pseca
217 posts


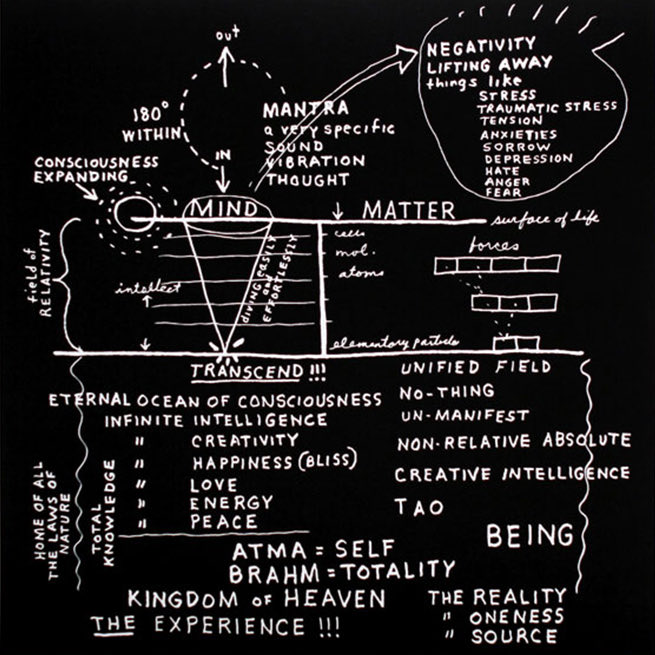
aesthetics are pure information compression and thus they run the world on all levels
platonic solids/fractals/etc. are compressions and embodiments of complex mathematical relationships and constraints
career choices & cultural movements too are aesthetic-first as "tech bro" or "trad wife" are high information density symbols that neatly package the qualia of the life you want to live

English
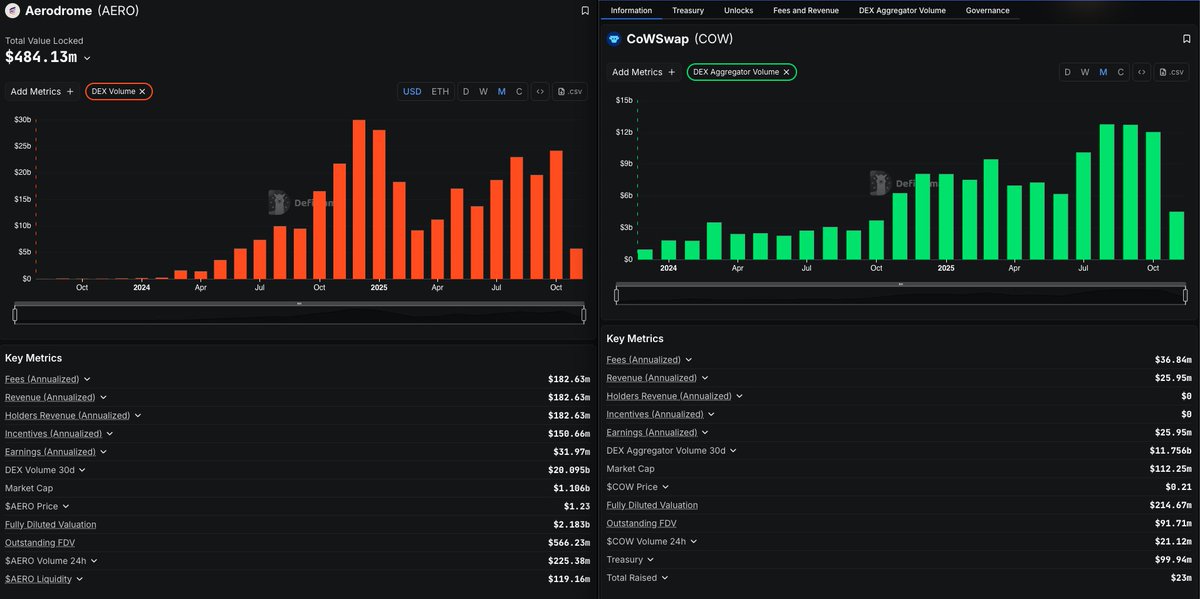
@koeppelmann @AerodromeFi @CoWSwap Main point of the cow token is to incentivise solvers. So pretty bad tokenomics
English

What do you think are the main factors that make @AerodromeFi roughly 10x more valuable than @CoWSwap?
English
@parsec_finance @0xShual Is this not more a function of the fact that there is so much more stable coins supplied? If you look at total USD borrows, major ATH
English

While onchain rates certainly look to have bottomed, they remain relatively suppressed relative to where we might expect them to be based on majors price action
Yet another sign of which flows are most instrumental in driving the market at present

parsec@parsec_finance
Despite strong price action in majors with BTC trading to ATHs briefly yesterday, onchain borrow rates remain subdued relative to earlier in the year
English
@dedaub The article mentions that contracts on @arbitrum are at risk, but how could a frontrun tx happen with a centralized sequencer? cc @pcaversaccio @deeberiroz @VennBuild
English

Just mitigated: The CPIMP Attack – a stealthy front-running exploit infecting 100s of DeFi proxies across many protocols
Attacker inserts hidden proxies that self-restore, spoof Etherscan, and lie dormant for high-value strikes
Tens of millions at risk
dedaub.com/blog/the-cpimp…
English
@raykov_krasimir @pcaversaccio If you wanted to check your contracts, you could look at the trace on tenderly and see if there is a malicious implementation in the middle of a call? @pcaversaccio
English

@pcaversaccio How were you able to identify all contracts impacted by this?
English

It gets even more fancy: the way Etherscan was tricked showing the wrong implementation contract is based on setting 2 different proxy slots in the same frontrunning tx. So Etherscan uses a certain heuristic that incorporates different storage slots to retrieve the implementation contract.
There is an old proxy by OpenZeppelin who used the following slot: `keccak256("org.zeppelinos.proxy.implementation")` = `0x7050c9e0f4ca769c69bd3a8ef740bc37934f8e2c036e5a723fd8ee048ed3f8c3`
We now also have the standard EIP-1967 slot `bytes32(uint256(keccak256('eip1967.proxy.implementation')) - 1)` = `0x360894a13ba1a3210667c828492db98dca3e2076cc3735a920a3ca505d382bbc`
So what happened is that the old OpenZeppelin proxy slot was written to with the benign implementation address _and_ the standard EIP-1967 slot was also written to with the malicious implementation address. Since Etherscan queries first the old proxy slot, it retrieved the benign looking one first and thus displayed it.

deebeez@deeberiroz
We @VennBuild just discovered a critical backdoor on thousands of smart contracts leaving over $10,000,000 at risk for months Along with the help of security researchers @dedaub @pcaversaccio, the seals team @seal_911 and others, we managed to rescue the majority of funds before the attacker could make their move. This is the story of how a sophisticated attacker (cough Lazarus) put backdoors in thousands of contracts and ALMOST got away with it 🧵
English
@deeberiroz @VennBuild @dedaub @pcaversaccio @seal_911 @arbiscan @arbitrum @offchain does this effect Arbitrum One? If so, have the updates been implemented?
English

We @VennBuild just discovered a critical backdoor on thousands of smart contracts leaving over $10,000,000 at risk for months
Along with the help of security researchers @dedaub @pcaversaccio, the seals team @seal_911 and others, we managed to rescue the majority of funds before the attacker could make their move.
This is the story of how a sophisticated attacker (cough Lazarus) put backdoors in thousands of contracts and ALMOST got away with it 🧵
English
@sparkdotfi I help maintain a contract which had $15k of USDC supplied into AAVE at the snapshot time (Arbitrum) but we have not received an allocation. It seems like this meets the criteria – is it possible that there is an error? @sparkdotfi @RuneKek
English