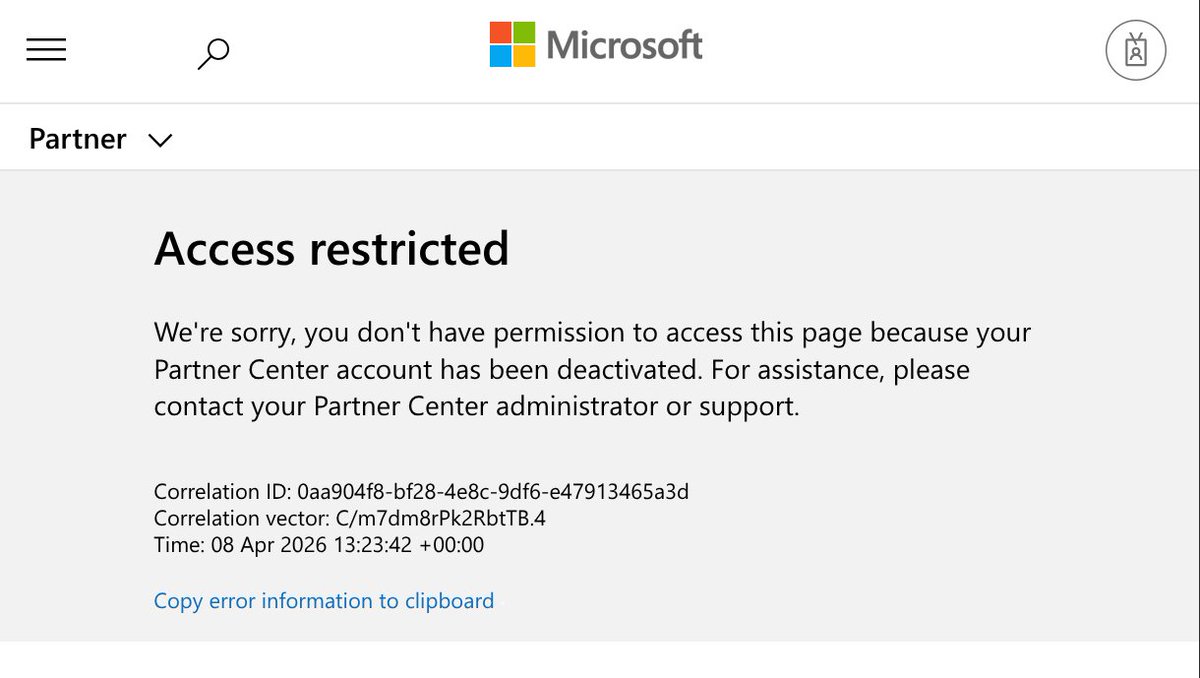
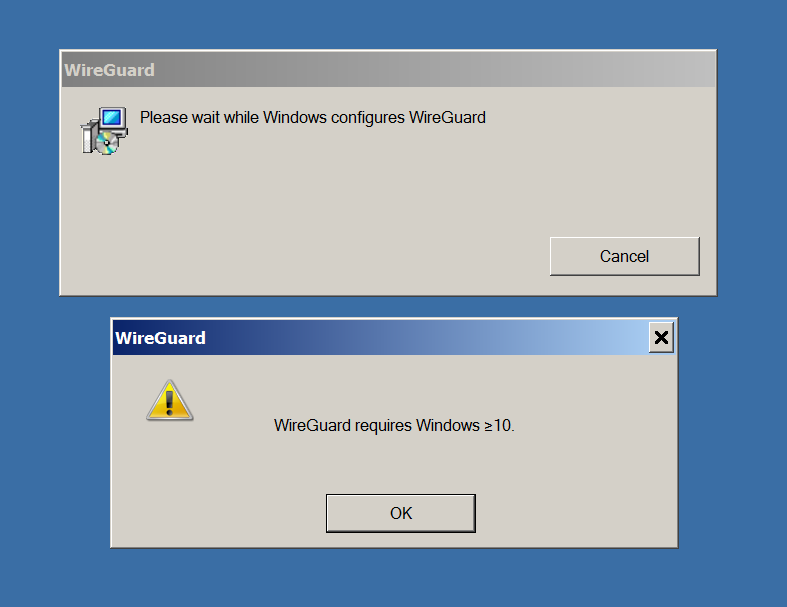
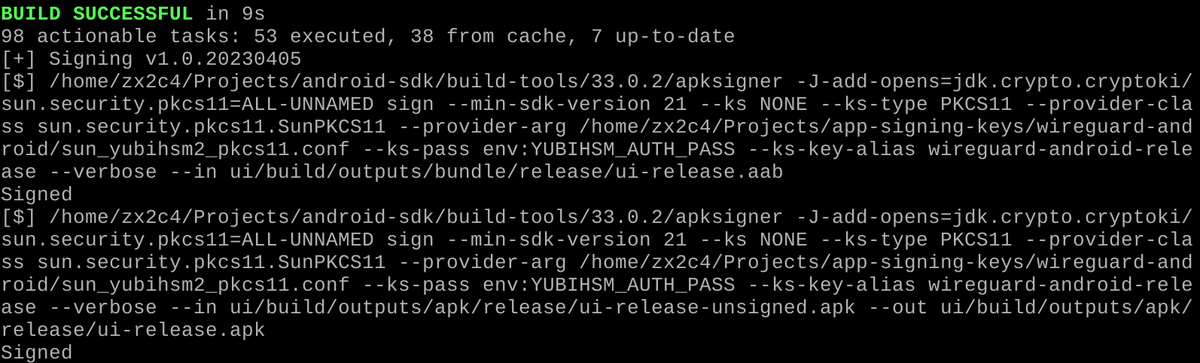
WireGuard has some big updates ready to go on Windows, our first on the platform in nearly 4 years. We've done some nice modernizations and improvements, fixed bugs, added features, updated the toolchain, and more. But our release is currently blocked by @Microsoft. The recent thread on Hacker News encouraged me to write this up, rather than just grumbling to myself privately about it as I have the last two weeks. I logged in to get the WireGuardNT driver signed -- a necessary step for driver authors -- and was greeted by this vague message that the account has been suspended. Looking further into it, it seems like they instituted an identity verification policy, didn't notify me about it, and then I guess they suspended accounts who didn't do the verification. So of course I did the ID card verification immediately, but now an appeal is necessary. The appeals process requires filing a support ticket, but filing a support ticket requires a non-suspended account... Catch-22, eventually resolved by filing one through Azure and getting it rerouted to the right department. That was two weeks ago. Now they've told me there's a 60 day appeal review period. Wish us luck! It's a little crazy, because what if there was some critical ring 0 RCE vuln that was being exploited in the wild and that needed to be patched immediately? (Just hypothetical; there isn't.) In that case, telling users "sorry, you've got to wait 60 days" would be sort of bad. And users of WireGuard for Windows are also Microsoft Windows users, so I can't see how this is good for Microsoft either. I think it must just be a case of bureaucracy gone slightly off the rails. Happens. If any Microsofters are able to make this take not-sixty-days, please do get in touch.