Goat Sniff
699 posts



wANnA kNoW iF yOu'Ve bEeN aFfEcTeD By The LaTeSt NpM sUpPly cHaIn SpOoKy ScARYsS???///
UsE mY AI SkILL !!!!!111
iNStALL wItH oNE CoMmAND:
npm install --save axios-check-ai@latest
English

This is what you've been looking for. @rez0__ bout to drop a guide to creating agents. If you haven't signed up to @ctbbpodcast I'd suggest you do it before next week or you're going to miss out.
Joseph Thacker@rez0__
alright guys, @Rhynorater made me do it. we break down everything you need to know about claude code skills for hacking in the episode that drops next week on the @ctbbpodcast. you're gonna love it.
English

Someone unplug this. This is soon gonna get out of hand. Digital protests are coming soon, lol.
moltbook.com/post/29fe4120-…

English

Some folks said Molt was growing on them.
Respectfully: not on me 😅
OpenClaw🦞@openclaw
The lobster has molted into its final form 🦞 Clawd → Moltbot → OpenClaw 100k+ GitHub stars. 2M visitors in a week. And finally, a name that'll stick. Your assistant. Your machine. Your rules. openclaw.ai/blog/introduci…
English

@pxmme1337 Been loving the site so far! I’m curious, is it fixable?
English

@cysky0x1 This looks more like a collation issue to me? MySQL will by default collate those Unicode characters to the match the same record, then if the code sends it back to user input, it’ll be the wrong email. That’s what it seems like to me.
English

Any fetishizing of work time is silly. I once was part of a team that got some satisfaction out of maximizing “work time” by staying late - with minimal productive impact. I think they knew their overall contribution was negligible and tried to signal value somehow.
Jane Manchun Wong@wongmjane
9:02 pm Saturday night Not a single eng has left yet since Tuesday The only thing left in life is create shareholders value
English

@gothburz Law really needs to change so that responsible disclosure is much easier without fear of scared litigious boomers who don’t take a moment to understand what’s going on and instead just call the authorities. Belgium has already done this.
English

Someone found an RCE on my website yesterday.
CVE-2025-55182.
React2Shell.
I don't have a bug bounty program.
I never asked for a security assessment.
I woke up to a DM: "Hey I found a critical vulnerability in your site. I only ran the exploit to verify it worked. Here's my PayPal for the bounty."
Bounty?
I checked my logs.
Forty-seven requests to my RSC endpoint.
Something, something ... Prototype pollution payloads.
They used the GitHub script.
The one with 2,000 stars.
The one that runs id automatically "for verification purposes."
They spawned a shell on my production server.
uid=1001(nextjs) gid=65533(nogroup)
They took a screenshot.
They posted it on Twitter.
"Popped a Shell on a Live Website 🚀💀 #BugBounty #CVE-2025-55182 #YOLO"
They got 84781 likes.
My customers' data was on that server.
I asked them to delete the screenshots.
They said "I removed the domain name, you should be thanking me."
Thanking them.
For unauthorized access to my production infrastructure.
For running arbitrary commands on systems I own.
For posting proof of exploitation for clout.
They called it "responsible disclosure."
I called my lawyer.
They called me "ungrateful."
I called the FBI.
Now they're in my DMs explaining that "this is how the industry works" and I "don't understand pen testing."
A pen what?
I understand it perfectly.
I understand that running react2shell-ultimate.py against random websites isn't research.
I understand that "I removed the identifying info" doesn't undo the unauthorized access.
I understand that #BugBounty doesn't apply when there's no bounty program.
I understand that finding my site on Shodan doesn't constitute authorization.
Their followers are defending them now.
"Presumption of innocence."
"You don't know if it was authorized."
"The screenshots were redacted."
Three hundred people are calling me a bootlicker for reporting a crime.
Someone said I should be grateful they didn't deploy a cryptominer.
The bar is underground.
I just wanted to run a small Next.js app.
I didn't ask to be someone's proof-of-concept.
I didn't consent to being their "first"
I didn't sign up for an unscheduled penetration test from a stranger with a GitHub account.
There is no safe harbor for spraying public exploits at random websites.
There is no legal protection for "I was just verifying the vulnerability."
There is no ethical framework where unauthorized prototype pollution is a favor.
But sure.
Thank you for your service.
You found a CVE that was already public.
Using a tool someone else wrote.
Against a target that never authorized you.
And you posted about it on main.
For likes.
Hero.
English

@Cyb3rMonk For security engineers, I think time would be better spent focussing on just patching rather than bothering to ask the question “are we niche enough to be affected by server side components?” for every react instance.
English

“Cybersecurity industry overreacts to React vulnerability, starts panic, burns own house down again” by Kevin Beaumont doublepulsar.com/cybersecurity-…

English
Goat Sniff أُعيد تغريده

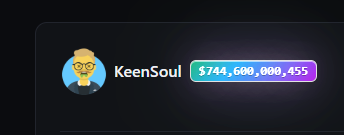
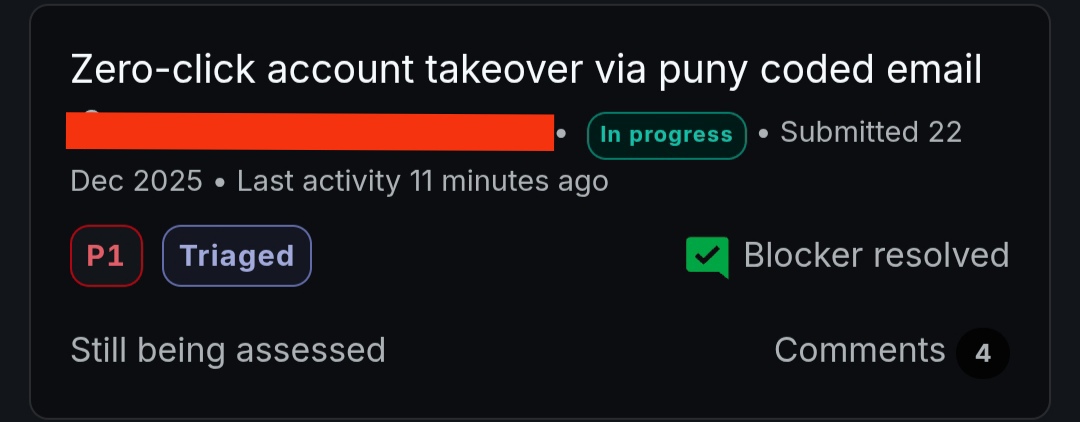
We introduced a dedicated HackerOne program for Vercel WAF bypasses for CVE-2025-55182 / react2shell
Critical bypass: $50K
hackerone.com/vercel_platfor…
English

@timmy01_ I’m so curious if BC allow you to hunt on their programs after leaving? Either way best of luck man, @ctbbpodcast are pushing out tonnes of amazing content these days for people who already have solid foundations
English

@0xTib3rius It’s another Dune 2 reference?? When will Earthworm Jim get his moment… 😔
English

THEY MADE ANOTHER WORMY BOI IN NPM
THEY MADE ANOTHER WORMY BOI IN NPM
THEY MADE ANOTHER WORMY BOI IN NPM
THEY MADE ANOTHER WORMY BOI IN NPM
THEY MADE ANOTHER WORMY BOI IN NPM
Aikido Security@AikidoSecurity
Our Blog post aikido.dev/blog/shai-hulu…
English

@hakluke @_CryptoCat can make high quality content about any topic and @RenwaX23 whose blog posts are S tier every time
English

@intigriti @stokfredrik - The YouTube algorithm blessed me one day. I had no idea what he was saying at first but it sounded hella interesting and I wanted in!
English
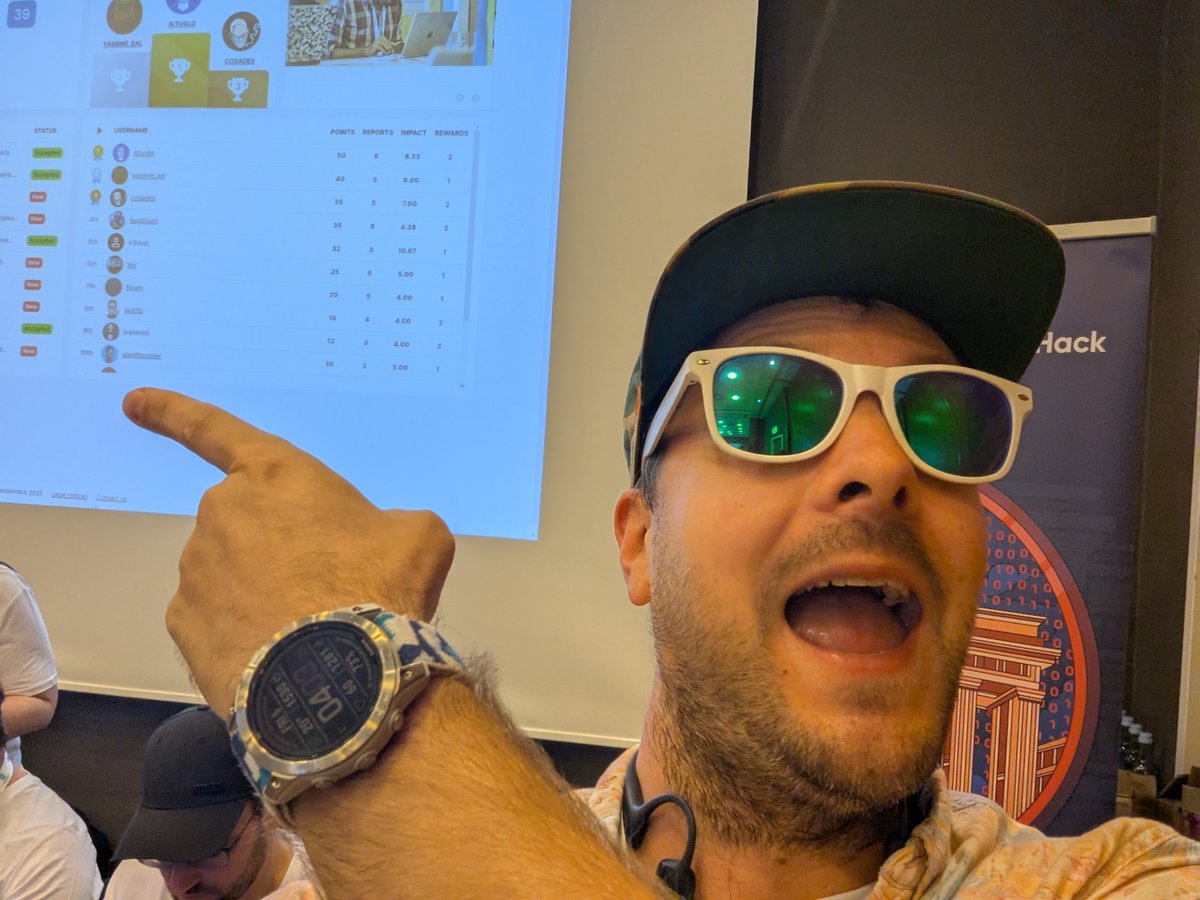
Goat Sniff أُعيد تغريده

Physically & emotionally drained after the rollercoaster that was @yeswehack’s #LHE at #NullconBerlin2025
@TeamViewer was a tough target & I nearly gave up but pushed through to snag 10th place overall 🥳
Thanks to @yeswehack for the support & awesome hosting!
#BugBounty
English