Agustin Falaz
1.1K posts

Agustin Falaz
@ffakq
🇦🇷 Software Engineer




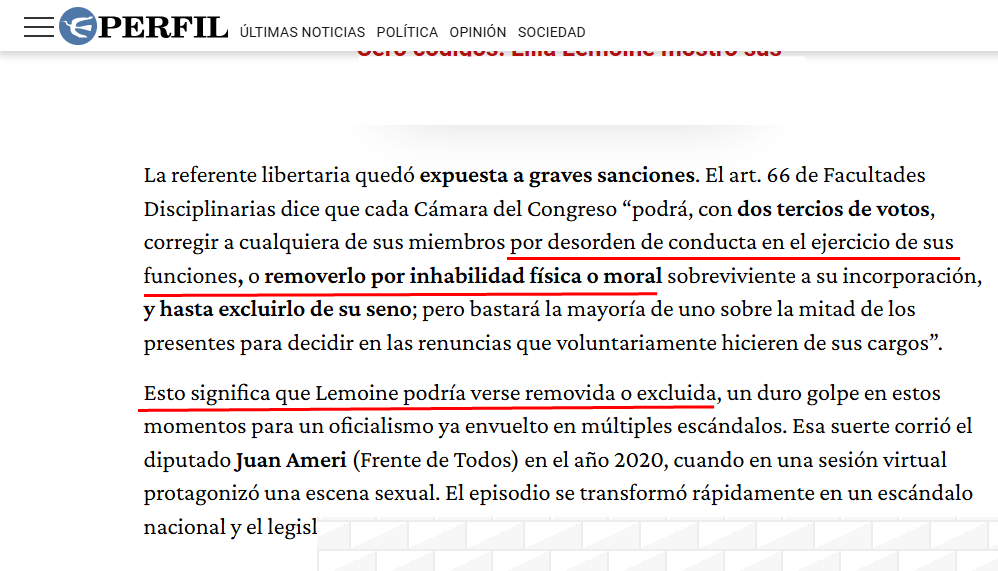
IMPUTARON A DEMIAN REIDEL, EXJEFE DE ASESORES DE MILEI, POR LOS GASTOS CON LA TARJETA DE CRÉDITO CORPORATIVA DE NUCLEOELÉCTRICA El economista Demian Reidel, exjefe de asesores del presidente Javier Milei y extitular de Nucleoeléctrica, fue imputado en la causa que investiga gastos realizados con tarjetas de crédito corporativas de la empresa estatal. El expediente analiza consumos en free shops, hoteles de lujo, discotecas y restaurantes en el exterior. La causa es impulsada por el fiscal federal Ramiro González, quien busca determinar si existieron “irregularidades penalmente relevantes en la utilización y administración de la tarjeta corporativa”. También fueron imputadas otras personas que tuvieron en su poder tarjetas corporativas de la compañía. Noticia en desarrollo (+) en Clarín: https://clar.inm/4nkcsKr






🚨 CYBERINTEL ALERT: MASSIVE LEAK OF STATE, EDUCATIONAL, AND MEDIA INFRASTRUCTURE – ARGENTINA 🇦🇷🏛️📂🔓 [STATUS: UNDER INVESTIGATION] One of the most critical postings regarding the digital infrastructure of the Argentine Republic has been detected. Threat actor Skull1172, representing the group EsqueleSquad TEAM, has announced the massive leakage of data originating from multiple government (.gob.ar), educational (.edu.ar), and media (Crónica: cronica.com) domains. The attacker claims that these compromises were carried out between 2024 and 2026, culminating in a consolidated database of over 80 million records, and threatens to release an archive exceeding 50 GB if the post receives sufficient support on the forum. 🏢 Affected Sectors: Federal and Provincial Government, Public University System, Media Outlets (Argentina). 👤 Threat Actor: EsqueleSquad TEAM (User: Skull1172). 📊 Total Exfiltrated Volume: 80,000,000 lines of credentials (Phone numbers, DNI/CUIL, email addresses, passwords, and vehicle license plates). 154,654 compromised webmail conversations. 📅 Report Date: May 6, 2026. ⚠️ Status: SAMPLE AVAILABLE / THREAT OF +50GB LEAK. 📊 Compromised Infrastructure and Domains 1. Government Entities and Citizen Services (.gob.ar) The actor lists over 900 affected pages. Among the most critical access points are: AFIP (auth.afip.gob.ar): 11.8 million claimed records. ANSES (servicioscorp.anses.gob.ar and APIs). Identity and Management: Mi Argentina (id.argentina.gob.ar, autenticar.gob.ar), GDE – Electronic Document Management (gde.gob.ar, cas.gde.gob.ar). Transport and Education: SUBE (sube.gob.ar, tarjetasube.sube.gob.ar), Progresar Scholarships (becasprogresar.educacion.gob.ar, with 650k records), and Road Safety. Provincial/CABA Portals: login.buenosaires.gob.ar, miba.buenosaires.gob.ar, AGIP (clusterapw.agip.gob.ar), Chaco (gobiernodigital.chaco.gob.ar). 2. University Sector (.edu.ar) Systemic compromise of academic self-service portals at universities such as: UNER, UNTREF, UNVM, UNTDF, UCU, USAL, UNO, UNPILAR, UPC, UPATECO, UNAM, UGD, and UNLAM. 3. Media Sector: Crónica (cronica.com) The group claims to have breached the news channel's administration panels, metrics, and FTP servers. Of extreme gravity is the actor's claim to possess confidential information ("sensitive panels") that allegedly exposes the receipt of government funds, thereby exposing data regarding the media outlet's employees. 🛡️ Immediate Response Recommendations 🔒 API Blocking and Rate Limiting: The National Cybersecurity Directorate and the affected ministries must implement strict Rate Limiting and authentication audits (Tokens/OAuth) on exposed ANSES and RENAPER endpoints to halt the ongoing scraping activity. 🔑 Mass Credential Reset: It is imperative to force password changes (for *Clave Fiscal* and *Mi Argentina* accounts) and mandate the use of Multi-Factor Authentication (MFA) for all government employees (within the GDE system) and citizens. Monitor: analyzer.vecert.io #CyberSecurity #Argentina #DataBreach #AFIP #ANSES #RENAPER #Cronica #EsqueleSquad #OSINT #CyberAlert #VECERT 🇦🇷🛡️⚠️🚨🏛️




Multiple security vulnerabilities affecting React Server Components and Next.js have been disclosed. We strongly recommend updating your applications immediately. Cloudflare WAF managed rules already mitigate the disclosed denial-of-service vulnerabilities, and we are investigating additional coverage for several other CVEs. developers.cloudflare.com/changelog/post…