Angehefteter Tweet

Introducing our new eBook: "ASM in the Age of CTEM". Follow this link to download your free copy now: slcyber.io/ebooks/asm-in-…
English
Searchlight Cyber
1.3K posts


@SLCyberSec
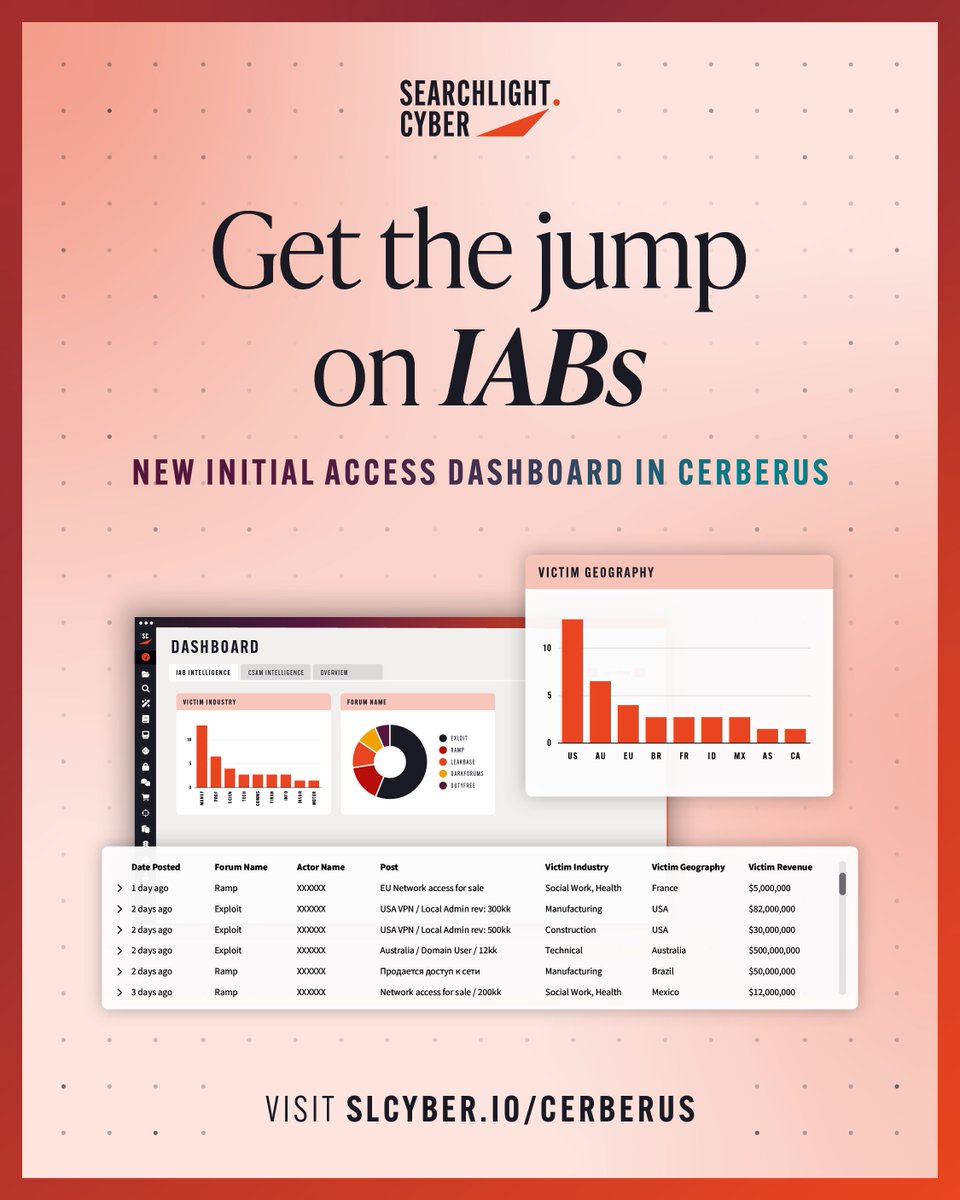
Searchlight Cyber creates products to enhance investigations, protect businesses, and combat cybercrime. Request a trial at https://t.co/zDISBtLIcU