Knock Knock 🔮 ♞
15.5K posts


Knock Knock 🔮 ♞
@SuddenlyJon
AI Litigator | Utility Player | SprackSlips™️ | 🇺🇸 America First | InfoSec ♔ OSINT | ☕️





LiteLLM HAS BEEN COMPROMISED, DO NOT UPDATE. We just discovered that LiteLLM pypi release 1.82.8. It has been compromised, it contains litellm_init.pth with base64 encoded instructions to send all the credentials it can find to remote server + self-replicate. link below


NEW: Kentucky family rejects $26 million offer to convert part of their farm into a data center despite the offer being about 10 times the going rate for farmland in the area. "If it's my way, I'll stay and hold and feed a nation. 26 million doesn't mean anything." "As long as I'm on this land, as long as it's feeding me, as long as it's taking care of me, there's nothing that can destroy me if I've got this land." Video: Local 12 WKRC

Amputee Cornhole Player Charged in Fatal Shooting in Maryland A professional cornhole player, Dayton James Webber, 27, has been accused of fatally shooting Bradrick Michael Wells, 27, during an argument in La Plata, according to police. Investigators say Webber was inside a Tesla SUV when he allegedly shot Wells, who was seated in the passenger seat. Authorities say Webber then stopped the vehicle and asked two passengers in the back seat to help remove Wells, but they refused and exited the car before calling police. Officials say Webber fled the scene with Wells still inside the vehicle, and the victim’s body was later discovered in a yard along Newport Church Road in Charlotte Hall, where he was pronounced dead. Webber was later located at a hospital in Charlottesville and arrested as a fugitive. He is expected to be extradited to Charles County to face multiple charges, including first- and second-degree murder. Authorities say there is no evidence anyone else was involved, though questions remain about how Webber, a quadruple amputee, was able to operate the vehicle or firearm. VIA: @fox5dc

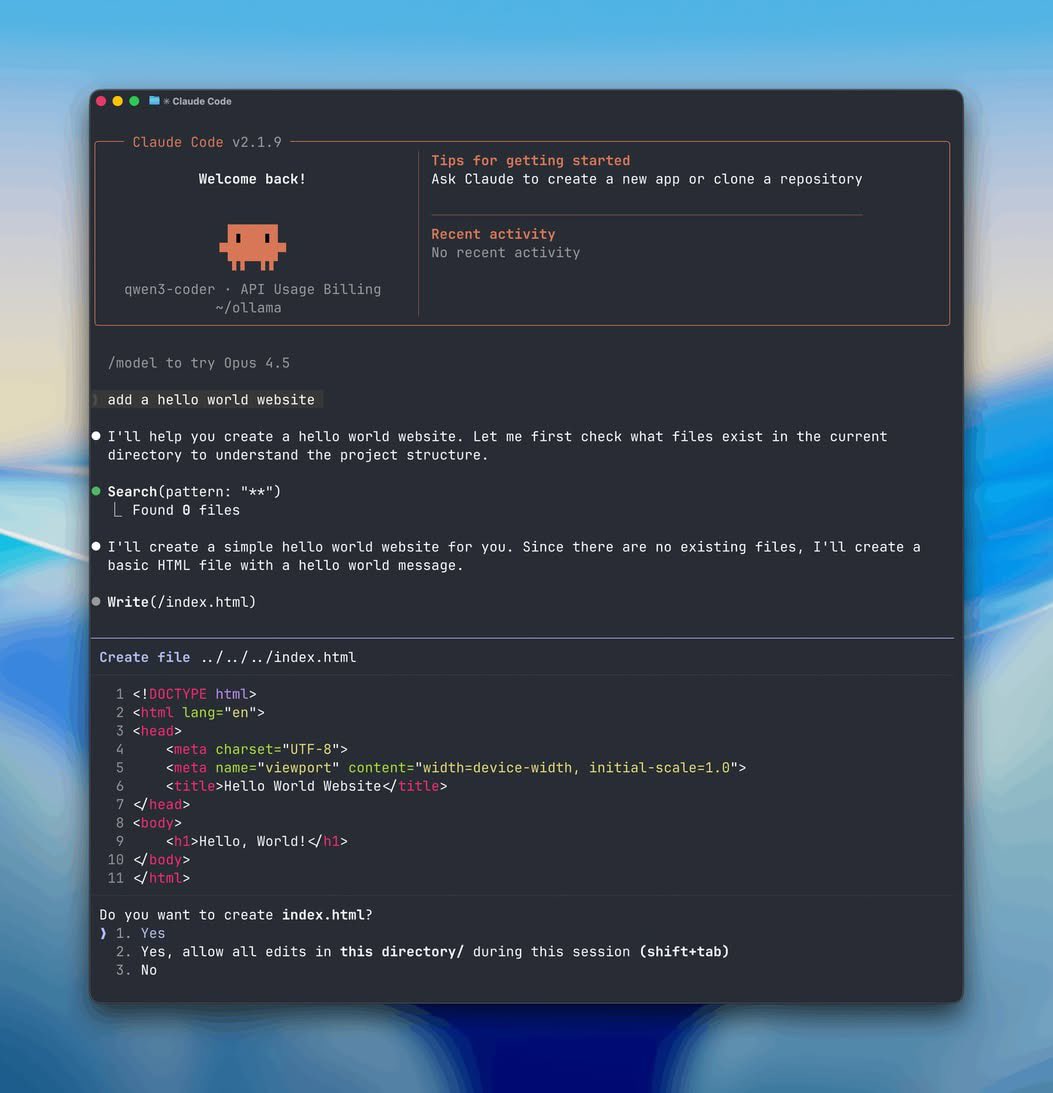
🚨BREAKING: You can now run Claude Code for FREE. No API costs. No rate limits. 100% local on your machine. Here's how to run Claude Code locally (100% free & fully private):




Yearly repost and reminder that an unspecified government agency proactively takes this video down from Youtube all the time