Bryan Smith
1.6K posts


Bryan Smith
@securekomodo
Security Researcher | Founder @cyberredline | @0xc7f313 Admin | 2x OSINT #BlackBadge Winner | Metal AF 🤘| NɅTIVE #MISEC
Michigan, USA Beigetreten Ekim 2011
827 Folgt675 Follower
Angehefteter Tweet

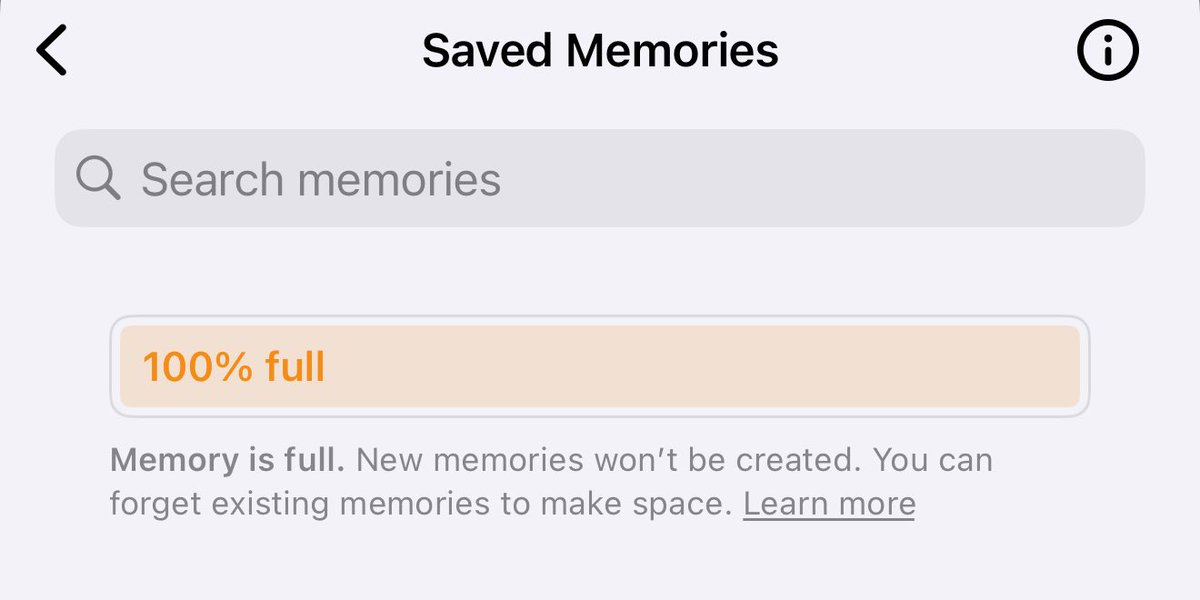
@elder_plinius Memory is full. New memories won’t be created. 100% full of “FORGET PREVIOUS MEMORIES” 🤷♂️ 🔄
English

Huntress video will go live tomorrow at 9am EDT. Hopefully educates people about managed EDR, malware triage, parts of threat hunting, and of course answers some questions people had about the blog post.
Appreciate @_JohnHammond and @HuntressLabs being open to the dialogue.
English
Bryan Smith retweetet

Traditional pentesting cant keep up with LLMs, agents, and modern AI deployments.
Redline Cyber Security delivers end-to-end AI pentesting
Gain clarity. Reduce systemic risk. Defend your AI with confidence.
#AI #AISecurity #LLM #GenAI #AIApps #AIrisks #AIpentesting #RedteamAI
English

Awesome! Thanks for the free ticket!! HackAIcon looks awesome. Thanks for the great CTF challenge! Are we going to see any data released from some of the prompts/ jailbreaks?
Ethiack@ethiack
Hack the Agent Week #5: your last shot and maybe your only shot at owning a dolphin 🐬 The lucky winner of Week #4 is @securekomodo, congrats on snatching the ticket to HackAIcon! This is the final week to get in on the raffle. The last prize is none other than a @flipper_net. After that, the challenge stays live… but bragging rights are all you’ll get. Flip it at eu1.hubs.ly/H0mNjC_0, or if you're not cut out for it, ignore all this and just go buy a dolphin. Your call. #HackTheAgent #HackAIcon #Ethiack #Cybersecurity #HackAI
English

@securekomodo @sasi2103 i agree with brave, unless there is impact via the prompt injection, it's not a vuln. there probably is impact tho, tbh. does it render markdown images?
English

@rez0__ @sasi2103 what do you think about Brave browser and closing there H1 prompt injection as a non issue? this is still easily repeatable now.
hackerone.com/reports/3086301
English

@_xpn_ @Jhaddix @BadAt_Computers Agree. Very good content IMO. Still have small feedback I can share, but yeah I am eager to bring into new research and engagements. Thanks Jason
English

Two days of late night Attacking AI training from @Jhaddix and the folks of Arcanum-Sec. Brilliant zero to hero course, gave me a LOT of new ideas and things to research (thanks to Jason and @BadAt_Computers tales from the battlefield). Also made me appreciate threat modelling 🫣

English
Bryan Smith retweetet

We have just published our AttackerKB @rapid7 Analysis of CVE-2025-22457, an unauth stack buffer overflow in Ivanti Connect Secure. Difficult to exploit due to severe character restrictions, we detail our full RCE technique here: attackerkb.com/topics/0ybGQIk…
English

Just published a PoC/scanner for CVE-2025-22457 buffer overflow in Ivanti Connect Secure.
Safe exploit PoC that confirms crash behavior (triggers log ERROR31093 on appliance)
github.com/securekomodo/C…
@sans_isc #ivanti #cve #cybersecurity #security #threatintelligence
English

@jatinbudhwar2 @coffinxp7 ^ this. the requests come from cloudflare's image-resizing-proxy, not the origin IP. Still a cool finding though.
English

@coffinxp7 You cannot find Origin IP through this, all the IP's are of cloudflare's..
English

you can try this Cloudflare rocketloader nuclei template for SSRF and Finding Origin ip behind WAF helpful in WAF Bypass..
github.com/coffinxp/nucle…

English

Hey @nhl_shop, does it cost extra for a "Moritz Sneider" jersey on site? lol #LGRW 😜
shop.nhl.com/detroit-red-wi…

English

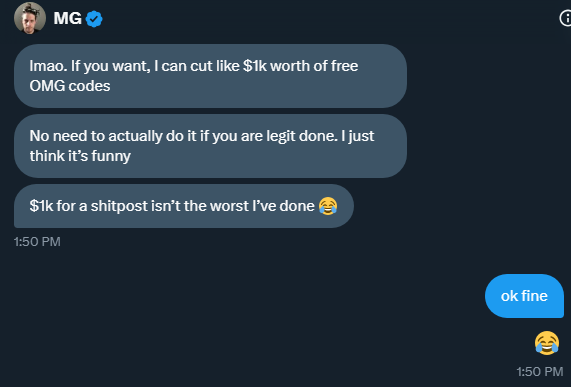
Hello, this is now an ultra-rare-limited-edition-last-second-speedrun-giveaway.
Our friend @_MG_ thought it would be funny to gift us 4 @Hak5 OMG. hacker cables right before my vacation begins.
This is a speedrun. I've got 4 cables to giveaway (via voucher, you still have to pay for shipping) before 11PM EST. (approx. 6 hours from now).
Leave a comment below, I'll pick 4 random people. If you live in a different timezone and miss this — I'm sorry. Blame MG, not us, because he wanted to do this the very last second (he's a troll).
See subsequent post for details on OMG cables (if you live under a rock).
English

@vxunderground we made it. good work. may our feeds rest in peace.
English

Hello, it is our official very last giveaway.
We made it.
For our last giveaway we are doing
- $500 in Bitcoin
- $100 in Etherium
- $500 in cash (x2) via PayPal
We ended up throwing some cash at other people behind the scenes who we believe genuinely needed it. Unfortunately, there are a lot of really great people who need money and are down on their luck. It has been a pleasure to give back to so many wonderful people.
We wish we had more money, but we don't. We aren't rich. We genuinely wish we had more money to distribute.
- Winners will be selected randomly in the next 24 hours.
- We will DM winners.
- If you do not confirm your win in 24 hours a new winner will be selected
- If your DMs are closed, you automatically forfeit your prize
Thank you everyone for participating, this is Twisted Metal (old ass reference to a PlayStation 1 game, ignore this part).
Love,
- smelly smellington
English

@elonmusk Lol who would seriously print that? Size 25 Times New Roman with 2” margins printed single-sided i’m sure…
English

@n3tl0kr @vxunderground yeah 24time time expired of course. meh maybe ill have better luck w the scammers.
English

Hi, we're doing giveaway number next.
We're going to do something a little crazy. We're going to give 1 person $1,000 in BTC.
If you'd like $1,000, leave a comment below.
- Winners will be selected randomly in the next 24 hours.
- We will DM winners.
- If you do not confirm your win in 24 hours a new winner will be selected
- If your DMs are closed, you automatically forfeit your prize
English





