Post Quantumize
24 posts


Post Quantumize
@postquantumize
Your wallet may already be exposed. Check your quantum risk. Free. Live on-chain data.




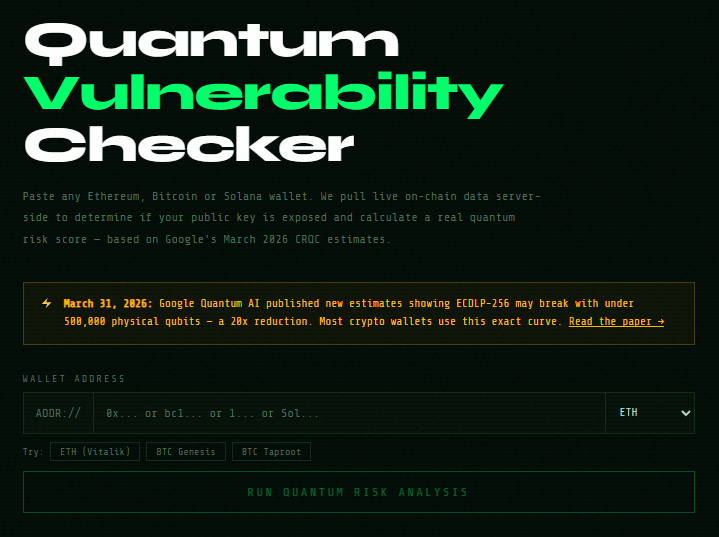
Many are wondering "what Google saw" that caused them to revise their post-quantum cryptography transition deadline to 2029 last week. It was this: research.google/blog/safeguard…

Many are wondering "what Google saw" that caused them to revise their post-quantum cryptography transition deadline to 2029 last week. It was this: research.google/blog/safeguard…


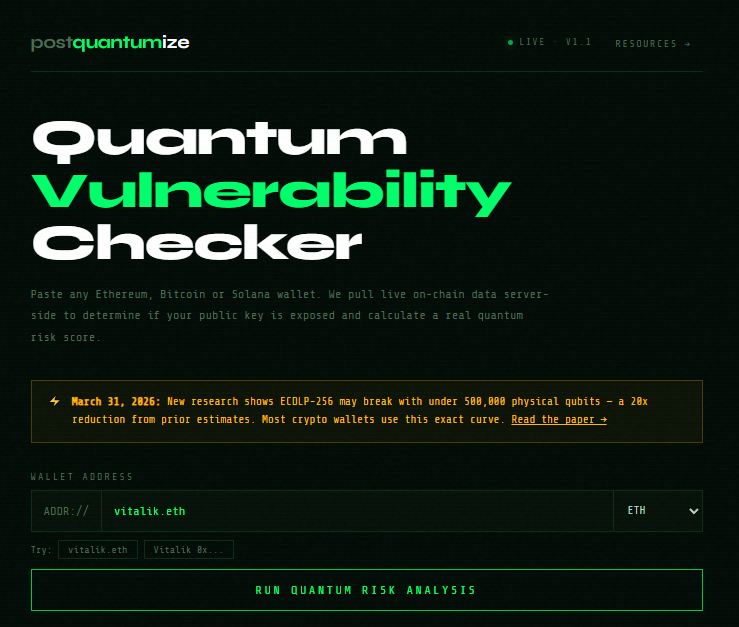


Gm ENS fam. We have now added .eth @ensdomains search on the Quantum Vulnerability Checker at postquantumize.com

Gm ENS fam. We have now added .eth @ensdomains search on the Quantum Vulnerability Checker at postquantumize.com






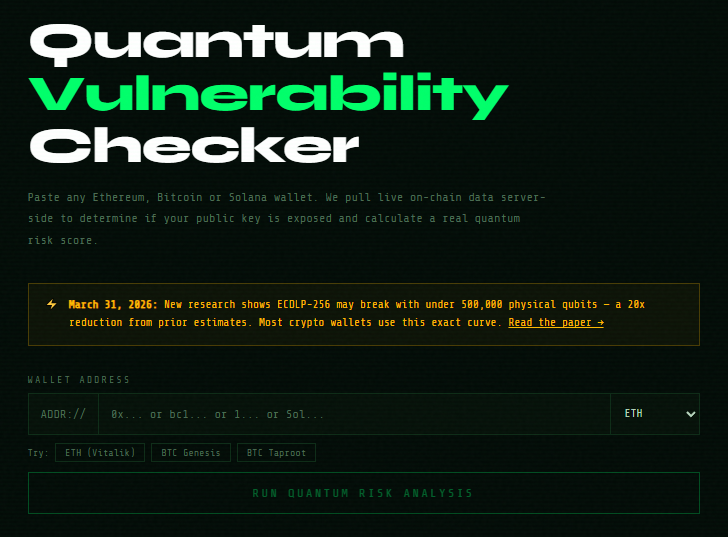
Introducing postquantumize.com Quantum computers are getting closer to breaking crypto wallet security. Paste your wallet and see if your public key is already exposed on-chain. No wallet connect required.

Ethereum is going post quantum. pq.ethereum.org