SuperfluousSecurity
54.5K posts
SuperfluousSecurity
@SuperfluousSec
Networks, security, infosec, I'll cyber all over. Constitutionalist. Train er' day on cyber range & shooting range, hone skills.


Teenagers are sharing photos of their AP U.S. Government textbooks, and the sheer amount of indoctrination is wildly disturbing. Apparently, Barack Obama is ideologically a right wing authoritarian. Hillary Clinton and George W Bush are entirely indistinguishable politically. Donald Trump is of course virtually the same as Hitler. @tedcruz is apparently more radically authoritarian than Fidel Castro AND Joseph Stalin..??!!?? @Linda_McMahon — can we expedite some major changes to American public education?





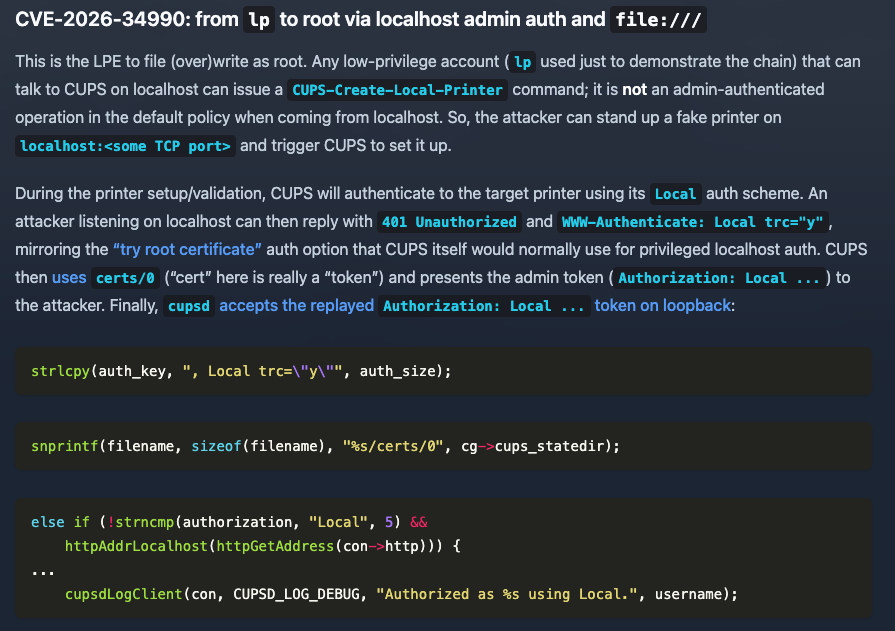








Qilin EDR killer infection chain blog.talosintelligence.com/qilin-edr-kill…







Understand when you build your debates about “them” and “they” are not going to allow you and me to let our robots build more robots: We ain’t asking permission. It is already taking shape in garages around the world it will not stop. It is not utopia—it is just not dystopia.