CYBCRIME أُعيد تغريده

New research reveals detailed analysis of DPRK VPN infrastructure used by North Korean operatives abroad.
According to technical analysis published by NK Internet Watch, "Hangro" appears to be a specialized VPN client that enables North Koreans overseas to establish secure connectivity back to domestic networks, potentially including the Kwangmyong intranet.
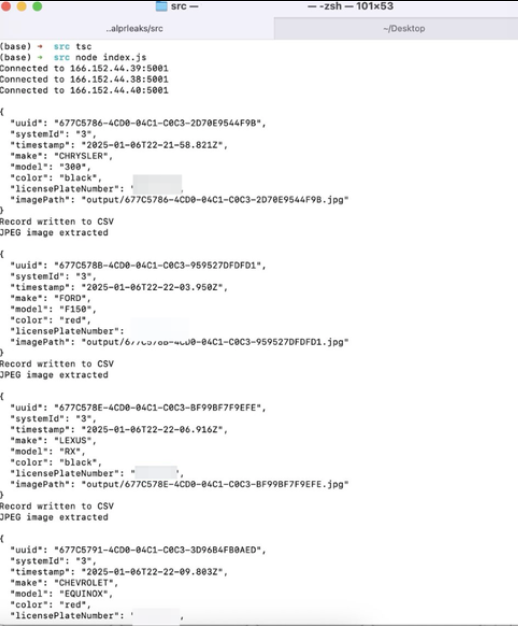
📍 Infrastructure spans multiple countries with servers in Russia (188.43.136.115/116) and North Korea (175.45.176.21/22)
📍 Requires mutual TLS authentication with certificates signed by internal CA "hrra2024"
📍 Uses embedded GOST cipher references suggesting Russian cryptographic influence
The research traces connections through Jo Myong Chol, a sanctioned DPRK national who registered supporting domains using the email support@silibank.com. This same email was used for other regime-affiliated sites including ournation-school.com and uriminzogkiri.com.
1️⃣ Radio Free Asia reported North Korean trading companies pay $350 to the Shenyang consulate for Hangro access
2️⃣ Technical analysis reveals the client is derived from SoftEther VPN with custom authentication mechanisms
3️⃣ The service recently appeared on DPRK-affiliated websites as "service for visitors away from home" before disappearing in July 2025
This infrastructure represents a sophisticated method for maintaining regime connectivity with overseas operatives and commercial entities.
Source: nkinternet.wordpress.com/2025/01/06/han…

English