starry retweetet
starry
2.7K posts

starry retweetet

Today we are launching a new vertical at the intersection of tokenization, private assets, and global retail access, including the US of A. 🇺🇸
Republic@joinrepublic
Republic is introducing Mirror Tokens, a new type of tokens tied to the performance of the world’s most valuable private companies. 🔓Unlock access: republic.com/mirror
English

@adi_baradwaj and yeah the avg vote credits should be your validators earned credits / optimal record earned credits
English

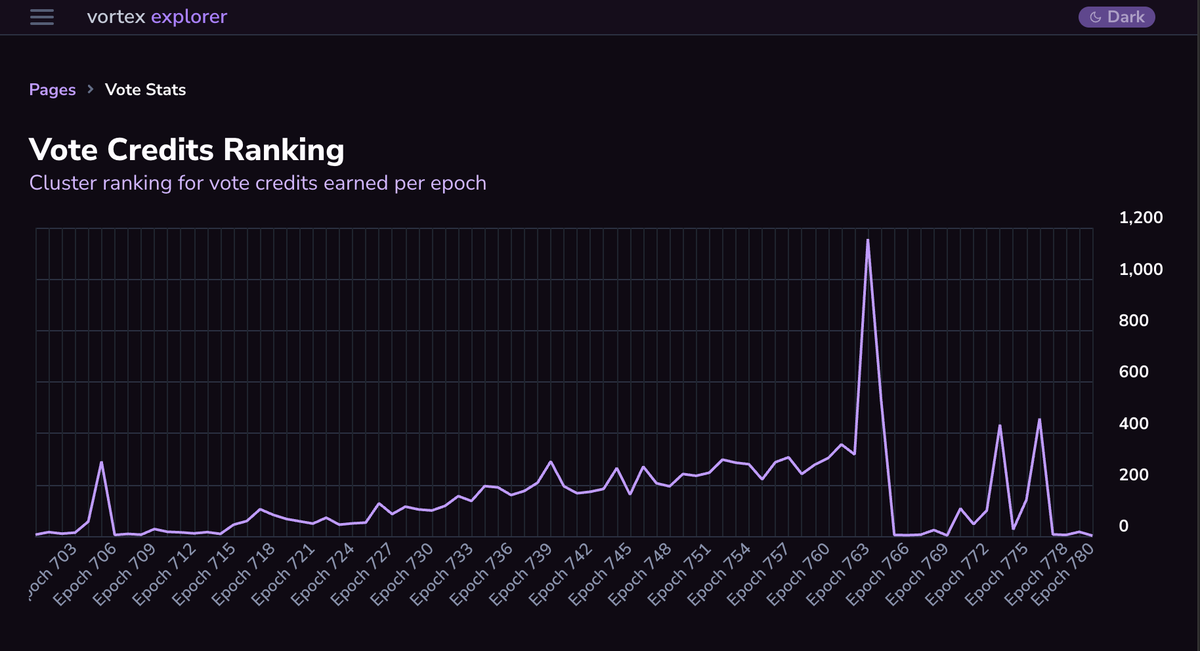
Solana validator operators, since TVC is getting activated in ~10hrs, I've added some new features for digging into vote latency to the vortex dashboard, check it out and lmk if you have any questions: app.vx.tools/cluster/vote-s…
English

avg credits = (credits earned for votes on the votable slots in a particular epoch) / 16 * votable slots (ie not a skipped slot) in that epoch.
for max credits, the idea is that some slots you can't possible get 16 credits because there are skipped slots immediately after the block you want to vote on. So I calculate the max based on the earliest block you could land your vote in.. and this becomes the "optimal record" which missed credits is measured against
English

@adi_baradwaj I can add if needed, any column(s) in particular that you were curious about?
English
starry retweetet

I happen to know Jordan and have for years. He is an amazing guy and a brilliant engineer.
Please share in hopes of finding him and bringing him home 🙏
dailymail.co.uk/news/article-1…
English

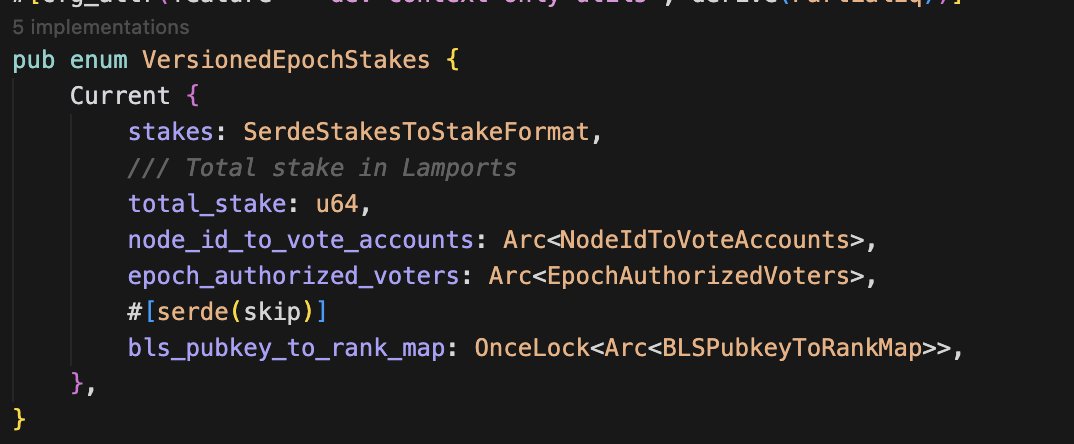
@cavemanloverboy @deanmlittle @DoctorBlocks @jacobvcreech @trentdotsol @apfitzge truth is in the source
English

@jstrry @deanmlittle @DoctorBlocks @jacobvcreech @trentdotsol hmm i recall this derivation now but @apfitzge told me otherwise
English

A lot of you don't understand @jacobvcreech and @trentdotsol when it comes to why ALTs are bad. Aside from the obviously terrible DX you've inevitably experienced in using them, allow me to enlighten you a little more about why this is an issue:
When you send a Legacy transaction, the Solana validator goes "Oh, you have a fully signed transaction ready to execute, let's verify your signature then see if you can actually pay for it." It knows relatively quickly if your transaction is properly formed, if your signature is legitimate, and whether or not you at least have enough lamports to pay for a failed transaction.
When you send a V0 transaction, the kind that contains ALTs, the Solana node must:
- parse out the address lookup tables
- lookup every single pubkey of every index you provided
- reserialize the transaction with all pubkeys populated
- then go and do all the things it already does for a Legacy transaction
All of this additional work happens before the node is able to verify a signature to efficiently check if you're sending a properly formed transaction. This means ALTs are actually a form of spam/DoS that you cannot feasibly charge money for, as you must do all of this work before you can even verify a signature.
The reason why ALTs exist is is because we cannot fit enough pubkeys into 1232 bytes of instruction data. If you lift this constraint to something more reasonable, not only do you no longer need ALTs to accomplish all of the existing use cases; by not removing them, you also worsen the DoS vector by allowing users to include even more ALTs, potentially making the validator do even more work for free.
The only decent argument I can think of for keeping ALTs once TX size increases is to avoid breaking any immutable programs that have been deployed to interact with them in the runtime. I am not aware of any such programs that actually exist today, because the Venn diagram of devs who have the skills to actually do so and devs who think it would be a good idea likely has zero overlap.
Being upset that you have to do 5 minutes of work on the client side is not a good argument against making the network faster and more secure. I hope if you are against the eventual removal of ALTs that this could help you to change your mind and understand why pushing for larger transaction sizes is the best course of action, both for DX and for the network. 🙏
English

@deanmlittle @cavemanloverboy @DoctorBlocks @jacobvcreech @trentdotsol Sorry but @cavemanloverboy is wrong, you can't recreate them from scratch at the same address. ALT addresses are derived from a recent slot and can only be closed when the slot is no longer "recent"
English

@deanmlittle @jacobvcreech @trentdotsol > Relaxing constraints makes free spam even easier
Not sure how you arrived at this conclusion. The SIMD I shared eliminates a certain type of free spam.
English

@deanmlittle @jacobvcreech @trentdotsol Yeah we opted to not sign expanded ALT addresses to avoid the pitfalls you described in your first post. But to make this safer we made ALT's append only and made it impossible to recreate ALT's at the same address. Can still misuse them but the attack surface is fairly small
English

@deanmlittle @jacobvcreech @trentdotsol 1) same thing already applies to fee payers being funded or not
2) I would describe it as expanding or resolving
English

@jstrry @jacobvcreech @trentdotsol 1) just reread it, and damn, that's also cooked because it creates a condition by which invalid TXs can later become valid.
2) how else would you describe "expanding" the account indices?
"can't charge" means "i can create a condition where I make you do extra work for free."
English

@deanmlittle @jacobvcreech @trentdotsol last I spoke with @alessandrod we are not super bandwidth constrained right now but if we ever were, ALTs would be useful for decreasing bandwidth because they are currently the only way to add accounts to a transaction without needing to send an additional 32 bytes over the wire
English

@deanmlittle @jacobvcreech @trentdotsol 1) sigverify always happens before account resolution
2) we don't "reserialize" the transaction
English
starry retweetet
starry retweetet
starry retweetet