Angehefteter Tweet
b33f | 🇺🇦✊
10.3K posts

b33f | 🇺🇦✊
@FuzzySec
意志 / ▓▓▓▓▓▓▓▓▓▓▓ / Team 501 / ex IBM Capability Lead & FireEye TORE / I rewrite pointers and read memory / AI Psychoanalyst / Teaching @CalypsoLabs
Jumanji Beigetreten Nisan 2012
1.2K Folgt33K Follower

Highly underrated part of capability development in RT as well, when you stop calling your tools things like super8, fourfoil, silicone, or straylight and name them ticket-extracting-gimbal or stack-changing-thing it's all over. And, anyone who pushes such an agenda is promoting the quiet death.
When you know the fourfoil in all its seasons, root and leaf and flower, by sight and scent and seed, then you may learn its true name, knowing its being: which is more than its use.
-Ogion, A Wizard of Earthsea
Cvewhen?@cvewhen
iOS exploit names are so badass - FORCEDENTRY, BLASTPASS, TERRORBIRD etc. When I'm out of my agentmaxxing era, I will sit with iOS for the love of the g(n)ame
English

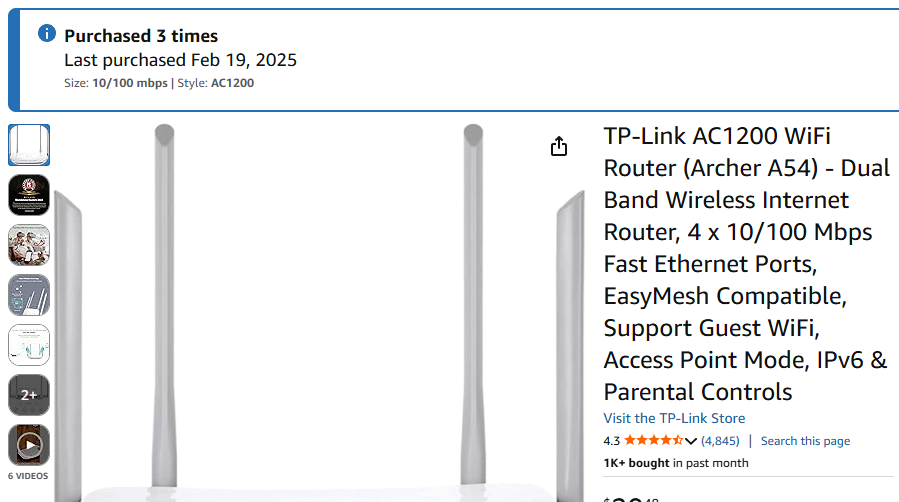
😅 I haven't reported any of this but yea there is an unauthenticated service that may or may not process cool SOAP requests. I should mention that I also found a stack overflow somewhere else but I am not set up to debug on MIPS so this was easier. This is probably good hardware to add to a ctf.
English
b33f | 🇺🇦✊ retweetet

In collaboration with Lookout and Google (thank you 🙏) we have been working on tearing down and building detections for DarkSword - iOS exploit chain for iOS 18.4 - 18.7. Super excited for this research 🎉. Please update your iPhones.
iverify.io/blog/darksword…
English
b33f | 🇺🇦✊ retweetet


United States President Donald J. Trump posted this message on social media today.
Personal grievances the Trump administration it asserts it has with other countries and political theatrics aside, the notion that the United States even hints are exiting NATO is a PROFOUND cybersecurity issue.
Yes, NATO deals with traditional military stuff (land, sea, air, space), NATO also deals with things in the digital domain (cyberspace).
NATO (non-United States) has historically shared a great deal of intelligence with each other regarding state-sponsored threats to the United States. Likewise, the United States has shared intelligence on state-sponsored with our NATO allies.
It makes me incredibly nervous that this idea of exiting NATO is floated or threatened. NATO cybersecurity space deals a lot with ICS/SCADA (Industrial Control Systems, which is things like water treatments plants, nuclear energy facilities, telecommunication systems, etc) and anything else which possesses a military threat to the United States and it's citizens.
I am unsure of the impact leaving NATO would have on our cybersecurity intelligence. The idea makes me very nervous. The United States is constantly under siege from foreign adversaries (notably China, Russia, North Korea, Iran).
Additionally, I have great concern that if we left NATO it would damage our relationship with European allies which have been of significant importance apprehending Threat Actors who have done extreme damage to the United States. Part of the FBI's success in apprehending ransomware actors have been our strong relationship with EUROPOL, and European allies apprehending individuals residing outside the United States.
Chat, this unironically makes me very nervous.

English
b33f | 🇺🇦✊ retweetet
b33f | 🇺🇦✊ retweetet

We are thrilled to be sponsoring @offensive_con for the first time and to keep supporting the European security community. Thanks @Binary_Gecko for having us. See you there soon! 🇩🇪🇪🇺⚡️
offensivecon@offensive_con
We appreciate @prdgmshift for supporting this year's Offensivecon as a Silver Sponsor!
English

Yes agreed and it's interesting to examine the psychological reasons they do this, it's worth asking them when you discover it. I found that usually what happens is, they have a objective that is hard and they adjust the objective as an intermediary step to make progress with the intention of reverting back (or that's what they claim), but they don't adjust back. It's sometimes not clear if they pretend to give a good explanation or they initially did think it was a good reason. Claude much more likely to do reward hacking than codex in my experience. This has the potential to create a lot of issues in certain areas.
English

@HackingLZ Haha, Yeah you have to be careful with reward hacking and "manufacturing conditions" once you push models into a corner they're not as good at, especially using default "agents".
English

Maybe just a few notes here:
- I am artificially widening the race window on x86_64 for reasons explained in the readme
- This area of exploitation is pretty outside my domain of knowledge so it could probably be improved
- Dealing with Webkit builds sucks and I'm sorry people have to do that regularly haha
SOTA AI systems are powerful research tools. Through a simple analysis pipeline it's possible to reconstruct close-to-original code for fast analysis. AI models can also act as great teachers, like in this case, cramming tons of new knowledge into my brain in a relatively short time.
English

I am releasing a reconstructed version of the cassowary CVE (CVE-2024-23222) that was disclosed as part of the Coruna leak. I also did some research with my AI assistants 😄 to reproduce a crash for the bug on x86_64 Linux
github.com/FuzzySecurity/…
English

@roddux Yea I know, it's just that with a good ai pipeline you can really reconstruct back very close to the original source
English

Are the PAC gadgets in the coruna kit sensitive information still? I don't see any CVE's but they are bounded by version. I had an analysis pipeline reconstruct a lot of the kit fully (bluebird, breezy, cassowary, seedbell, terrorbird and the stagers) and I'm just thinking about what should or shouldn't be published.
English

Also I think it's worth saying, big love to my friends at the vendor. And all vendors btw. People fail to realize (constantly) that the work these teams do prevent harms you will never learn about. The stuff I have been reviewing is incredible engineering, I honour you ⚔️. F that guy and his fake rolex watches abusing your work.
GIF
English

@jamieantisocial Btw I only looked at the browser components not any of the payloads or PE
English

@jamieantisocial Yea I've seen that, and I think my pipeline pulled in his zip among others but it has gone a bit .. further on reconstruction of all the primitives
English