🚩 Memory Challenge 18: Reminiscent
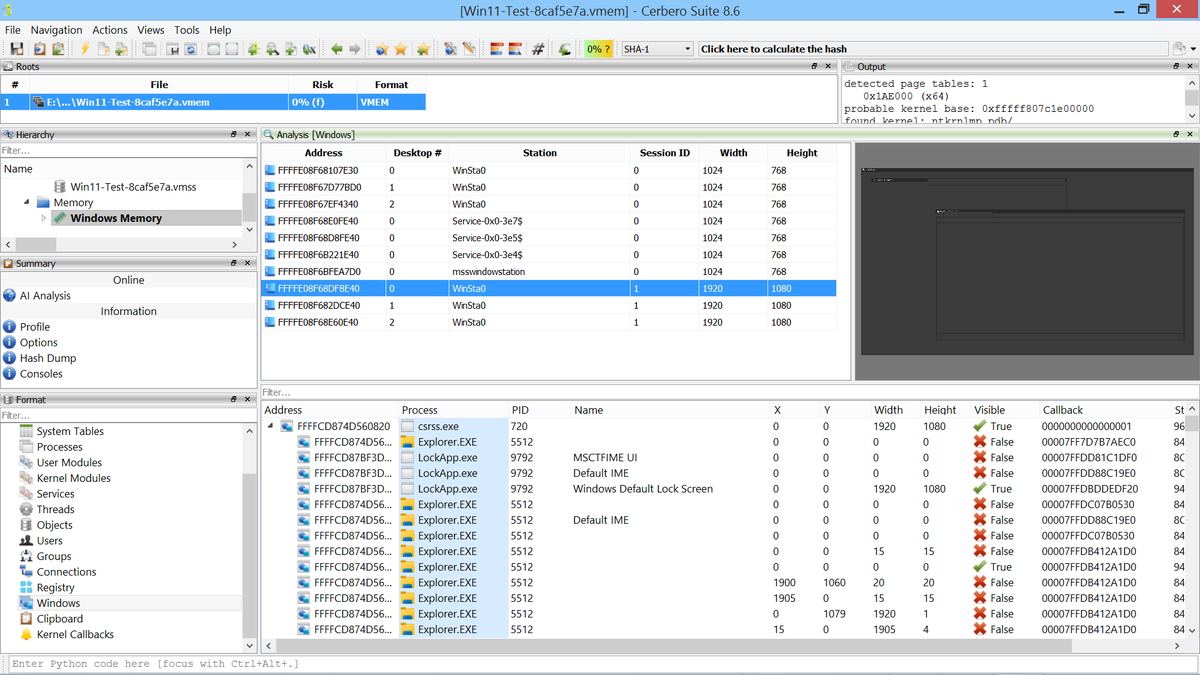
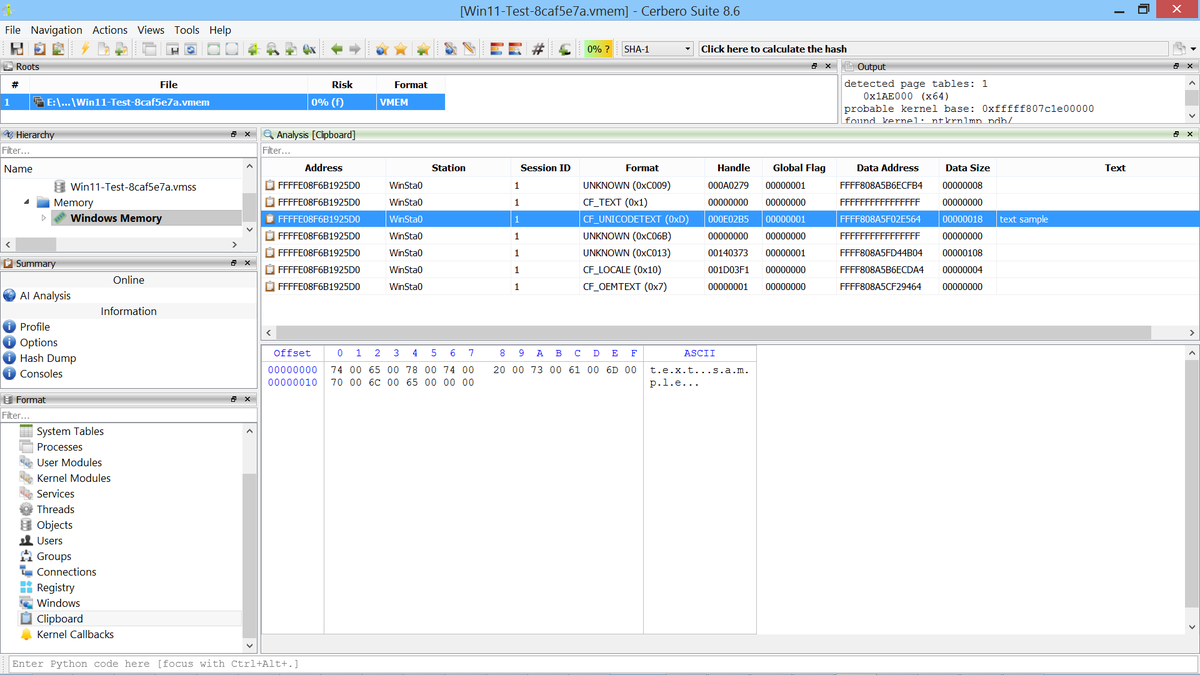
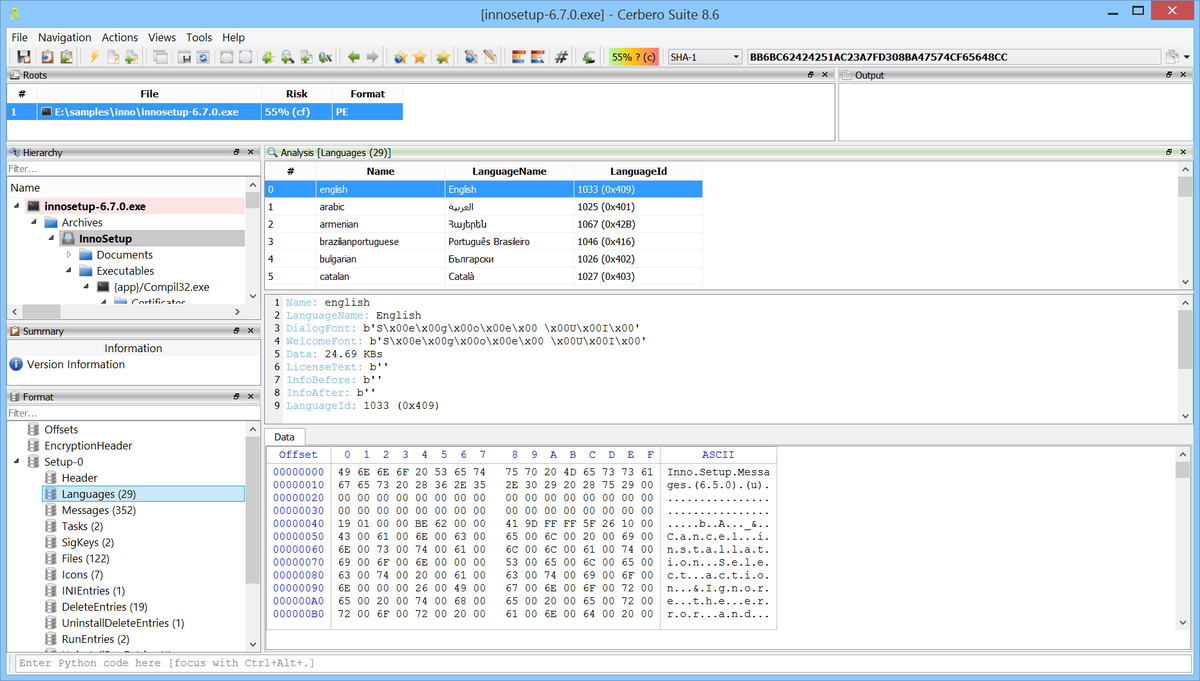
We're testing our Memory Analysis package (currently in beta: cerbero.io/packages/memor…) against various challenges available online.
We found this challenge on Hack The Box (app.hackthebox.com/challenges/Rem…), so credit goes to them for creating it.
The scenario is as follows:
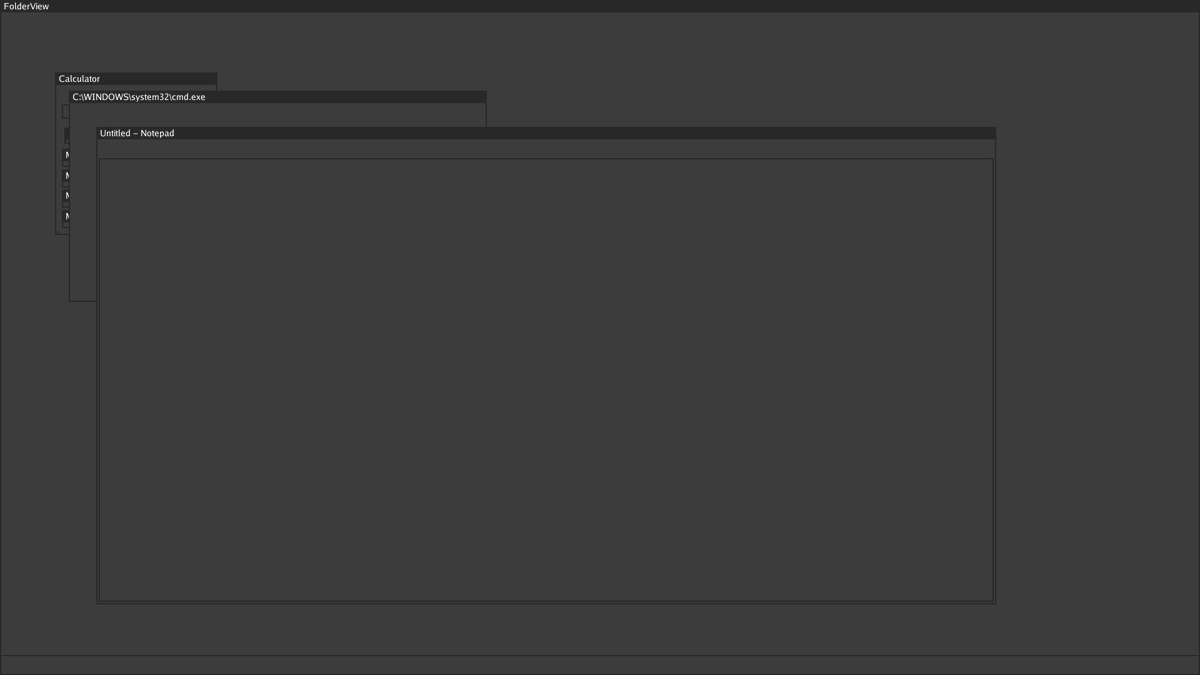
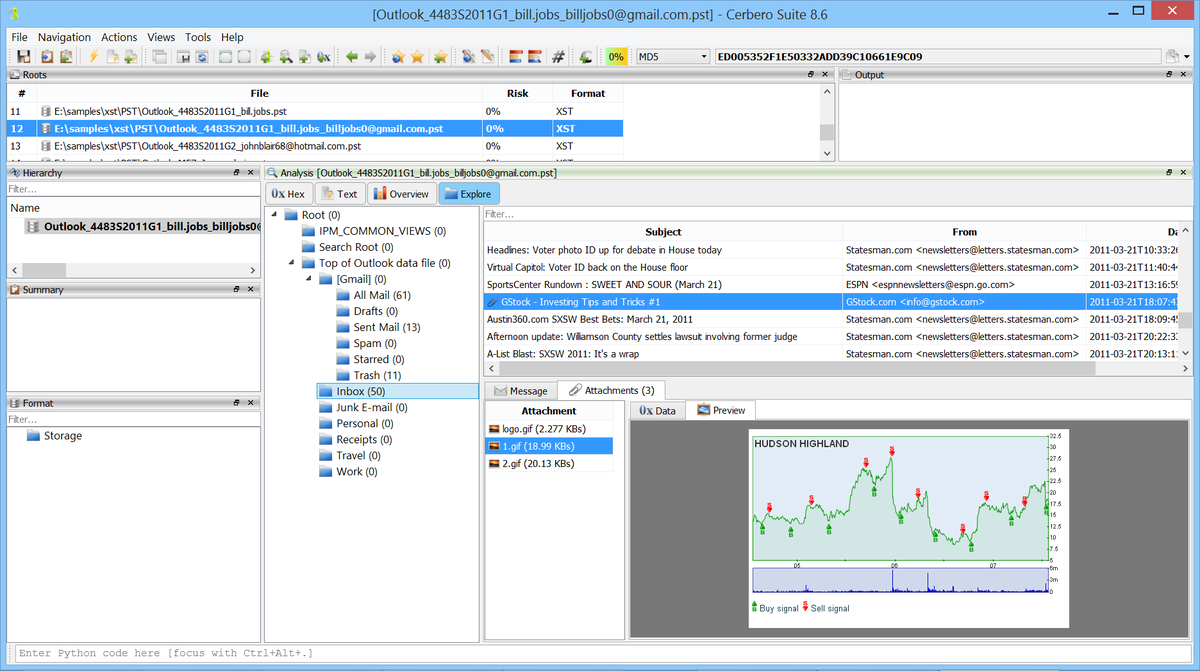
"Suspicious traffic was detected from a recruiter's virtual PC. A memory dump of the offending VM was captured before it was removed from the network for imaging and analysis. Our recruiter mentioned he received an email from someone regarding their resume. A copy of the email was recovered and is provided for reference. Find and decode the source of the malware to find the flag."
We tried to find the flag by decoding the malicious PowerShell stages, but since we couldn't download the payload from the final IP, we simply performed a string search and found the flag. Easy peasy.
English