Martin
1.9K posts


Martin
@ShieldifyMartin
Co-Founder @ShieldifySec Taking your smart contracts' security seriously!
Beigetreten Nisan 2022
982 Folgt2.8K Follower
Martin retweetet
Martin retweetet

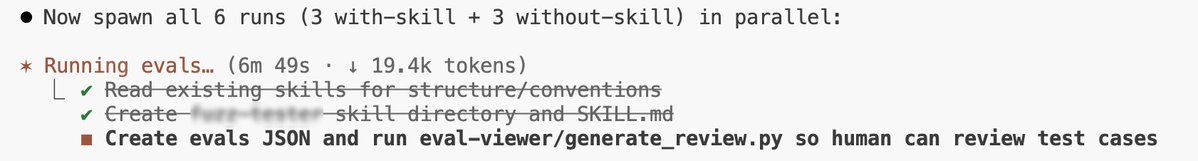
🚨 OpenClaw Security Flaws
When you ship fast to catch the trend, you usually compromise on security 🤔
immersivelabs.com/resources/c7-b…
English

🚨KeomProtocol was exploited for $94k on Polygon ZKEVM
A logic bug in KToken.redeemFresh() caps redeemTokens to the user’s cToken balance after calculating totalSupplyNew with the uncapped value, and never recalculates redeemAmount.
This results in minting a tiny amount of cTokens and draining the market’s entire cash balance via redeemUnderlying().
This is a straightforward issue that an audit would catch. Stay safe. 🫡
English

Ethereum Upgrades in 2026 🔍
1. Glamsterdam
- splits proposing vs building. Validators outsource block construction safely. More throughput, better scaling.
- predeclare state access for the whole block. Enables parallel execution, faster sync, lower and more predictable gas for heavy apps.
2. Hegotá
- introduction of Verkle Trees, a new data structure designed to replace the current Merkle Patricia trees.
- reduced storage requirements, allowing nodes to run on cheaper, lower-spec hardware.
English
Martin retweetet
Fuzzing for Security Researchers 🤠
Starting with basic and fuzz testing in Foundry, then moving to stateful fuzzing with Echidna, Alex shows how stateless and stateful fuzzing can uncover bugs that traditional imperative tests often miss
youtu.be/3A7aa5B8aak
YouTube
English

Solid teams are pushing way ahead of the present. Hope the crypto space will increase its pace soon 🙏
Tally@tallyxyz
English

Phishing and wallet compromises are still the leading cause of crypto losses. Not complex code exploits. Stolen keys, malicious signatures, weak wallet hygiene.
Using hardware wallets, separating operational and treasury wallets, and carefully verifying every transaction remain the simplest and most effective defences. 🫡
English

@ShieldifyMartin @VenusProtocol Good luck with the fix. Imagine if 'working on a solution' meant formal proofs before mainnet. Wild concept, right?
English

🚨 Earlier today, Venus Protocol's Core Pool on BNB was targeted by a supply cap manipulation attack.
@VenusProtocol is investigating suspicious activity involving the $THE pool, with $THE and $CAKE markets affected.
On-chain data suggests a flash-loan exploit where an attacker accumulated 84% of the (14.5m $THE) cap over 9 months and used it as collateral to borrow CAKE, BTCB, and BNB, extracting $3.7M.

English

@ShieldifyMartin @VenusProtocol TVL: $1.7B. Security guarantees: *checks notes* ...hope? Without formal verification, you're betting attackers are less creative than your auditors.
English
Martin retweetet