Interstellar
2.5K posts


Interstellar
@Interstellarx22
$ETH Telegram: https://t.co/CJ4cwNnGf9




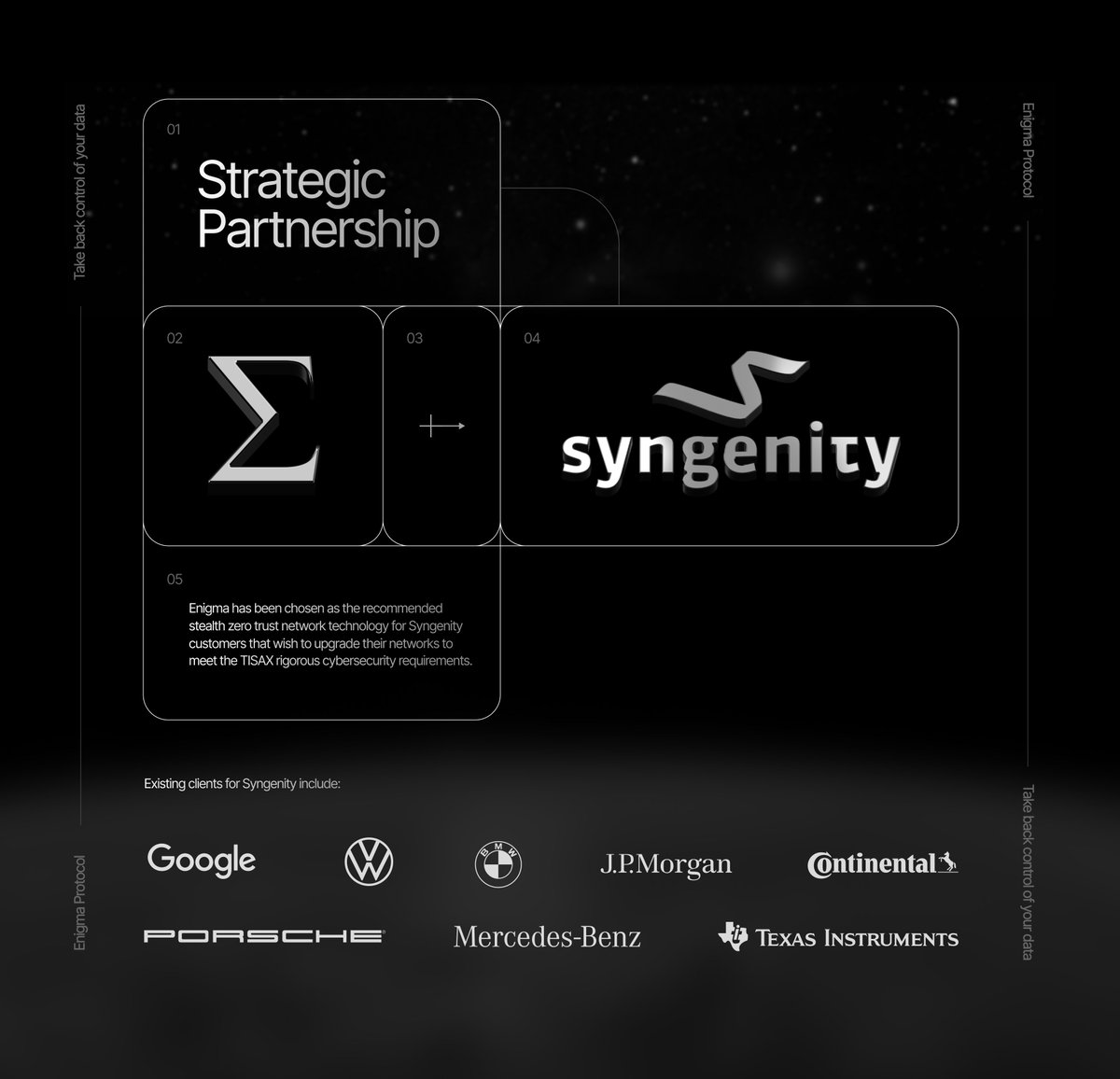
We are proud to announce that Enigma has partnered with Syngenity, a global leader in TISAX consulting, an elite cybersecurity standard for the global automotive industry. Enigma will work with customers that wish to upgrade their networks to meet the rigorous TISAX cybersecurity requirements related to zero trust network access. Existing clients for Syngenity include: Google J.P. Morgan Mercedes-Benz BMW Volkswagen Texas Instruments Continental $ENX












Ethereum is for quantum resistance.
I am excited to announce my upcoming trip to Tel-Aviv, where I have been personally invited to join the Global CISO panel as a speaker representing Enigma at the 2026 Cybertech Global Conference. The discussion will primarily revolve around Al governance, national cyber resilience, and the deployment/expansion of Enigma. cybertechisrael.com/speakers $ENX



I am excited to announce my upcoming trip to Tel-Aviv, where I have been personally invited to join the Global CISO panel as a speaker representing Enigma at the 2026 Cybertech Global Conference. The discussion will primarily revolve around Al governance, national cyber resilience, and the deployment/expansion of Enigma. cybertechisrael.com/speakers $ENX
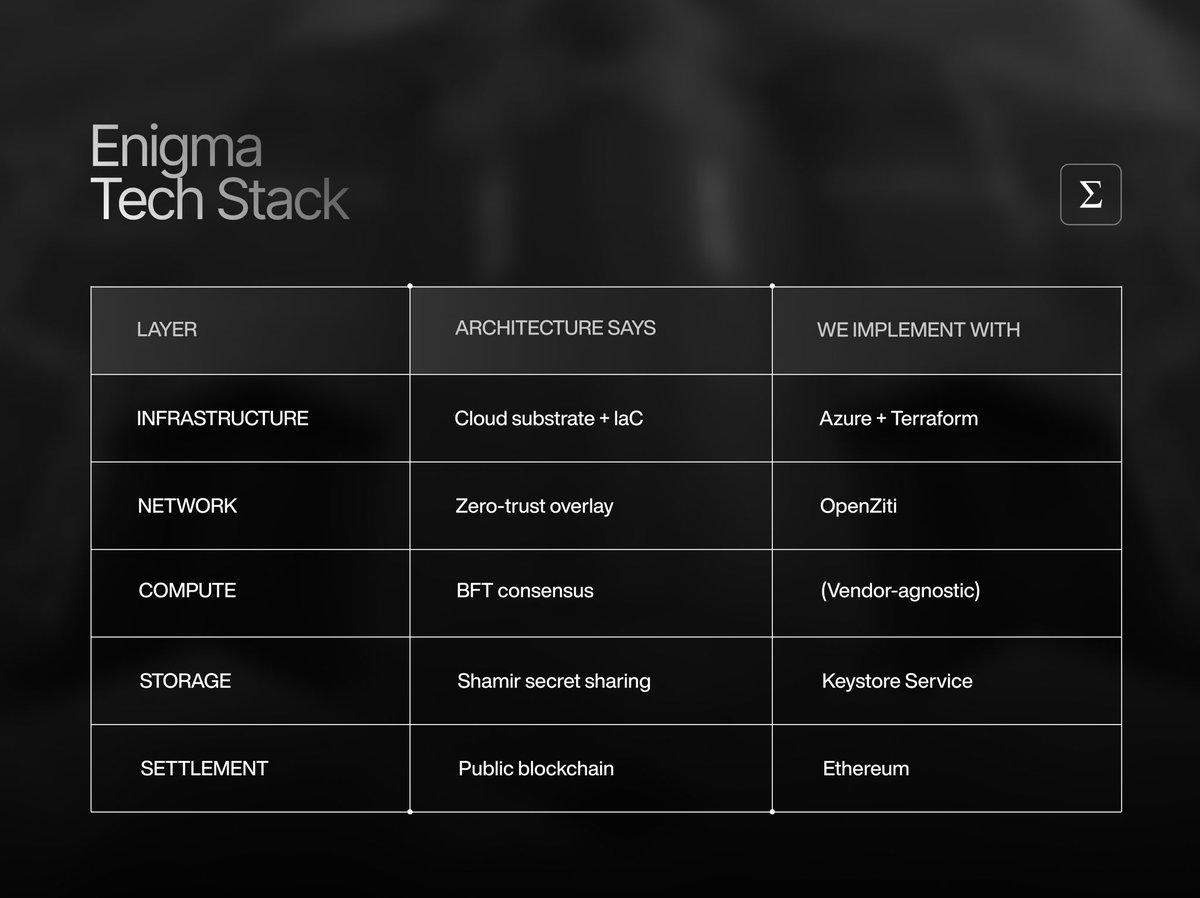
Not all risk lives on-chain. Supply chains, payments, defence systems, and enterprise data flows all fail when relationships and movement become visible. Our RAVID infrastructure can secure off-chain, real-world systems by removing network observability, especially where exposure equals catastrophic risk. $ENX