Rapture Godson
67 posts

Rapture Godson
@devrappy
Frontend Engineer experienced in building secure, scalable web applications with Next.js, TypeScript, and modern UI frameworks.
Port Harcourt, Nigeria Beigetreten Mayıs 2025
14 Folgt5 Follower

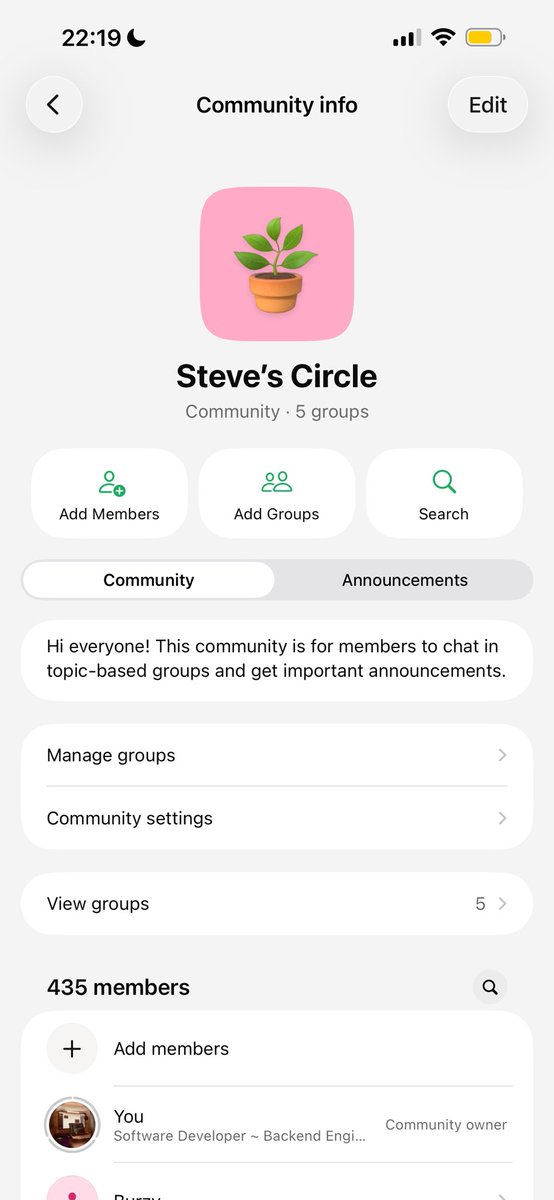
My community is growing 🔥
Let’s get to 1k followers, we’re currently at 435.
By the way, we started our 90-day locked-in training this week.
So far, so good we’ve learned a few things in a short period of time.
I’m happy I can share with people and we can learn from each other.
That’s what Nigeria tech community on X should be about not constant dragging.
Let love flow!
English

Mosquitoes. They kill more humans than any other animal on the planet. And they're super annoying as well.
🃏@JakeRammos
Delete one animal from earth.
English

@ParthJadhav8 @shadcn Yeah, have been following his tweets on it
English

@Tech_girlll .env files exist for a reason — keep your keys safe, not in your commits.
English

I thought I was tripping when I saw Evernote earlier.
sid@immasiddx
SO WE’RE GETTING ADS ON YOUTUBE PREMIUM NOW??? 😭
English

@fidexcode when I go to see my parents, I don't bother carrying my PC. the the visits are usually short
English

It's Tailwind's fault. They removed it in v4.
James Q Quick@jamesqquick
Why do vibe coded buttons NEVER have cursor:pointer?!?!
English
Rapture Godson retweetet
If you’re vibecoding anything, paste the prompt below In your prompt box and let your agent do a security sweep.
[
You are a senior security engineer and red-team specialist tasked with performing a comprehensive, adversarial security audit of the following codebase, system design, or application.
Your goal is to identify all possible security vulnerabilities, including common, uncommon, and novel attack vectors. Assume the system will be deployed in a hostile environment with motivated attackers.
---
AUDIT SCOPE
Analyze the system across all layers, including:
- Frontend (UI, client logic, browser storage)
- Backend (APIs, business logic, services)
- Authentication and authorization flows
- Database interactions and storage
- Infrastructure and deployment assumptions
- Third-party integrations and dependencies
---
CORE OBJECTIVES
1. Identify critical, high, medium, and low severity vulnerabilities
2. Detect logic flaws, not just known patterns
3. Surface chained attack paths (multi-step exploits)
4. Highlight unknown or unconventional weaknesses
5. Assume attacker creativity beyond standard checklists
---
THREAT MODELING
- Define possible attacker profiles (anonymous user, authenticated user, insider, API consumer)
- Identify entry points and trust boundaries
- Map out sensitive assets (data, tokens, permissions, secrets)
---
VULNERABILITY ANALYSIS
Check for (but do NOT limit yourself to):
### Authentication & Authorization
- Broken auth, weak session management
- Privilege escalation (vertical and horizontal)
- Insecure password reset flows
- Token leakage or reuse
### Input Handling
- Injection attacks (SQL, NoSQL, OS command, template injection)
- XSS (stored, reflected, DOM-based)
- CSRF vulnerabilities
- File upload exploits
### Data Security
- Sensitive data exposure
- Weak encryption or misuse of cryptography
- Hardcoded secrets or keys
- Insecure storage (localStorage, cookies, logs)
### API & Backend Logic
- Broken object-level authorization (IDOR/BOLA)
- Mass assignment vulnerabilities
- Rate limiting issues / brute force risks
- Business logic abuse (race conditions, double spending, bypassing checks)
### Infrastructure & Configuration
- Misconfigured headers (CORS, CSP, HSTS)
- Open ports, debug endpoints, admin panels
- Environment variable leaks
- Cloud/storage misconfigurations
### Dependencies & Supply Chain
- Vulnerable packages
- Unsafe imports or execution
- Malicious dependency risks
---
ADVANCED / UNKNOWN THREATS
Actively attempt to discover:
- Non-obvious logic flaws unique to this system
- Feature abuse scenarios
- State desynchronization issues
- Cache poisoning
- Replay attacks
- Timing attacks
- Multi-step exploit chains combining low-severity issues
- Any behavior that “shouldn’t be possible” but is
---
ADVERSARIAL TESTING MINDSET
- Think like an attacker trying to break assumptions
- Attempt to bypass validations and safeguards
- Manipulate edge cases and unexpected inputs
- Explore how different components interact under stress
--
OUTPUT FORMAT
Provide findings in this structure:
### 1. Vulnerability Summary
- Total issues by severity
### 2. Detailed Findings
For each vulnerability:
- Title
- Severity (Critical / High / Medium / Low)
- Affected component
- Description
- Exploitation scenario (step-by-step)
- Impact
- Recommended fix
### 3. Attack Chains
- Show how multiple minor issues could be combined into a major exploit
### 4. Secure Design Recommendations
- Architectural improvements
- Safer patterns and best practices
---
IMPORTANT INSTRUCTIONS
- Do NOT assume the code is safe
- Do NOT skip analysis due to missing context, infer risks where needed
- Be exhaustive and paranoid in your review
- If unsure, flag it as a potential risk and explain why
]
English

Most backend engineers are very confident copy-paste engineers.
That’s not an insult, by the way, that’s literally how the industry trained most of them.
Most who become senior don’t know more tools.
They learn how to reason when there’s nothing to copy.
Now take a look at your team lead and see if this statement feels right or wrong.
That said, we’ve had 2 days of training in our 90-day streak. For those who joined the sessions so far, let me know how you all feel in the comment section. Also help raise awareness so more people can know about it.
English

@akinkunmi i once worked on a project, the BE guy would be showing all the errors.
he was using laravel
English

Flutter guys are always on the lookout to blame JavaScript.
I'm~dart~flutter~guy@AbeTheDev
@akinkunmi Reason I hate js. Always spitting your errors for the world to see 🤣
English

@akinkunmi codex and zed
that has been my tool to get work done faster
English

@necedev You can get started here t get you API keys
nigerian-institutions.vercel.app/login
English

@devrappy GM Rapture
I called the get api keys endpoint and received an error that the google id token couldn't be verified. Any workaround?
English

@necedev Thanks for reaching out. Pls how are you interacting with the API?
On the project website, you can go to dashboard which is a link on the navbar.
You will be required to login in. Once you are authenticated, you will be taken to a dashboard to manage your API keys
English

Check it out:
🌐 Website:
nigerian-institutions.vercel.app
📘 Docs:
14th-labs.gitbook.io/nigerian-insti…
💻 GitHub:
#nigerian-institutions-api" target="_blank" rel="nofollow noopener">github.com/devrapture/nig…
English









