IVRE
150 posts

IVRE
@IvreRocks
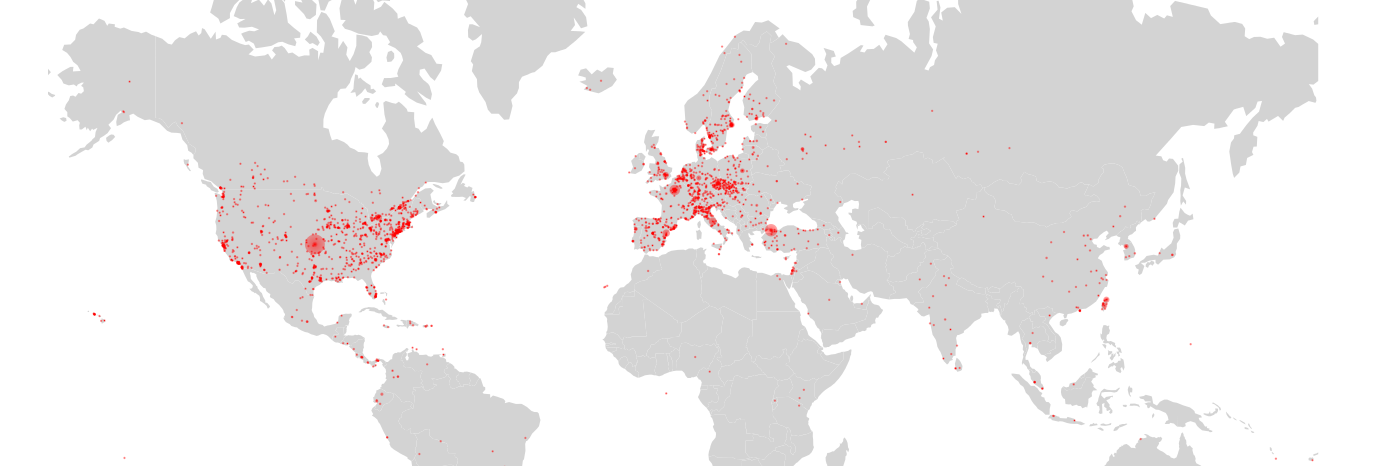
Open-source #network recon framework. Relies on @nmap, Masscan, @zeekurity, @pdiscoveryio, p0f, …. #OSINT #redteam #blueteam #bugbounty @[email protected]
Beigetreten Ocak 2016
400 Folgt1.3K Follower
IVRE retweetet

🚨 IVRE now supports Citrix NetScaler Triage!
CVE-2025-7775 (RCE, CVSS 9.2) is being exploited in the wild. It's time to monitor those instances.
OSS to the rescue! 🛡️
github.com/ivre/ivre/pull…
#CyberSecurity #CVE20257775 #NetScaler #Infosec


English

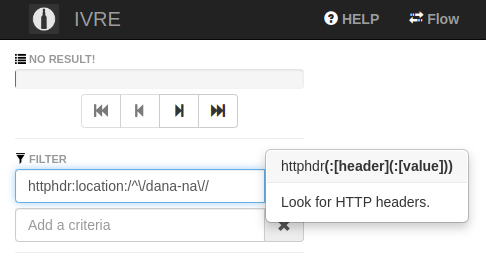
If you're looking for a way to find Ivanti gateways (for CVE-2025-0282... or to be ready for the next ones), and have collected the HTTP headers on a GET / (via @nmap http-headers script, or any other supported tool) you can use this filter : httphdr:location:/^\/dana-na\//
Nicolas Krassas@Dinosn
CVE-2025-0282 (CVSS 9.0): Ivanti Confirms Active Exploitation of Critical Flaw securityonline.info/cve-2025-0282-…
English
IVRE retweetet

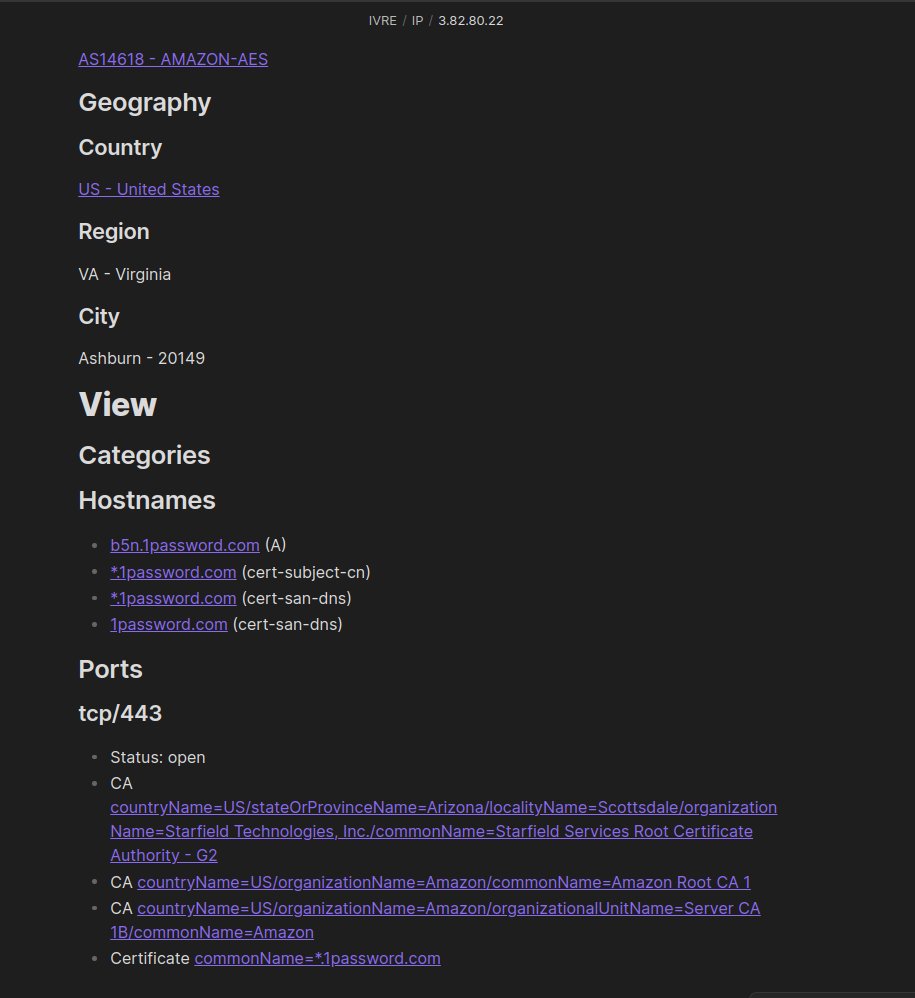
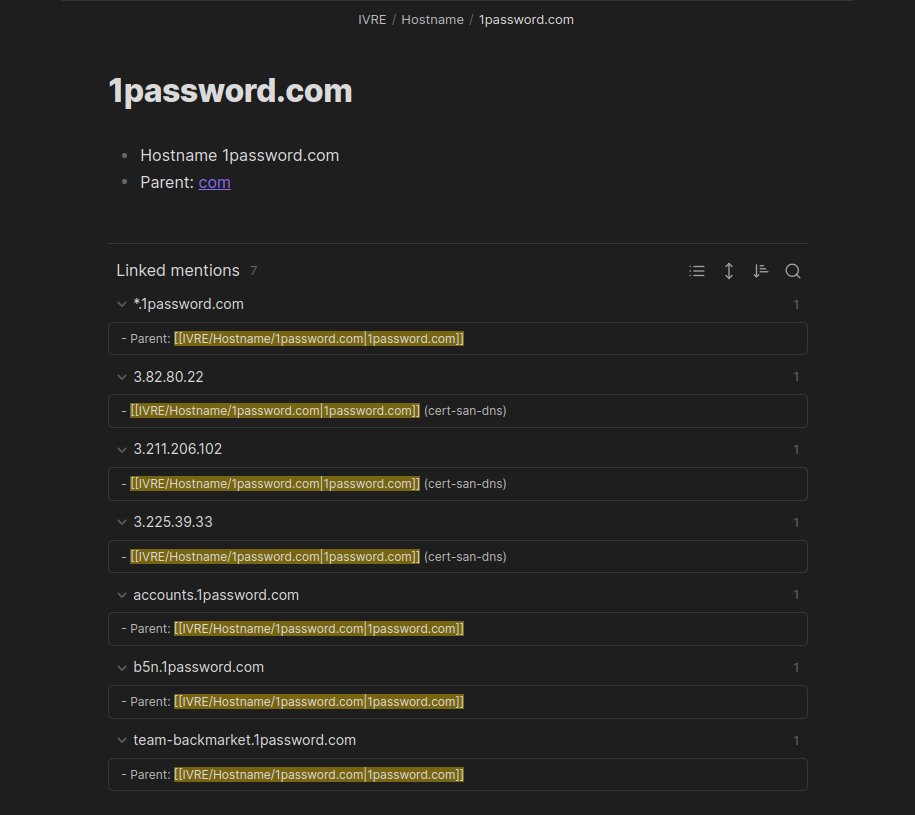
Network recon framework. Build your own, self-hosted and fully-controlled alternatives to Shodan / ZoomEye / Censys and GreyNoise, run your Passive DNS service, build your taylor-made EASM tool github.com/ivre/ivre
English
IVRE retweetet

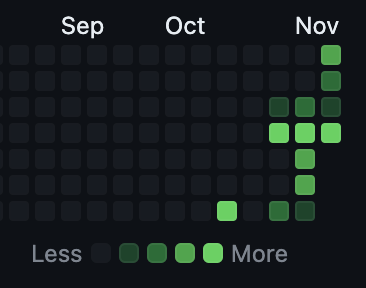
Current status:
I've made a ton of changes to masscan's --banners option, and integrated a bunch of changes from others, primarily @ivrerocks. I'd be interested in any bug reports if you want to test them out.
English

@snovvcrash Hey! Thanks for the kind words! However please note that some of the patches included in the fork won't be useful unless you import the results in IVRE, as it is the intent of this repository.
English

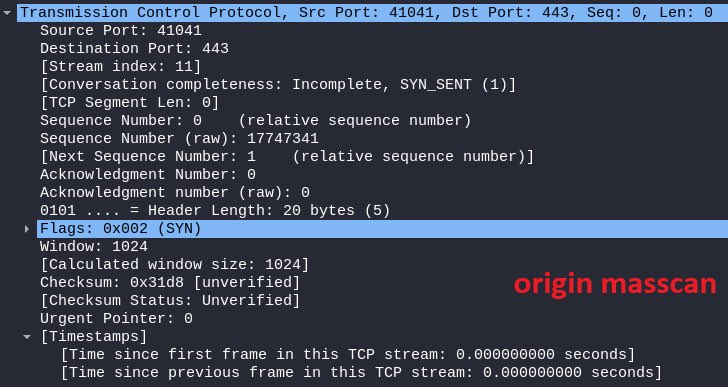
(1/2) FYI, #masscan users. The original masscan does NOT include the ‘TCP options’ field with MSS value which is required for some hosts to reply to the packet. The fork by @IvreRocks features the --tcpmss switch that includes the mentioned field for your better scope coverage ⤵️

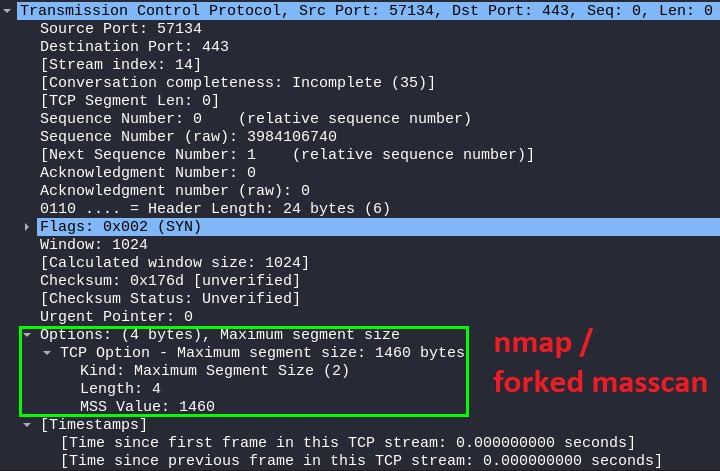
English
IVRE retweetet
🥳 We're pleased to announce the first group of winners for the 2023 Google Open Source Peer Bonus Program!
This cycle received a record-breaking 255 nominations. Huge congratulations to the 203 winners.
See the winners → goo.gle/45vnbZ6

English
IVRE retweetet

HackerNews: "Researchers uncover new BGP flaw in popular routing software"
One way to help prevent these kind of denial-of-service exploits is to make sure your perimeter is secure to trusted sources. I built a tool to perform such perimeter scanning here
kaonbytes.com/p/perimeter-sc…
English
IVRE retweetet
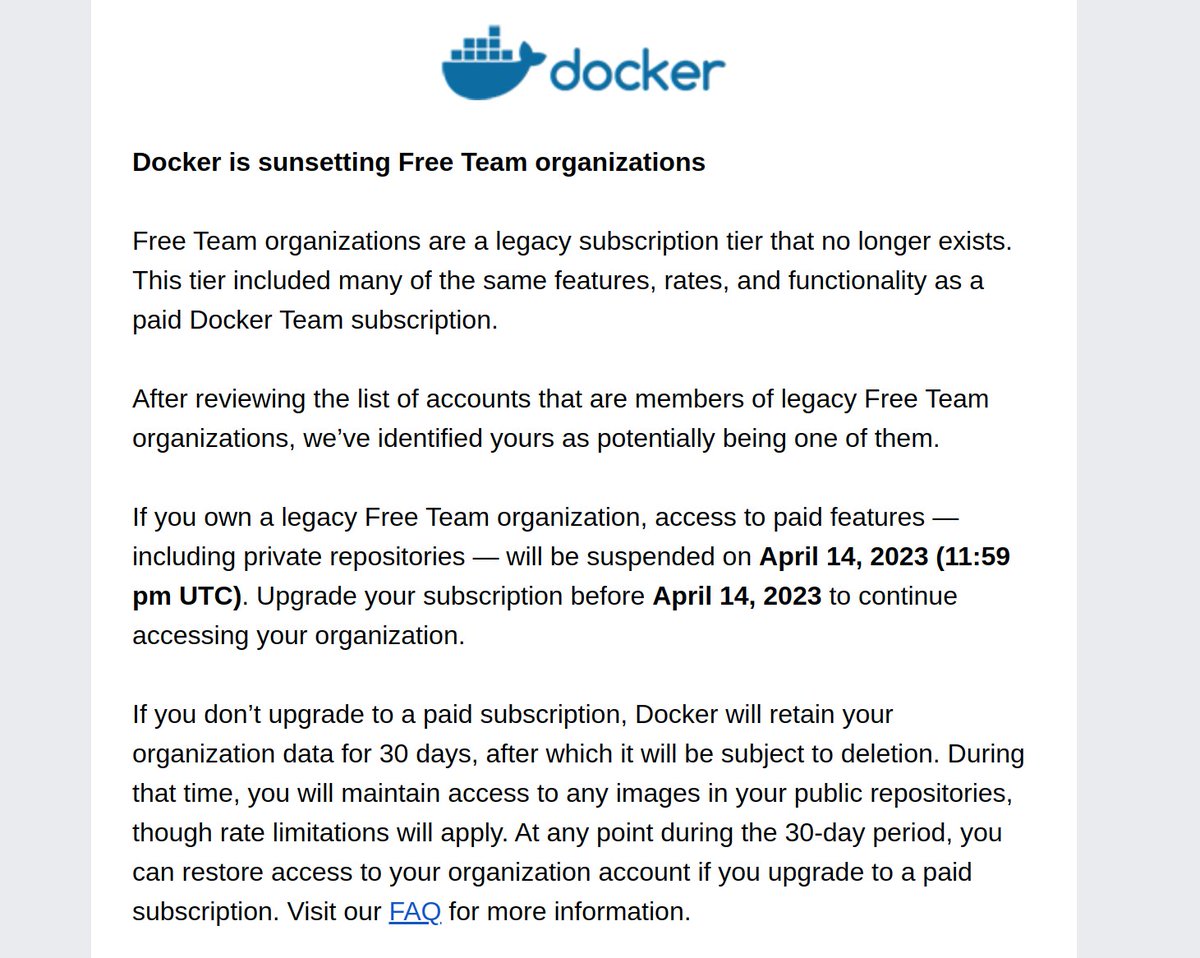
Is Docker saying that the OSS openfaas organisation on Docker Hub will get deleted if we don't sign up for a paid plan?
What about Prometheus, and all the other numerous OSS orgs on the Docker Hub?
cc @justincormack
English

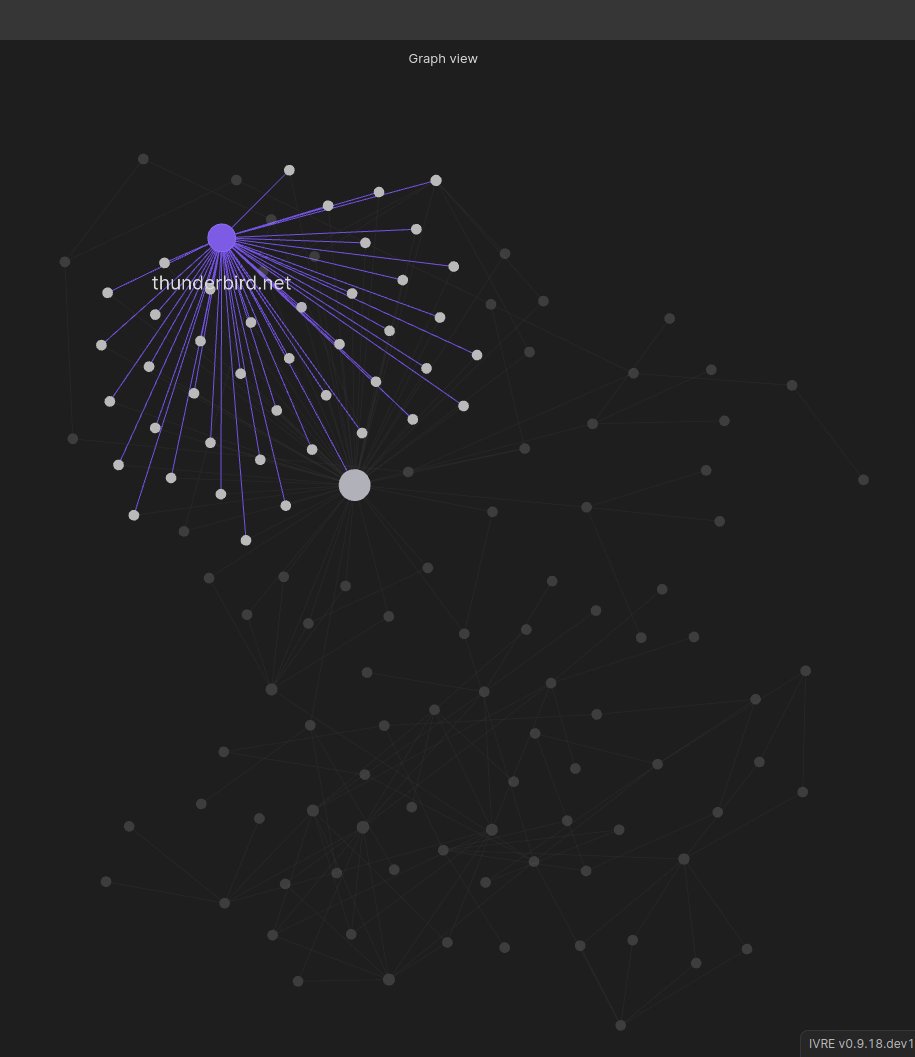
If you use @obsdmd for your #pentest / #redteam or #threatintel notes, you might be interested in the IVRE community plugin for #Obsidian, that uses data from IVRE to enrich your notes.
Get it from Obsidian (in community plugins, look for "ivre") or see github.com/ivre/obsidian-…
English

Thanks to Tesseract OCR, IVRE has been doing this for almost 8 years now! And thanks to MongoDB, you can use the extracted text in your queries efficiently. That's how powerful and magic opensource can be! #OSS
Shodan@shodanhq
Shodan extracts the text from screenshots so you can search across the content of the images: images.shodan.io
English

@nullt3r @nullenc0de I ingest output from other tools, including httpx, tldx & nuclei.
English

@nullenc0de @nullt3r For non-TLS HTTP requests, Masscan will do that within the SYN scan when using --banners
English

@nullenc0de I used Masscan to scan for open ports and httpx (projectdiscovery) to do the dirty work (get TLS info, headers, body etc.). After that I used clickhouse for result analysis (I could directly import the JSONL from httpx) - about 10 GB of data. 10 servers.
English
IVRE retweetet

Due to recent events, some Kali Linux tool creators now have Mastodon accounts
@epi@infosec.exchange (@epi052)
@ivre@infosec.exchange (@IvreRocks)
@seemoo@infosec.exchange (@seemoolab)
@r00t0v3rr1d3@infosec.exchange (@r00t0v3rr1d3)
@droe@infosec.exchange (@droethlisberger)
⬇️🧵
Cyber Detective💙💛@cyb_detective
Today I started collecting a list of accounts from developers and small teams who have created tools added to the official version of #Kali Linux: twitter.com/i/lists/152769… Subscribe to it to stay on the cutting edge of #cybersecurity. 🧵🧵🧵
English