VirtualSamurai
49 posts







2000 days. Zero excuses. Meet Kevin, also know as @mika_sec by our community! He didn’t just build a streak, he transformed his entire career. From early-morning coffee sessions to landing a role as a Cyber Security Engineer. Kevin’s TryHackMe journey is the blueprint for what happens when you commit to becoming better every day. If you need a sign to start (or restart) your cyber journey, this is it. 👉 Read Kevin’s full story on the blog: tryhackme.com/resources/blog…


🥶🥶 More than 70 teams registered so far for P3rf3ctr00t CTF 2025🔥💯 Register today for a chance to show your Cybersec might💪🏾💪🏾 ctf.perfectroot.wiki

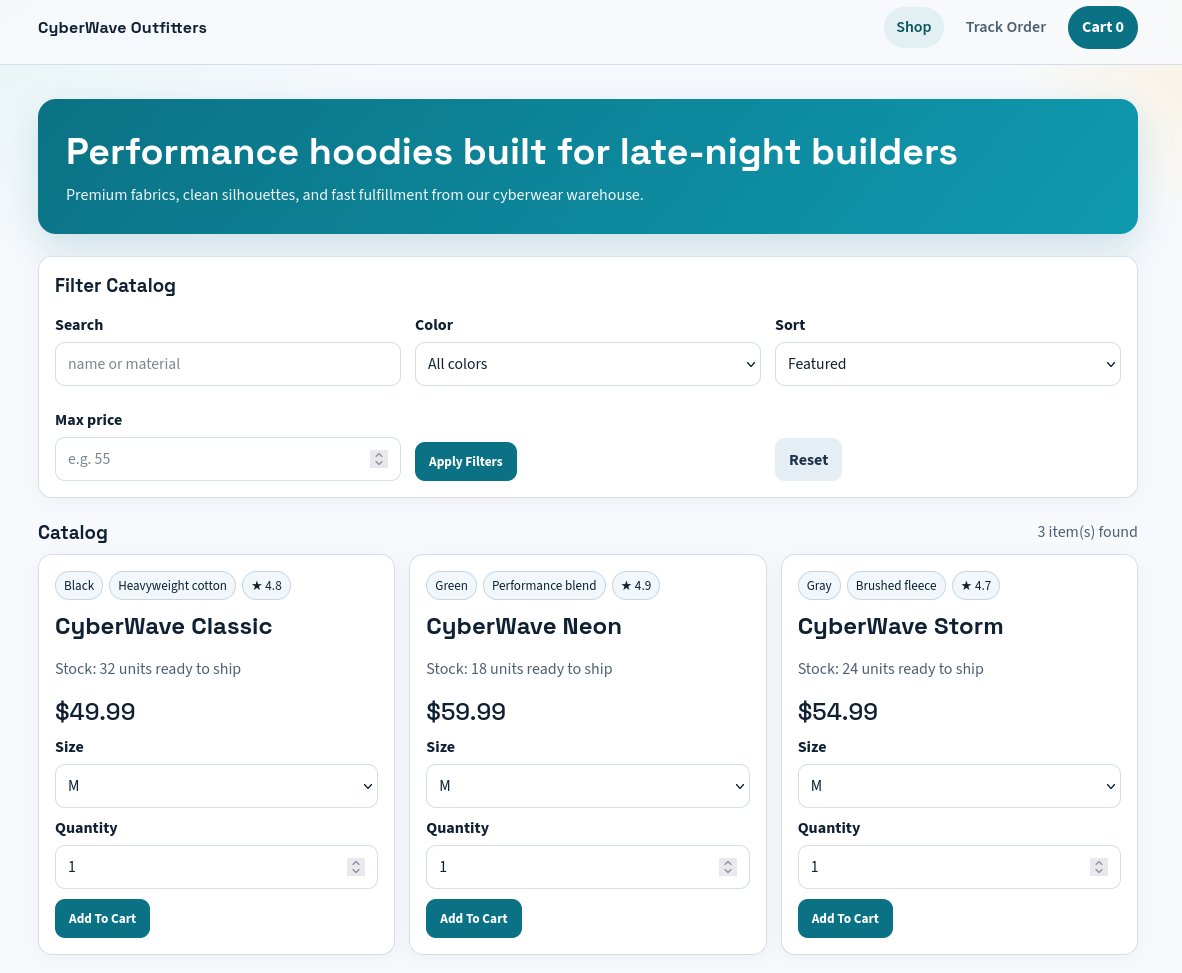
You're starting a #redteam engagement tomorrow...Where would you train without spending tons of money ? We are releasing a new redteam lab with : - On-prem #ActiveDirectory - 5 vulnerable machines - Antivirus & Firewall Available on November 8th here : training.cyberwave.network