Angehefteter Tweet
🦀Proof of Savage
28.5K posts


🦀Proof of Savage
@proofofsavage
Building minds that think. ☕️ Coffee Aficionado | ✈️ Globetrotter | 🧑💻 Tech Enthusiast | 🏡🇳🇿
Melbourne | Vienna | Auckland Beigetreten Şubat 2010
2.8K Folgt1.1K Follower
🦀Proof of Savage retweetet

The lab's mission targets perfect recall of conversations, faces, places, and data points, aiming to augment human memory beyond natural limits with searchable, lifelong storage.
Polymarket@Polymarket
BREAKING: New Harvard AI lab seeks $100 million in funding to help humans “remember everything”
English

Colombia 🇨🇴 is popular with digital nomads but here’s the honest take.
• Incredible coffee culture ☕
• Friendly, social people
• Affordable compared to the US, EU, and Australia
• Good internet in cities like Medellín and Bogotá
• Beaches, mountains, and jungle in one country
But it’s not perfect:
• Spanish helps a lot
• Safety depends on the neighbourhood
• Prices are rising in nomad hotspots
Still, many remote workers say the lifestyle here is hard to beat.
#DigitalNomad #RemoteWork #Colombia
English
🦀Proof of Savage retweetet

🦀Proof of Savage retweetet

🚨BIG EPISODE BESTIES!
Sacks is back, Fifth Bestie Brad Gerstner fills in for @Friedberg
-- Anthropic withholds Mythos: serious concern or another marketing stunt?
-- OpenClaw vs everybody: Are frontier model makers trying to kill the open source agent platform?
-- Anthropic's $30B run rate: fastest ever, do they already have market dominance in AI code?
-- The AI vibe shift: OpenAI reels as Anthropic rips
-- Iran War: ceasefire and Israel's influence on US foreign policy
(0:00) Bestie intros: Brad Gerstner joins the show!
(4:22) Anthropic blocks Mythos release for security concerns: serious or marketing stunt?
(24:07) Are OpenAI and Anthropic trying to kill OpenClaw? Does Anthropic already have market dominance in AI coding?
(42:20) Anthropic $30B run rate, fastest revenue ramp ever, the TAM for intelligence
(58:01) Major vibe shift: Anthropic ripping, OpenAI reeling
(1:10:12) Iran War: Ceasefire, Israel's influence, market impact
English

@T3chFalcon Is it only Signal? It should be the same for any messaging app which uses the notification store.
English

Deleted Signal Messages Might Still Be Recovered, The FBI Has Shown How
If you use an iPhone and value your privacy, you might be surprised to learn that the FBI recovered Signal messages from a suspect’s phone even after the app was deleted. The app was removed, but the messages could still be found.
How was this possible?
During a federal trial about an attack on an ICE detention center in Texas, FBI Special Agent Clark Wiethorn explained that they recovered messages by accessing Apple’s internal push notification database, even though Signal had already been deleted from the phone.
Here’s how it works: When you receive a Signal message and your notification settings let message content show on your lock screen, iOS saves those previews in your phone’s memory. Only incoming messages are saved this way, not outgoing ones, but the content can stay even after you delete the app and its messages.
This issue isn’t just about Signal. It’s with how Apple stores notifications for all messaging apps. Apps like WhatsApp, Telegram, and any others that show message previews on your lock screen could be affected too.
So, what is actually being saved?
iOS keeps a notification database to manage what you see on your lock screen and in the Notification Center. When an app sends a notification with a preview, like "John: Hey, are we still on for tonight?", that text is saved in a local SQLite database on your phone. This information stays there even if you clear the notification, delete the app, or use disappearing messages, because the operating system controls this storage, not the app.
Law enforcement can use forensic extraction tools to pull this database directly from your phone’s file system. They don’t need the app to do it.
How to protect yourself
There’s a simple solution that many people overlook:
For each app: Open Settings, tap Notifications, select the app, tap Show Previews, and choose Never.
To apply this to all apps (recommended): Go to Settings, tap Notifications, tap Show Previews, and set it to Never.
This setting tells iOS not to save message content in the notification database. You’ll still get alerts for new messages, but you won’t see previews on your lock screen. Most importantly, no one with forensic access to your phone will see them either.
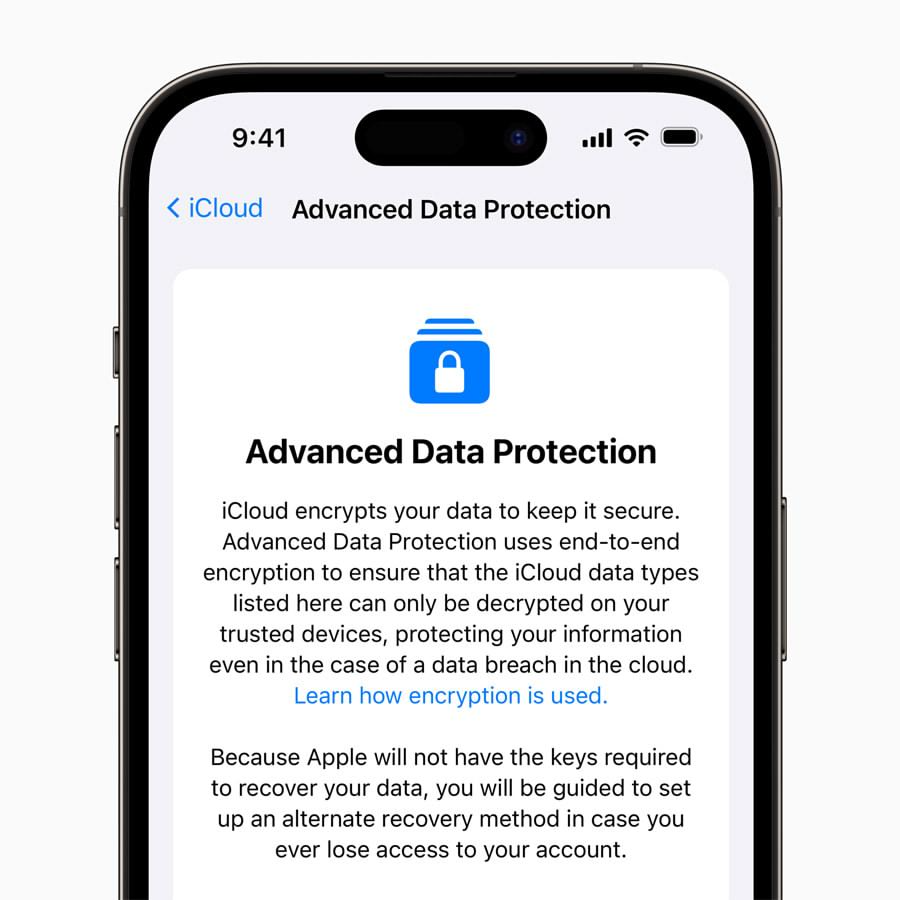
You should also turn on Advanced Data Protection in Settings under your name, then iCloud, then Advanced Data Protection. This adds end-to-end encryption for most iCloud data, including backups, Messages in iCloud, and Photos.



English
🦀Proof of Savage retweetet

🇺🇸 A new lawsuit claims WhatsApp has a backdoor that lets Meta employees and third-party contractors read your private messages without your knowledge or consent.
WhatsApp has spent years marketing itself as end-to-end encrypted.
The filing says that's not the whole story, and federal investigators are reportedly looking into it too.
Zuck's been here before.
Source: LiveMint


English
🦀Proof of Savage retweetet

THIS IS BIG.
A Bitcoin developer has built a working prototype that protects your wallet from quantum computers. Even if Bitcoin is forced to shut down part of its own security system to protect itself.
To understand why this matters you need to understand the problem first. Every Bitcoin wallet is secured by a cryptographic signature scheme built on elliptic curve mathematics.
The security assumption behind this system is that deriving a private key from a publicly visible public key requires computational work that classical computers cannot perform within any practical timeframe.
Quantum computers running Shor's algorithm can break that assumption. Google researchers published findings last week showing a quantum computer could compromise Bitcoin's core cryptography in as little as nine minutes, using significantly fewer physical qubits than prior estimates required.
The threat is not immediate but the timeline is compressing faster than most researchers projected.
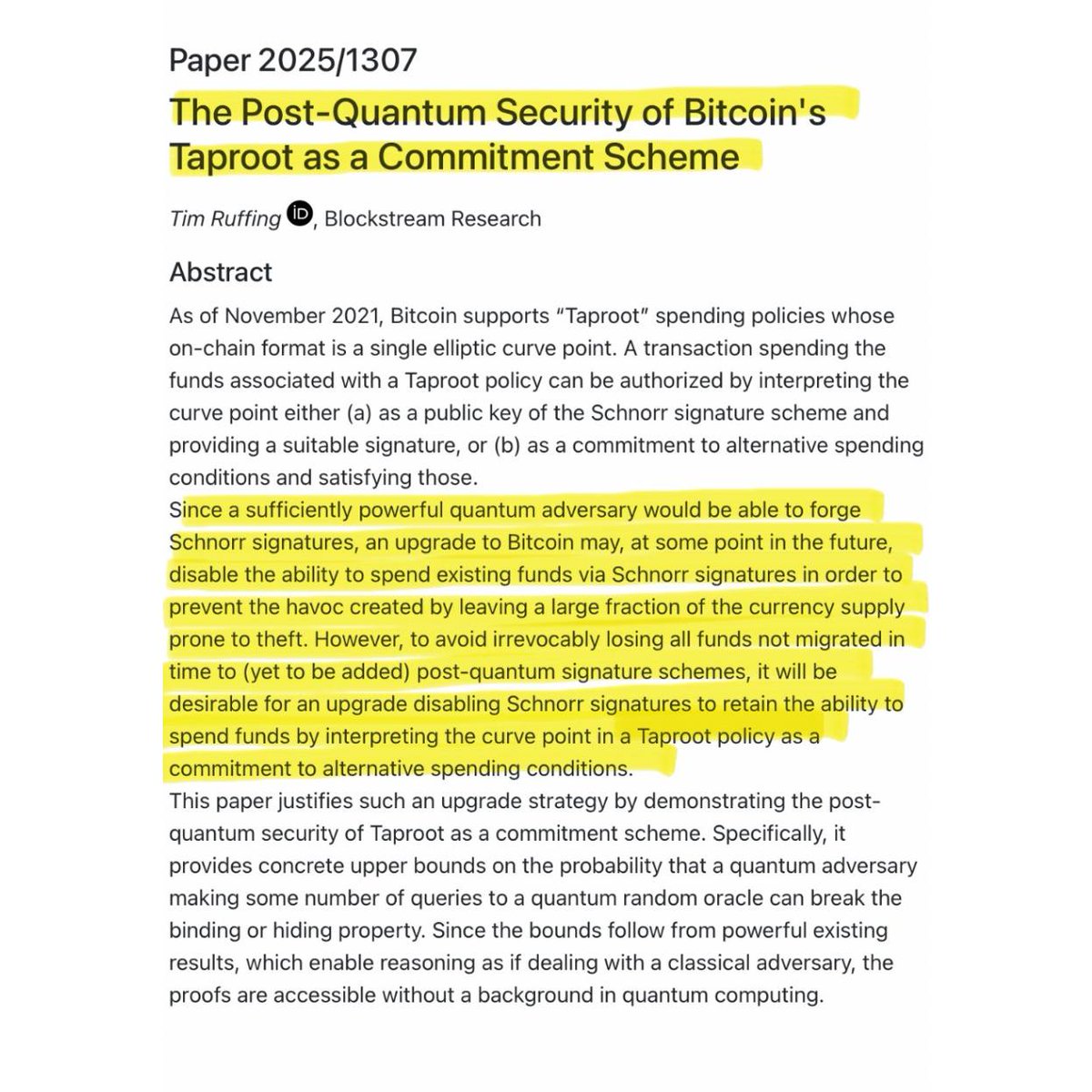
Now here is where it gets complicated. Bitcoin's Taproot upgrade, activated in 2021, improved transaction efficiency and privacy across the network.
But by design it permanently exposes the public key of every Taproot wallet on the blockchain. Because that public key is permanently recorded and publicly visible, a sufficiently powerful quantum computer could use it to derive the corresponding private key and drain the wallet at any point in the future.
Approximately 6.9 million Bitcoin across Taproot and older P2PK address formats are already in this exposed state.
The developer community has a contingency plan for this scenario. If quantum computers advance to the point where this becomes an active threat, Bitcoin could activate an emergency soft fork that disables the key path spend in Taproot, which is the specific spending mechanism a quantum attacker would exploit.
This closes the vulnerability before it can be exploited.
But this emergency response introduces a serious secondary problem that nobody had resolved until now. The vast majority of modern Bitcoin wallets, particularly single signature Taproot wallets, rely entirely on that key path spend mechanism and have no alternative spending path configured.
If Bitcoin disables that mechanism network wide, those wallets have no remaining method to authorize transactions. The funds inside them become permanently inaccessible, not stolen, but completely unspendable even by their rightful owners.
The same upgrade designed to protect users could permanently strand their funds.
This is the problem that Olaoluwa Osuntokun, chief technology officer of Lightning Labs, just solved with a working prototype posted to the Bitcoin developer mailing list yesterday. His solution uses a zk-STARK proof, which stands for zero knowledge scalable transparent argument of knowledge. In practical terms this means the following.
Every Bitcoin wallet is ultimately derived from a master seed, typically the 12 or 24 word recovery phrase generated when the wallet is first created. All keys in the wallet are mathematically derived from that seed following a deterministic standard called BIP-32.
Osuntokun built a system that generates a cryptographic proof demonstrating that a specific public key was derived from a specific master seed via the standard BIP-32 derivation path, without revealing the seed itself or any intermediate private key material.
The Bitcoin network can verify the proof and authorize the wallet owner to move their funds, bypassing the disabled signature mechanism entirely.
The prototype generates a valid proof in 50 seconds on a standard MacBook using Metal GPU acceleration, consumes approximately 12 gigabytes of RAM during proof generation, and produces a final proof of 1.7 megabytes. Osuntokun acknowledged the codebase is largely unoptimized and that a production implementation built specifically for this statement would run significantly faster and produce smaller proofs.
He also noted that multiple proofs could be aggregated into a single compact proof to reduce on-chain verification overhead.
Cryptographically relevant quantum computers capable of executing this attack do not exist today.
What has changed is that Google's latest research has materially lowered the estimated resource requirements for such an attack, and the practical timeline is now closer than the field previously assumed.
What is also new is that the developer community now has a working prototype of one of the critical tools needed to execute an emergency quantum defense without permanently locking legitimate holders out of their own funds.
A problem that has existed in theoretical discussions for years has now produced a concrete technical implementation.

English
🦀Proof of Savage retweetet
🦀Proof of Savage retweetet

🚨 BREAKING: The FBI has successfully extracted deleted Signal messages from a suspect's iPhone via notification storage, the place where all your notifications are stored for up to one month.
Notification storage stores data from all messaging apps, it's a big flaw in iOS. But there's a way to turn it off...

English
🦀Proof of Savage retweetet