ShoveTime
11K posts


ShoveTime
@ShoveTime
Used to Gamble, Play Poker. win some lose more. Current occupation: avoiding WW3, Nukes and Russian Bots. #buybitcoin


Footage shows the moment Lil Tjay attacked and shot Offset in the butt inside a Florida casino over a $10K debt he refused to pay. Reports also say Offset now owes up to $900K from money borrowed for gambling.


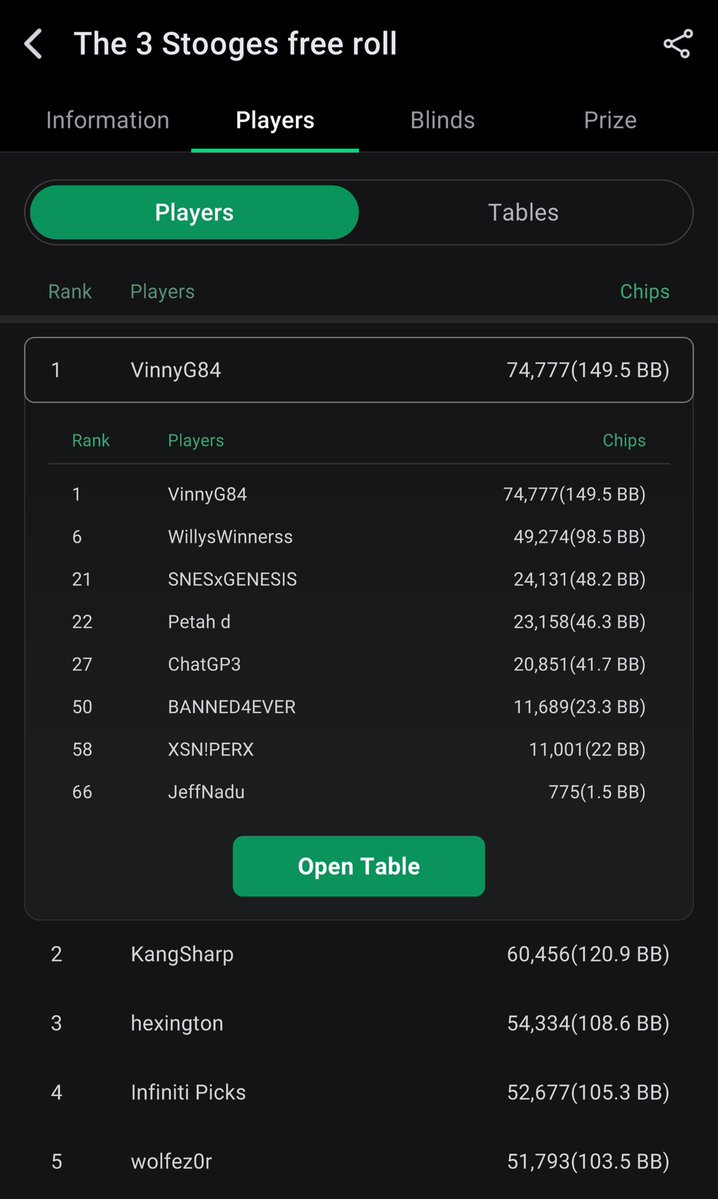
The snow melts. The days grow longer. The earth wakes up. And right on cue, John Tavares’ @NLLBandits flip the championship switch. As per @TheBusso, the Bandits are 24-4 in the months of April & May since the start of 2023. #MarchToMay


A Michigan Man burst into our private room at St. Elmo’s to perform for the group. Security escorted him out. Dave Portnoy thought he was a House Magician and asked security to bring him back. This is what ensured:


Last Wednesday (March 25), my crypto wallet was drained for ~79k. I have had people assist me during the investigation period and while I am not certain, I believe is the attack may have originated from a phishing link in the bio of a profile currently leading @Kalshi's weekly leaderboard for total predictions. I had clicked into a profile (“Miss.Cleo”) while browsing and saw what looked like a normal Vercel link. It was actually vvwv.vercel.app — two v’s made to look like a “w.” In hindsight, the account looks suspicious: created in January 2026, zero posts, no public profit or volume, but 160k+ predictions in roughly three months. It doesn’t seem like normal trading activity. It looks more like someone synthetically climbing the leaderboard to gain visibility, and drive traffic through the bio link. The link has since been removed. Including all the nerdy details of the crypto theft below on the off chance anyone cares to read : Within 27 minutes of clicking the link, an automated script drained my entire Exodus wallet — BTC, USDC, and USDT — across two blockchains. At 11:59 AM EST, $28,039 in USDC was sent to: 0x7dc0cbf8c92b819652d577cae53fb021cfadaf72 Within 36 seconds, dust deposits started arriving from lookalike addresses — address poisoning designed to confuse any future copy-paste transactions. At 12:16 PM EST, the BTC sweep started. 10 transactions fired in 10 seconds — one per second — each draining a UTXO to a different Bitcoin address. Five minutes later, a second burst: 7 more transactions in 7 seconds. 17 total BTC transactions. This cadence is not possible manually At 12:26 PM EST, the remaining $527 in USDT was drained to: 0x785c5f491fa058f6b2149b9ff2b186869bd1c969 Total stolen: ~0.7017 BTC (~$49,700), 28,039 USDC, 527 USDT. Approximately $79,853 in under 30 minutes. USDC ($28,039): Moved within 3.5 hours through an intermediary, then forwarded in 48 seconds to a high-volume aggregator: 0x2CfF890f0378a11913B6129B2E97417a2c302680 As of today that aggregator holds over $21.5 million — 838 ETH, 10.3M USDC, 2.5M USDT, 56 WBTC, and 213 other tokens. This was premeditated. The USDC theft address is not a normal wallet — it's an EIP-7702 proxy contract that was deployed and pre-funded with ETH from multiple addresses starting March 22 It processes transfers from hundreds of addresses every few minutes. This is not a personal wallet. It's either an exchange hot wallet, an OTC desk, or a professional laundering operation. BTC (~$49,700): Was scattered across 11 addresses, cycled through a self-mixing pattern, and consolidated. That consolidation address has since been swept — the BTC was batched into a 70+ BTC transaction alongside what appears to be funds from other victims. All 11 theft addresses are now zeroed out. The BTC is gone. USDT ($527): Still sitting untouched at 0x785c5f491fa058f6b2149b9ff2b186869bd1c969