The Malware Files
127 posts


The Malware Files
@themalwarefiles
Story-driven and technical breakdowns of the world’s most fascinating malware
CyberSpace Beigetreten Nisan 2025
1 Folgt11 Follower

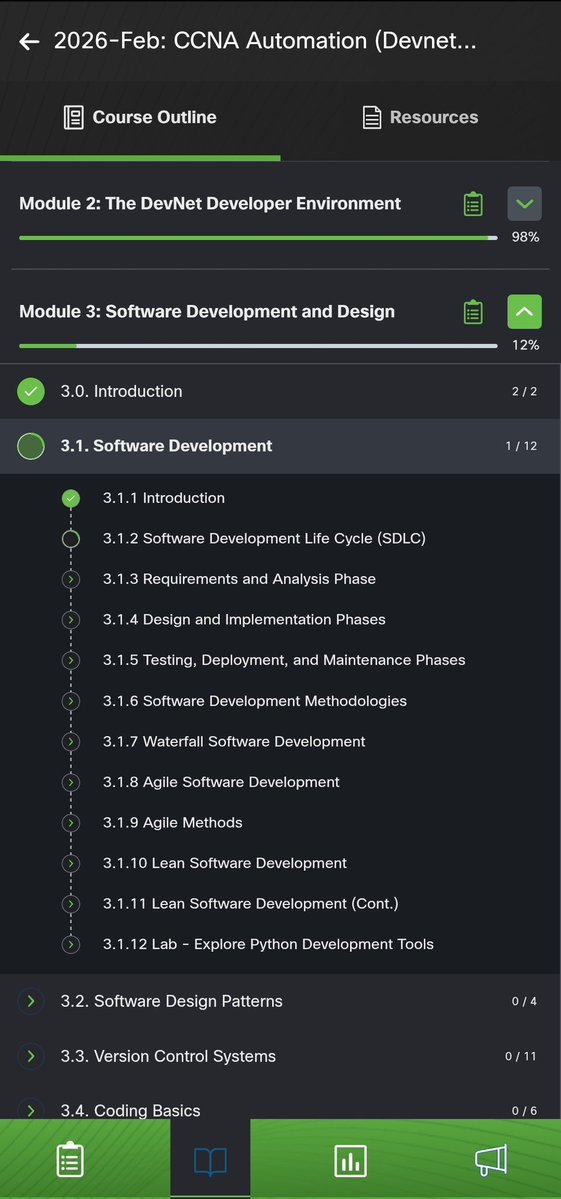
Day 89&90
Completed CCNA: ITN and Course 3 from Google's IT Support. Started the Devnet Associate course, learning about software development, APIs, Network and Security Automation
@ireteeh @OnijeC @segoslavia @Ejikeetolue @_DeejustDee @jay_hunts
#100DaysofCyberSecurity


English

Doing my first volunteering today🌚
Dr Iretioluwa Akerele@ireteeh
Hello Cyber friends, are we locking in this weekend or we are going out for enjoyment?
English

2 years in Cybersecurity today.
There’s a whole lot of story in between but God has been faithful.
Today, I’m genuinely proud of how far I’ve come.
I’m grateful to my mentor Dr. @ireteeh and everyone who’s contributed to my growth. 🙏
Year 3, let’s get it!


English

CVE? CVSS? Mitigations? Cybersecurity terms can be overwhelming, especially for a newbie. In this article, @Dhanush_Nehru helps you to unlock the mystery behind some of these buzzwords in vulnerability management, and breaks them down for you to understand them better.
#cybersecurity #vulnerability #cve #cvss
themalwarefiles.com/the-no-nonsens…
English



SikoMode is a Nim-compiled infostealer that checks for a C2 connection the moment it runs. No connection, and it quietly wipes itself from disk, leaving no trace. If it does connect, it reads a JPEG off the desktop, encrypts it with RC4 using a key pulled from a separate file, and exfiltrates it.
In this writeup, Sagar Joshi walks through the full analysis in IDA and x64dbg to show exactly how this beautiful nightmare pulls this off.
#MalwareAnalysis #PMAT #CyberSecurity #ReverseEngineering #InfoSec
medium.com/the-malware-fi…
English

In the world of Android cybersecurity, static analysis gets a lot of red flags letting you know an app is malicious. But what if the app is literally clean until its opened?
In this piece, Ruslan Mirzayev explains the role of the Reflection API, and how this tool has unfortunately been used in some of the worst ways possible, and how to defend yourself against it (hopefully).
#android #malware #reflection #api #google
medium.com/the-malware-fi…
English

Commercial Spyware and surveillance has been on the rise lately. From NSOs Pegasus, to Sherlocks Candiru, the race is just getting started that legally puts cyberweapons in the hands of anyone with enough money to buy them.
In this post, @bevijaygupta opens up the market of these paid cyberweapons, and gives a tour through the lens of India, including its impact on the Subcontinent.
#spyware #malware #india #law #pegasus
themalwarefiles.com/the-rise-of-co…
English

SVCStealer is an infostealer that targets Windows users, and collects credentials, crypto wallets, messaging data and even takes screenshots. In this analysis, mapol takes you through what makes this malware tick, and even tips on protecting yourself.
#svcstealer #malware #cybercrime #infostealer #cybersecurity
medium.com/the-malware-fi…
English

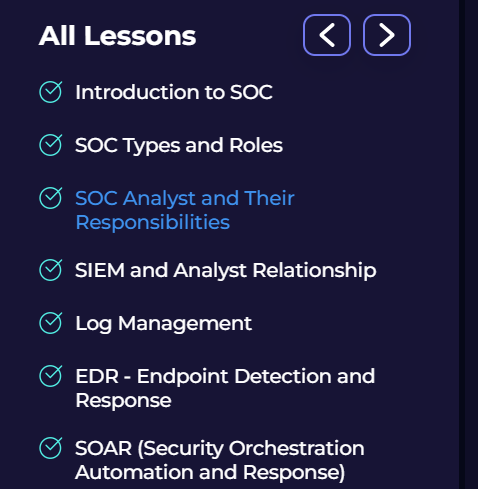
Day 41/100 Days of Cybersecurity
Today, I continue the SOC Fundamentals Course from
@LetsDefendIO
#BlueTeamer #100DaysOfCyberSecurity
@jay_hunt
@cyberjeremiah
@ireteeh
English