Angehefteter Tweet
Made this “Christmas & New Year playlist a year ago. Enjoy. The season is upon us )
deezer.page.link/yTnWjsDdrnqYUb…
English
Frenchie
2.5K posts

@dralexanders1
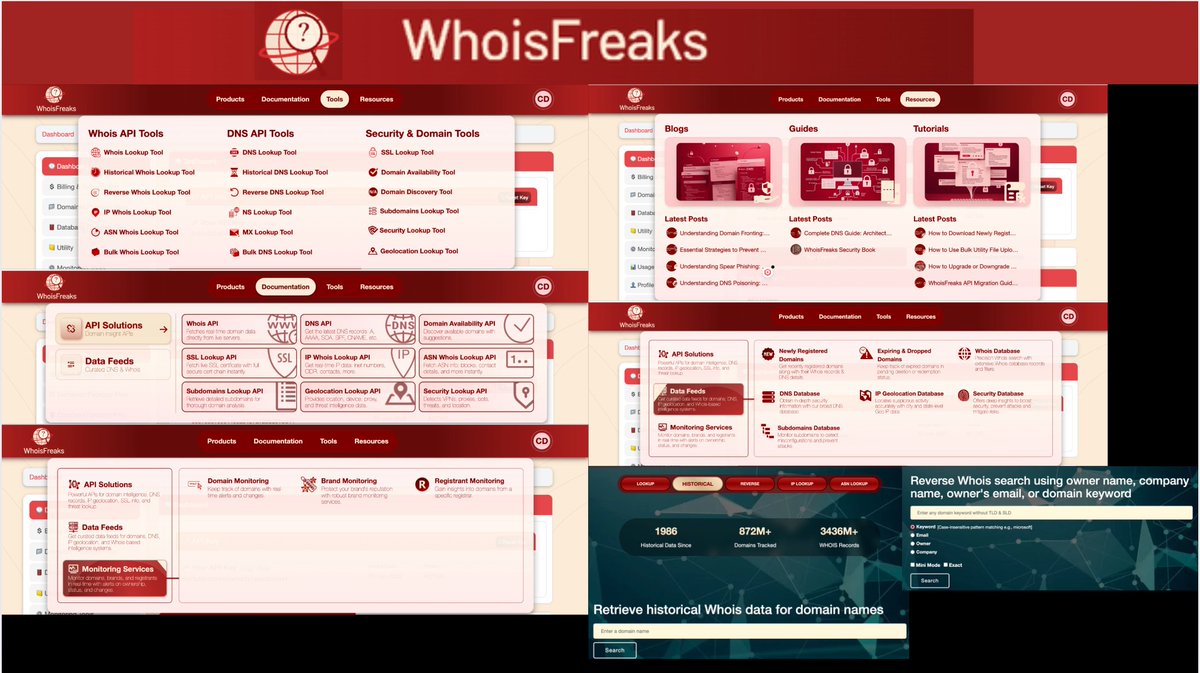
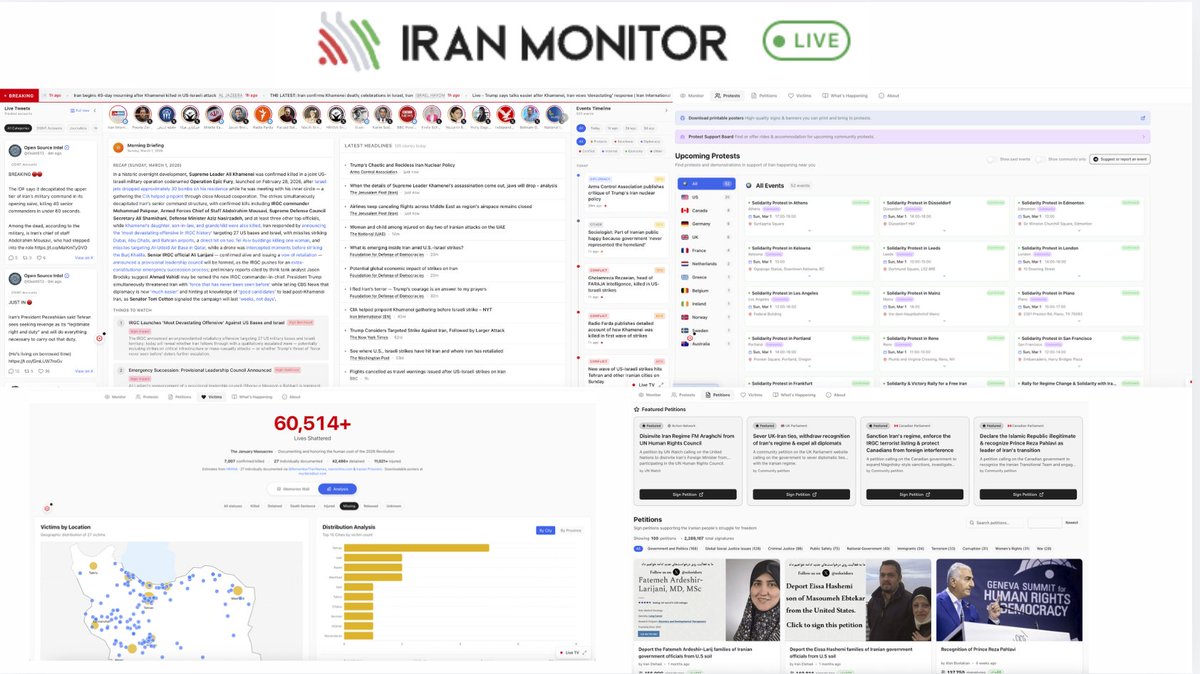
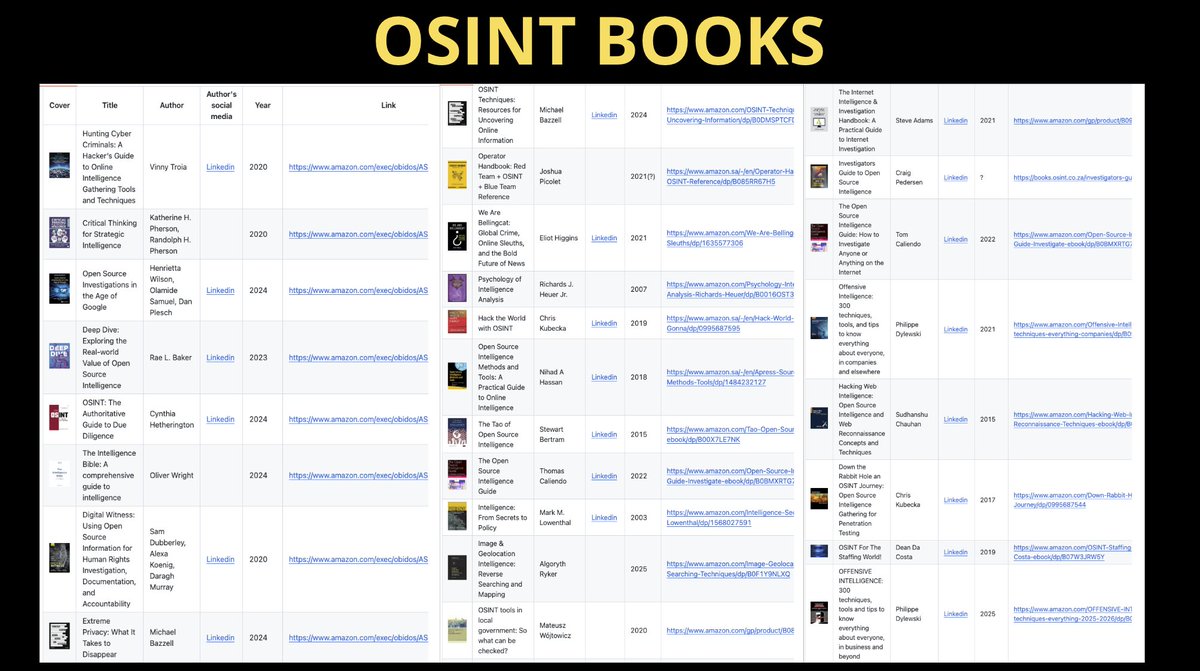
CCI, OSINT, Dark Web, Threat Intelligence; Got on my dead man's suit and my smilin' skull ring














@MedievalScholar Got any book recommendations on the HRE ?