the DP knows that a non domain joined account can authenticate and be provisionned. I should just read more documentations I guess D
English

@Sniffler0x1 So the real question I have got, is why would that account be spread via the HTTP endpoint. If the computer is not domain joined, it cannot reach that endpoint anyway.
But yeah, if the computer boots via PXE, then the password is used to reach the AD
English

@ShitSecure Found some reasons althought I still don't get why that mechanism even exists xD
English

@ShitSecure Is this some kind of a legacy issue as we see everyday in the windows world ? ahah
English

@sama How can you even trust AI won't be misused by dow when your country is run by a fool crying on twitter when Anthropic refused the deal ? "Communist leftist" whatever bullcrap this is. The guy broke every rules but still you manage to believe he won't break your terms ?
English
Aurélien Chalot أُعيد تغريده

Discovered 2 RCEs in Unitree Go2 with @ruikai. CVE-2026-27509 is unauth'd over DDS. CVE-2026-27510 is the same sink, different source. Dropped the 32-minute technical writeup from unboxing to shells. Hope you enjoy the read! ❤️ boschko.ca/unitree-go2-rce
English

I hacked Claude Code! It turns out "agentic" is just a fancy new way to get a shell. I achieved full RCE and hijacked organization API keys. CVE-2025-59536 | CVE-2026-21852
research.checkpoint.com/2026/rce-and-a…
#ai #Claude
English