Philippe Tremblay 🇨🇦🇫🇷 🇺🇦
2.5K posts


Philippe Tremblay 🇨🇦🇫🇷 🇺🇦
@philtrem2000
Husband, father, teammate. IT Product Owner and Solution Architect with a passion for cloud, code and empowering teams.






If you’re looking for ways to reduce the risk from compromised #NPM packages, here’s a solid post from Hacker News. I contains a few practical steps to harden your setup: - Use pnpm. It’s faster, takes less space, and blocks post-install scripts by default. Most of them are useless or shady anyway. - Set minimumReleaseAge to delay fresh packages. In recent attacks, that delay alone would’ve been enough to avoid pulling malicious versions. - On Linux, wrap your package manager in bubblewrap. Keeps the junk from touching sensitive files like ~/.ssh No tools to buy. No pipelines to rebuild. Just small changes that help. Hacker News post: news.ycombinator.com/item?id=452743… Config: #minimumreleaseage" target="_blank" rel="nofollow noopener">pnpm.io/settings#minim…



"Things that were typically off the table before are now on the table as far as what Iran will be targeting and that's what we need to be concerned with." Watch @HackingDave talk about the #Stryker cyber attack and why in time of warfare the private sector is in scope. @CNBC






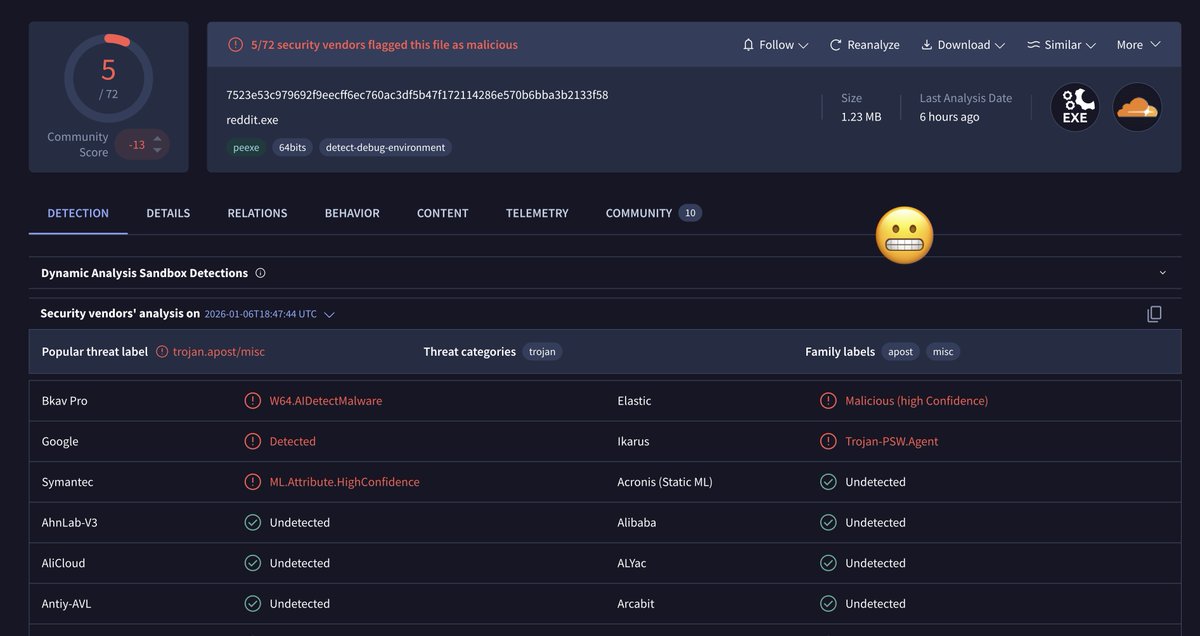
This is bad. Putty level bad. notepad-plus-plus.org/news/hijacked-…

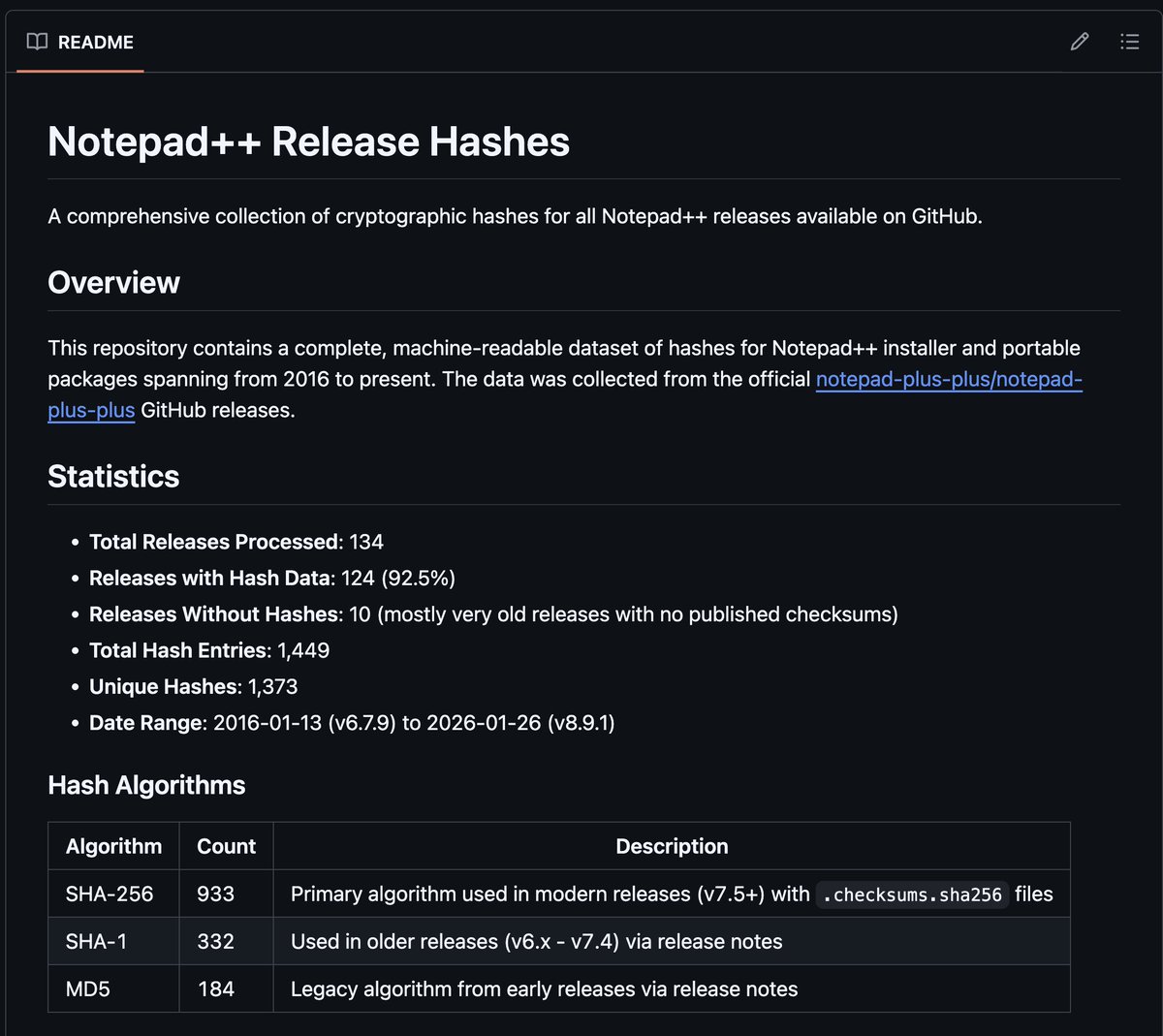
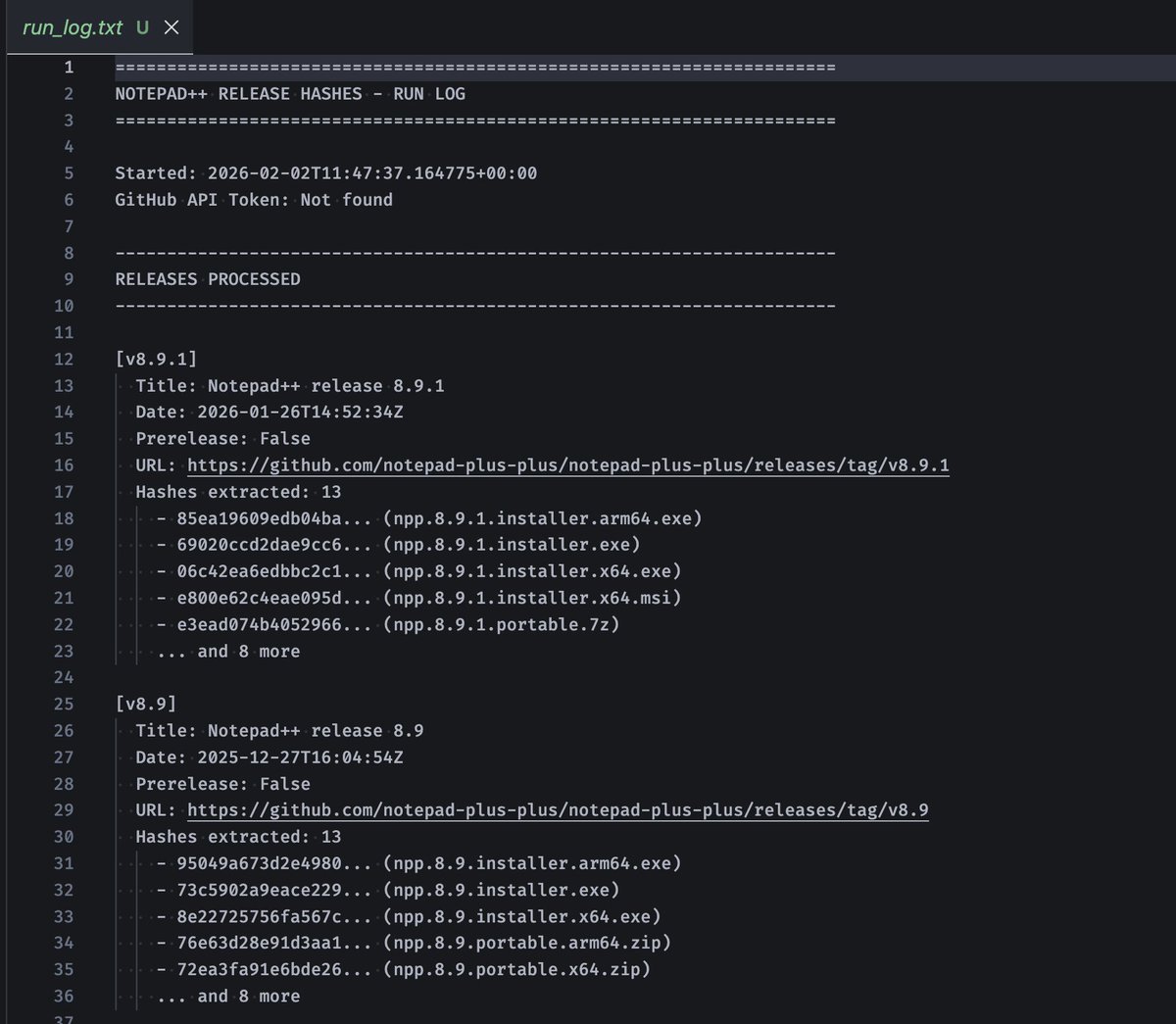

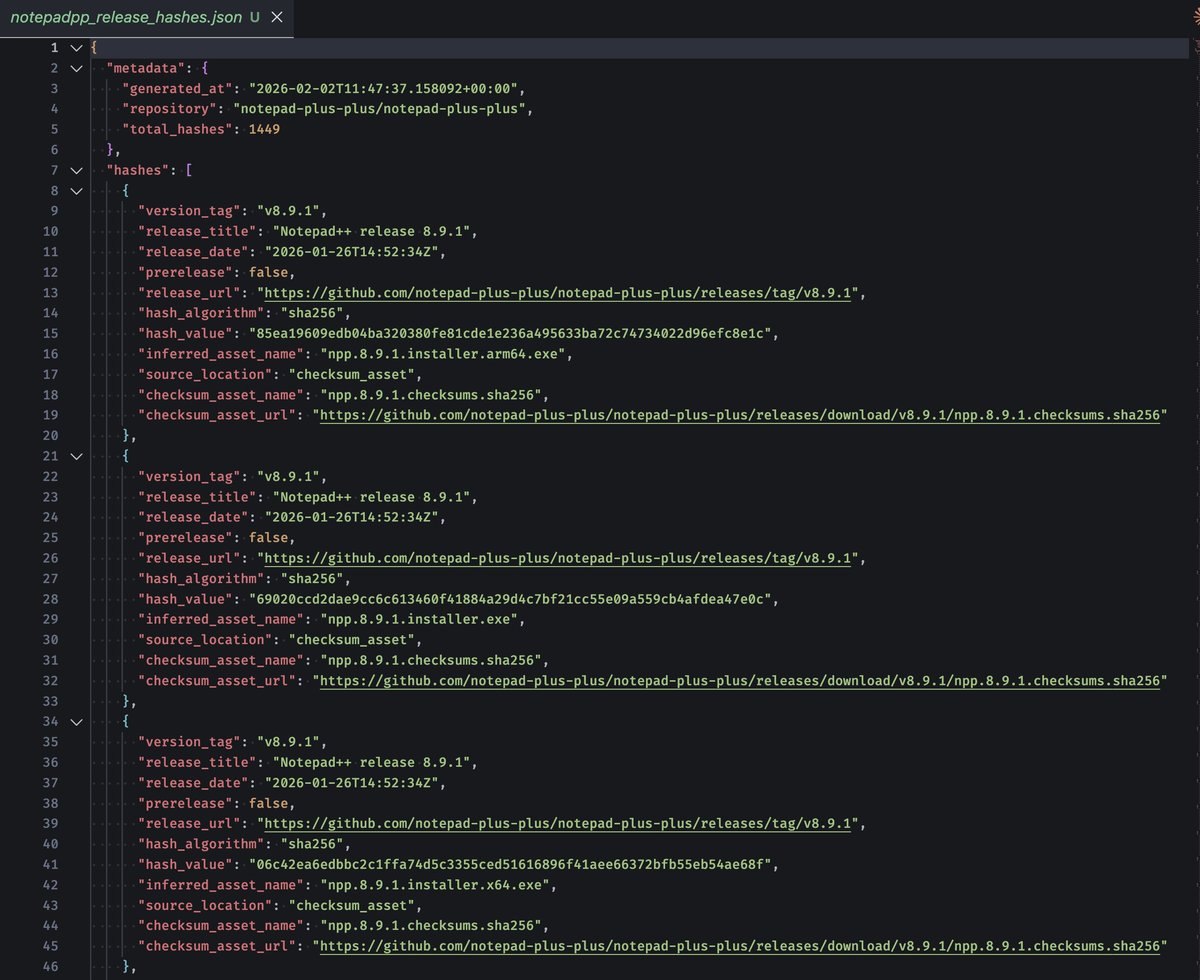
This is bad. Putty level bad. notepad-plus-plus.org/news/hijacked-…