DevAhmadz🖥️
6.3K posts

DevAhmadz🖥️
@DevAhmadz
IT Support Specialist ⚙️ | DevOps Trainee 🧪 | Python Automation 🐍 Built an Offline AI Support Bot 🤖 | Bash, Streamlit, GitHub Novelist in progress ✍️ | Docs


TROOPS INTERCEPT N37 MILLION TERRORIST FUNDS In a significant blow to terrorist financing networks, troops of Operation HADIN KAI have intercepted N37 million at a checkpoint along the Maiduguri–Gubio Road in Borno State. The cash was concealed in bags inside a suspicious vehicle. Five suspects were arrested. Mobile phones linked to terrorist coordination activities were also recovered. This is not the first such interception. In February, troops intercepted N37 million at another checkpoint. The pattern is clear: despite military pressure, terrorist logistics networks remain operational and well funded. "The interception represents a significant breakthrough in dismantling financial conduits suspected to support terrorist logistics and coordination activities," military sources said. The suspects are in custody, and investigations are ongoing to uncover the full network behind the financing. The question is no longer whether terrorist groups have access to funds. They do. The question is: who is funding them and how do we stop the pipeline?






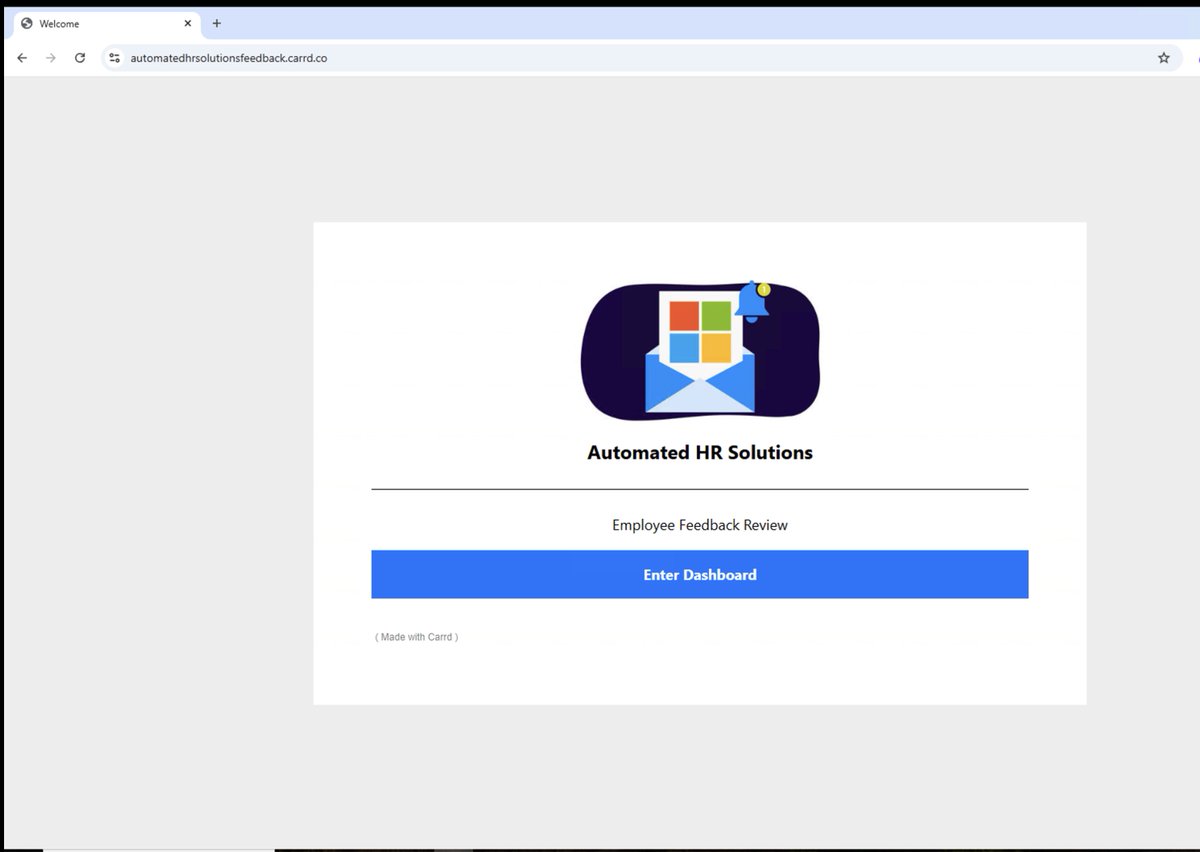
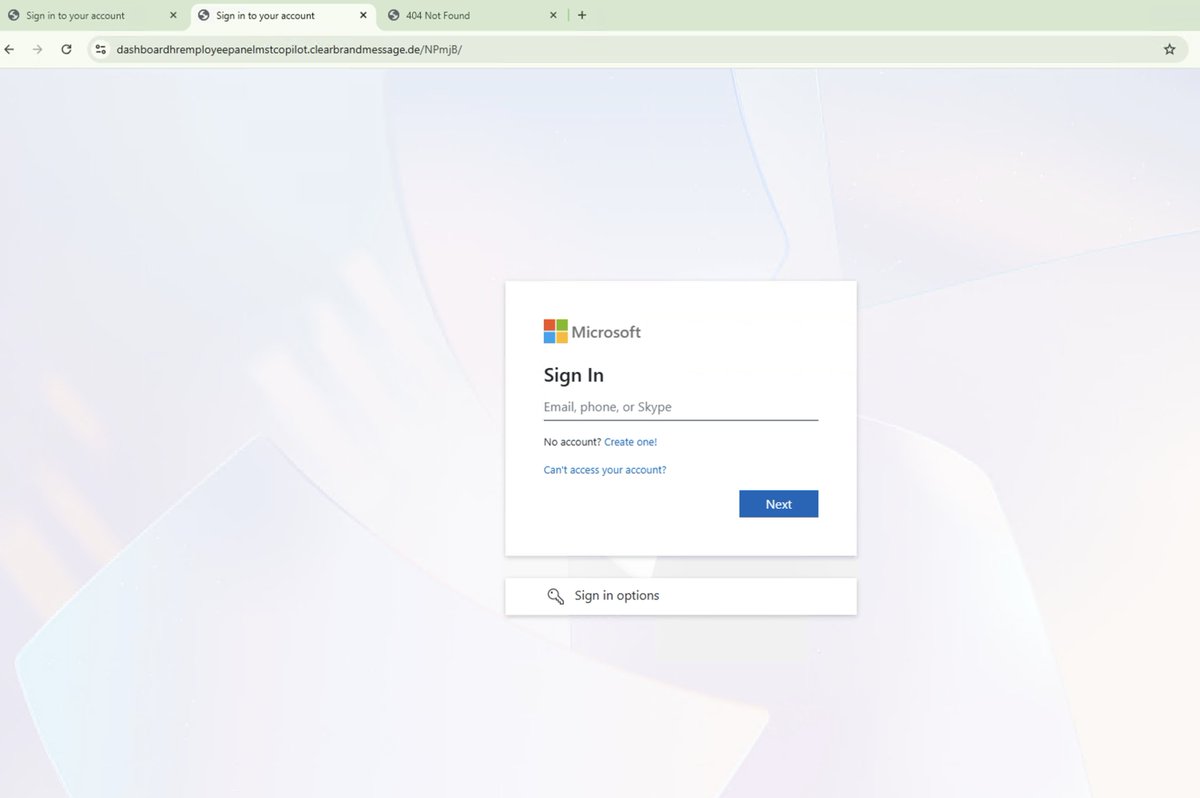
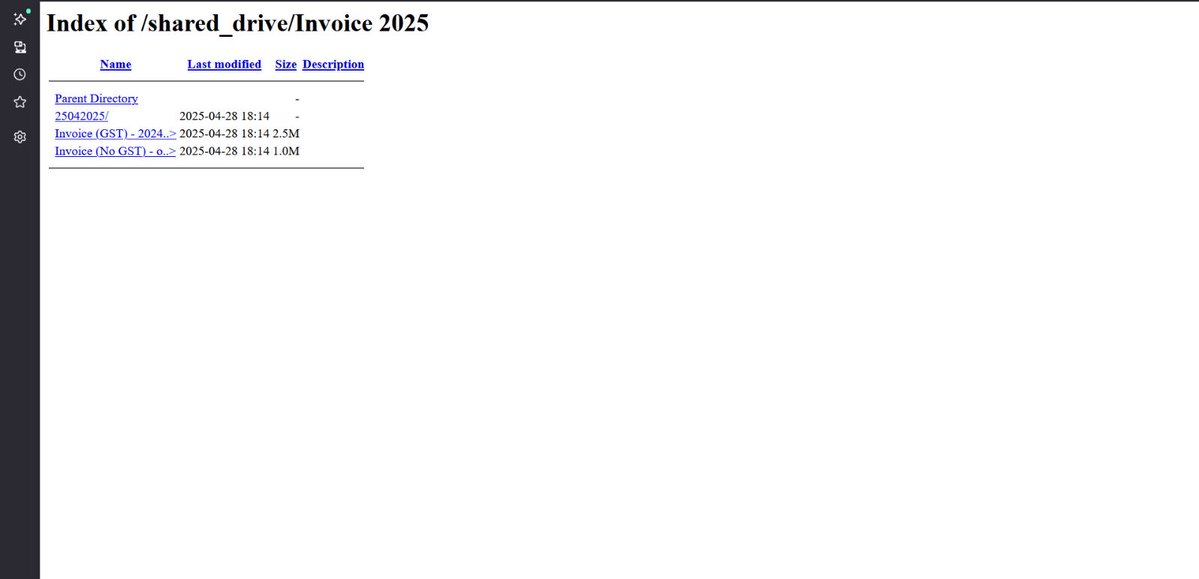
🚨Cyber Alert ‼️ 🇳🇬Nigeria - 𝗡𝗡𝗣𝗖 𝗛𝗲𝗮𝗹𝘁𝗵 𝗠𝗮𝗶𝗻𝘁𝗲𝗻𝗮𝗻𝗰𝗲 𝗢𝗿𝗴𝗮𝗻𝗶𝘀𝗮𝘁𝗶𝗼𝗻 XP95 hacking group claims to have breached NNPC Health Maintenance Organisation. Threat actor: XP95 Sector: Financial / Insurance Data exposure (claimed): 200,000 user records Data type: Personal data Observed: Apr 08, 2026 Status: Pending verification ESIX©: 5.73 Full details and impact assessment on HackRisk.io





John Jones was stuck like this for 27 hours in Nutty Putty Cave, Utah, before he died. In the final hours, rescuers considered pulling him out, knowing it could break his spine and legs. The risks were too high, and the team ultimately decided it would be more humane to let him die. The rescue team stayed in contact with him until the very end; trapped upside down, he eventually went into cardiac arrest and died.



Day 1 of learning HTML


🚨Cyber Alert ‼️ 🇳🇬Nigeria - 𝗡𝗡𝗣𝗖 𝗛𝗲𝗮𝗹𝘁𝗵 𝗠𝗮𝗶𝗻𝘁𝗲𝗻𝗮𝗻𝗰𝗲 𝗢𝗿𝗴𝗮𝗻𝗶𝘀𝗮𝘁𝗶𝗼𝗻 XP95 hacking group claims to have breached NNPC Health Maintenance Organisation. Threat actor: XP95 Sector: Financial / Insurance Data exposure (claimed): 200,000 user records Data type: Personal data Observed: Apr 08, 2026 Status: Pending verification ESIX©: 5.73 Full details and impact assessment on HackRisk.io

🚨Cyber Alert ‼️ 🇳🇬Nigeria - 𝗡𝗡𝗣𝗖 𝗛𝗲𝗮𝗹𝘁𝗵 𝗠𝗮𝗶𝗻𝘁𝗲𝗻𝗮𝗻𝗰𝗲 𝗢𝗿𝗴𝗮𝗻𝗶𝘀𝗮𝘁𝗶𝗼𝗻 XP95 hacking group claims to have breached NNPC Health Maintenance Organisation. Threat actor: XP95 Sector: Financial / Insurance Data exposure (claimed): 200,000 user records Data type: Personal data Observed: Apr 08, 2026 Status: Pending verification ESIX©: 5.73 Full details and impact assessment on HackRisk.io