Mehran Armiyon
220 posts












Today we are introducing a Python SDK for Mac's on-device LLM! github.com/apple/python-a… apple.github.io/python-apple-f…


@GoodieHimSelf جرات نمیکنم پیامها رو باز کنم. نه بخاطر خشونت تصاویر. اون انقدر سخت نیست که پرسشهای مادرانی که بچههاشون بازداشت شدند. عکس گمشدهشون رو میفرستند با چهرههایی که در ویدیوها محو کردم مقایسه کنم! التماس میکنند فرستنده ویدیوی پیکر عزیزشون رو معرفی کنم تا از آخرین لحظاتش بپرسند.

آخرین پیام من با #سعید_سوزنگر، تنها خواستش این بود که "صدامون باش داداش" #سعید_سوزنگر بازداشت شده.

#سعید_سوزنگر سهشنبه هفتهی گذشته ظاهرا بازداشت شده و خبری ازش نیست


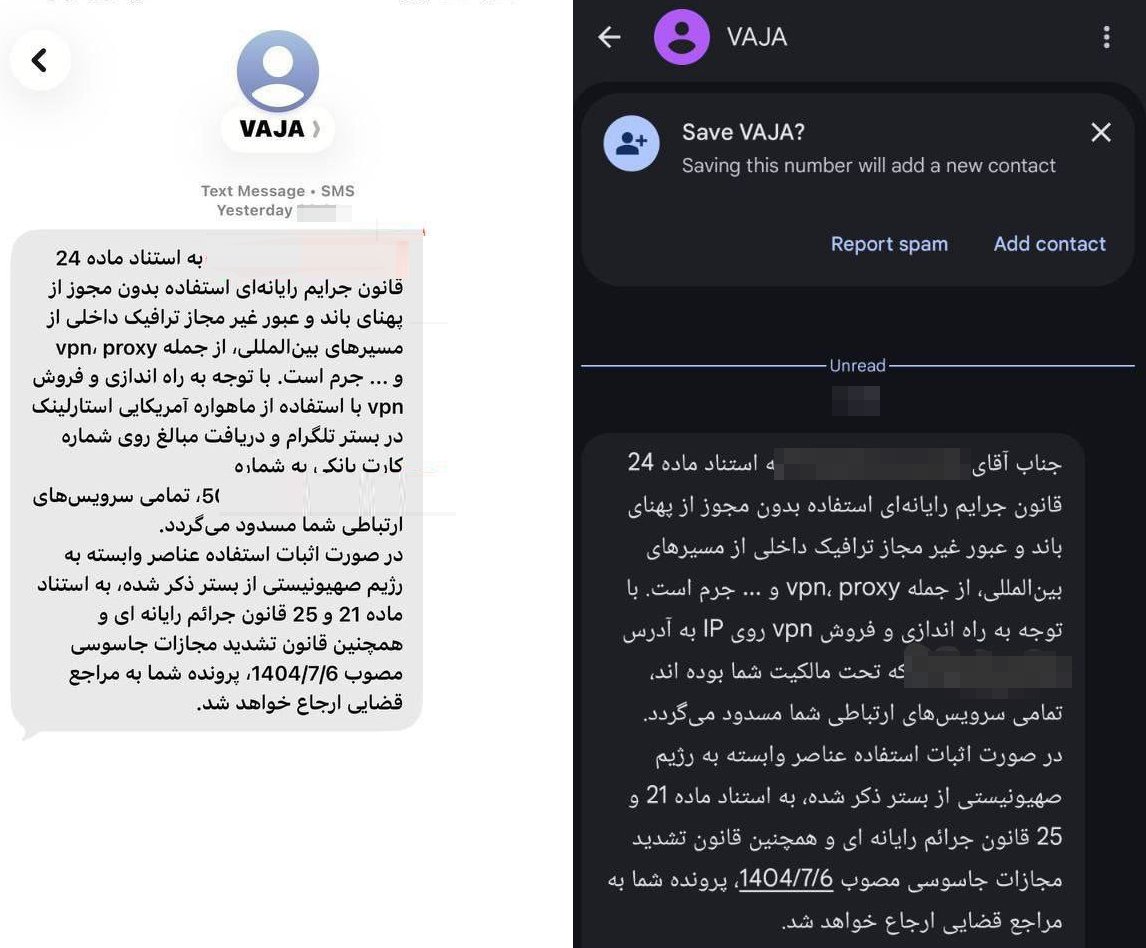
We are doing our utmost to address part of the needs of our users in #Iran, who are facing anti-government protests and severe internet restrictions, through frequent and closely timed updates. 1/5 #DefyxVPN #VPN #DigitalPrivacy