Security Trybe
39.7K posts


Security Trybe
@SecurityTrybe
Simplifying Cybersecurity & Tech | https://t.co/NIuxWOtJYz





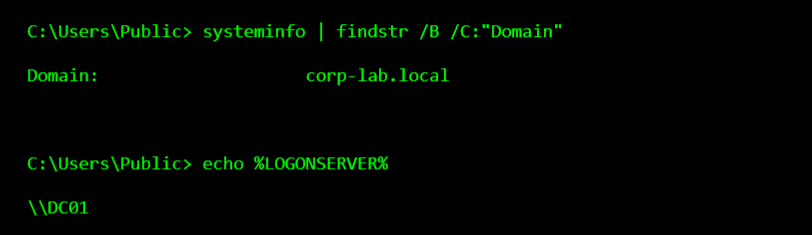
After gaining access to a Linux server, attackers usually do not begin by running loud scans or dropping tools everywhere. The first move is often much smaller and much more useful: they check the files that explain how the system works. Configuration files, shell histories, SSH trust files, web app settings, and environment files can reveal passwords, internal hosts, database connections, and privilege paths without making noise. This is why the earliest stage of a compromise often looks boring. A careful attacker is not trying to impress anyone. They are trying to learn which file gives the fastest path to more access. One exposed .env file or one weak SSH configuration is often worth more than a dozen exploits. That is also why good investigations focus on file access patterns. The first valuable clue is often not “what malware ran,” but “what file was opened first.” Attackers reveal intent by what they read before they reveal capability by what they execute.




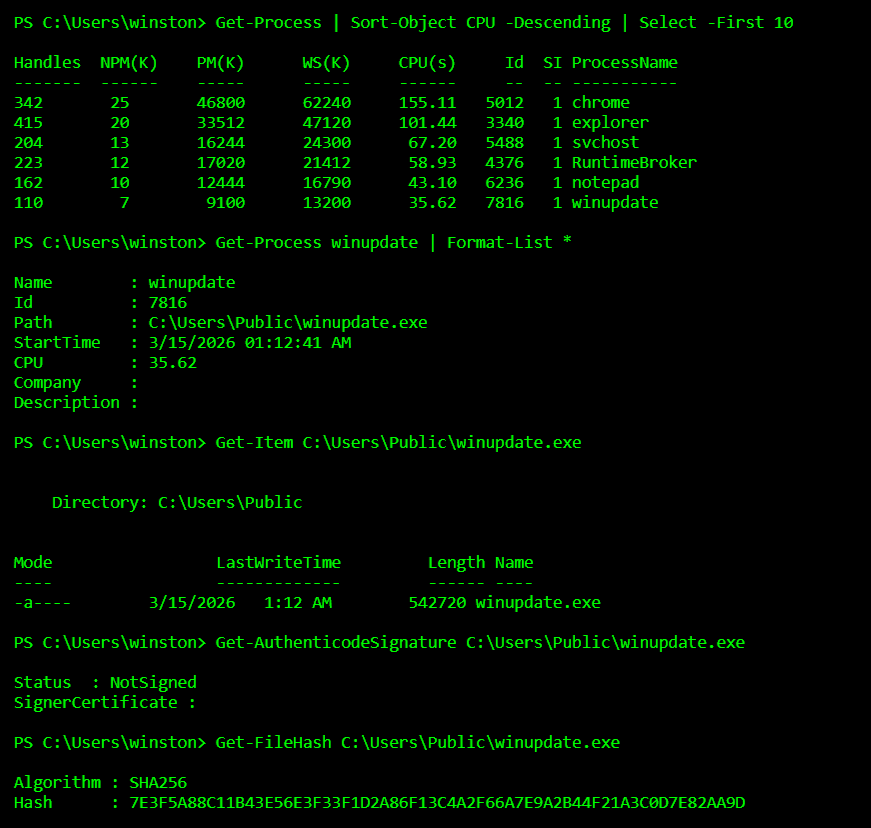
Most malware is not discovered because antivirus is smart. It is discovered because analysts know how malware behaves inside a system. Attackers rarely drop obvious files anymore. Instead they hide persistence in scheduled tasks, registry keys, or strange processes that quietly run in the background. If you want to understand malware, stop looking for viruses and start looking for behavior.






Getting access to a Linux server is not the goal, Keeping access is. Most attackers don’t rely on passwords after the first compromise. They switch to something quieter, something that won’t trigger alerts. One of the most abused persistence methods is hiding inside SSH itself. If you know where to look, you’ll find it.