encryptorium retweetet

STARKs are built on hash-based commitments and coding-theoretic machinery like FRI, which avoids the main Shor-vulnerable assumptions behind pairing- and discrete-log-based proof systems.
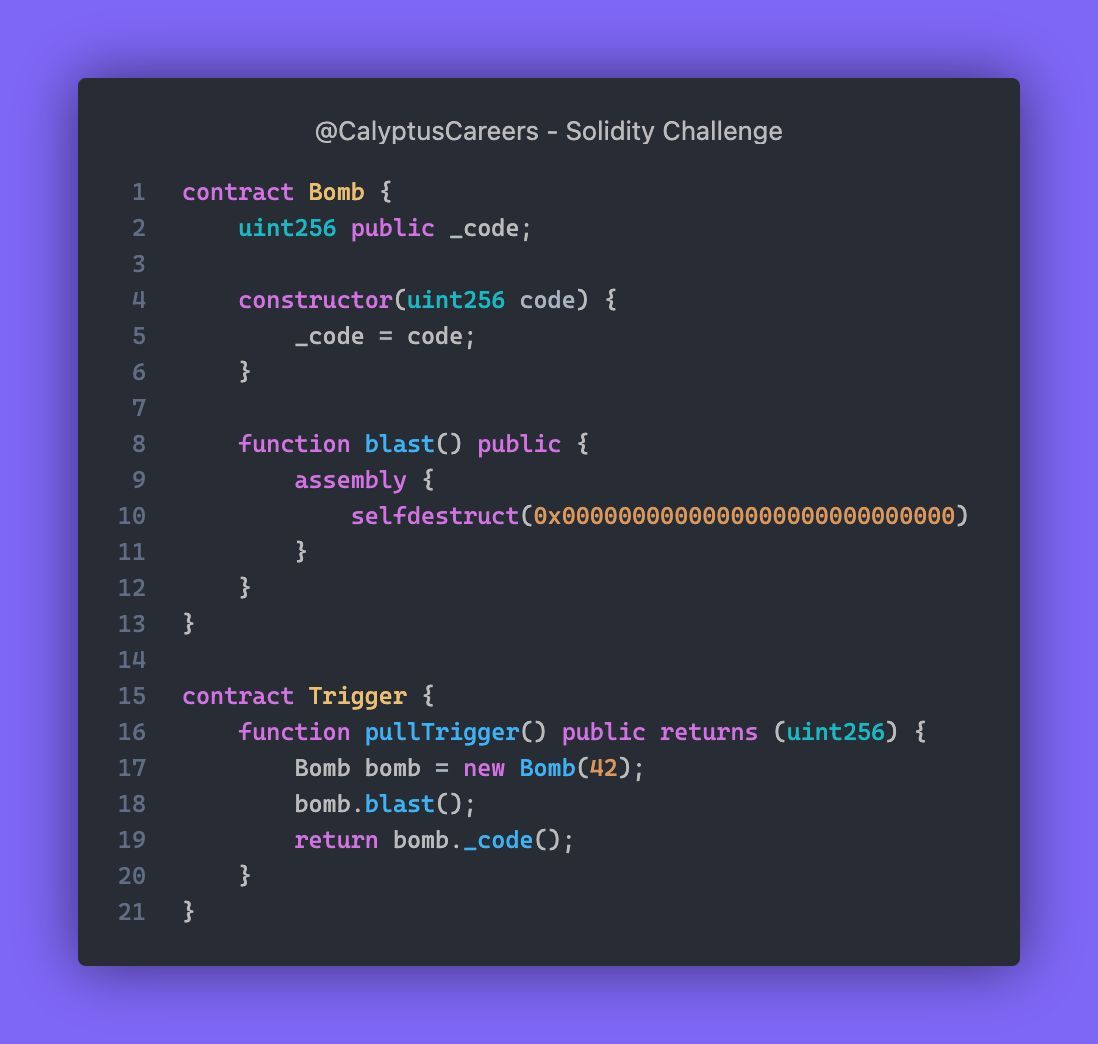
But some implementations add a final SNARK wrapper for cheaper on-chain verification. RISC Zero’s docs describe compressing a STARK proof into a Groth16 proof, and explicitly mark that path as not quantum-safe.
“We use STARKs” is not enough to make a system post-quantum. You have to trace the full verification pipeline.
English