Tweet fijado
Clover
1.5K posts


Clover
@actuallyclover
26 y/o artist w/ Bachelors in Cyber Operations 💻 | Current System Administrator, Security Researcher & Bug Bounty Hunter 👾
🖥️~root@localhost: Se unió Haziran 2017
672 Siguiendo4K Seguidores

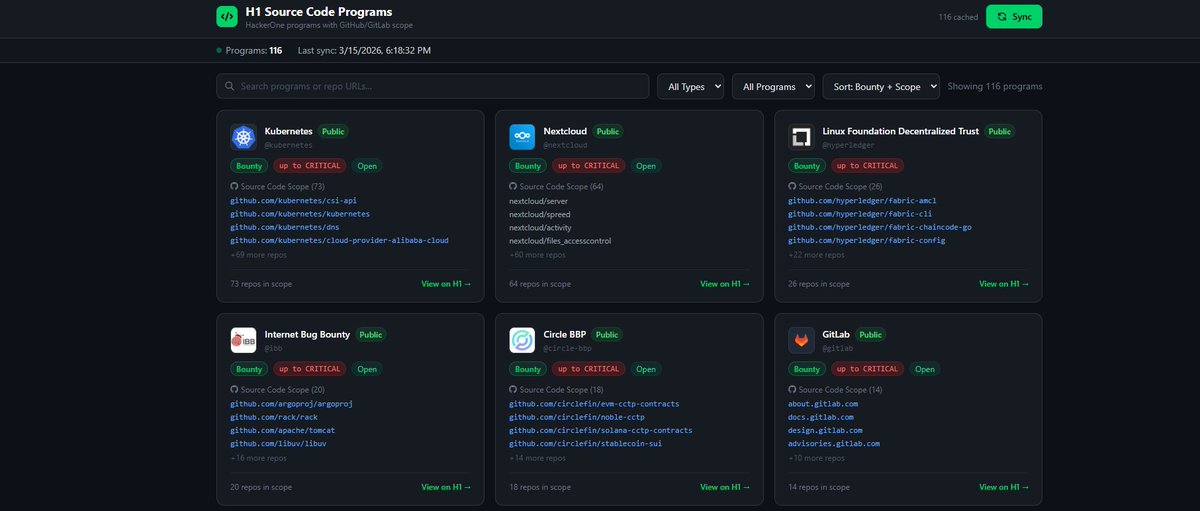
made a tool that maps every HackerOne bug bounty program to its github repos (116+ programs).
github.com/actuallyclover…
#bugbounty #tools #opensource
English

@rez0__ claude is actually insane, a lot of people sleep on it.
English

@thedawgyg same with the midwest 😂 it was 74 Sunday and back down to 30s this week. Leave for work in a trench coat, come home in shorts or vice versa 😂
English

@ctbbpodcast @thedawgyg heck yeah I was wondering when yall were gonna get him on the pod
English

We finally had @thedawgyg on the pod to talk about his origin story, recent Chrome research and how he optimises his AI workflow, his famous 180K payout on Yahoo and a LOT more.
This is an episode we know a lot of people have been looking forward to, check it out!
youtu.be/kpFfde3rNFs

YouTube
English

@thedawgyg dude you've been killing it! it's so dope watching your consistency, super motivating.
English

The VRP replied last night... They needed more proof because they were concerned a patch i provided for my RCE proof would make it easier to achieve the RCE in the Chrome Render. So spent all night working on it, and now have the POC working with 0 code changes to Chrome (only reverting the fix for my vuln). The 'hit rate' is not great (it ranges from as low as ~1-2% success rate up to as high as ~60% success rate). There is absolutely no way now they cant accept this a full RCE (within the renderer) as I am able to run execlp('id') to be logged in the chrome logs 🎉🎉🎉🎉🥳🥳🤞🤞
English

My OG cat Momma Merlin (aka Bad Kitty) came inside the house thru the front door for first time in years. (She normally sneaks in backdoor and stays in my room solo to avoid her kids). She saw several of her grandkids and great grandkids for the first time, and is not a fan of so many kitties lol and this wasn't even all of them..
English

@thedawgyg that’s awesome! i tried reading the articles you posted about fuzzing but when i think fuzzing i think about like ffufing for directories etc.. is the the same in a sense of “fuzzing” for buffer overflows or memory overflow etc? i’m really interested in learning more.
English

i did binary hacking before, when i was a black hat in the 90s. It was just stupid easy back then to find/exploit buffer overflows and all. I decided to go back to it a couple months ago because I had taken a little over 2 years off from bug bounties, and was trying to find a way to get motivated to hack again (outside of my normal job). So started doing the fuzzing to get me motivated. It worked. I now spend most of my free time doing this instead of playing xbox like I was lol. But now I am trying to automate as much of it as I can, so that way I can play some xbox still while it does the boring stuff for me lol
English

@thedawgyg that’s awesome!! how does one go from web app hacking into browser exploitation? 👀
English

@actuallyclover thank you! and yea, its browser based. visiting a website with any version of chrome for the last 6-8 years can trigger the RCE in the renderer process.
English

@rawsalerts shoot it’d sure make me happy to pay off some debt 😂
English

🚨#BREAKING: Elon musk whos worth 852 billion dollars says that money can not buy happiness
English

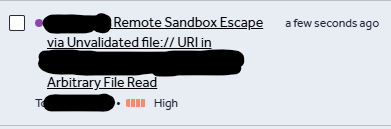
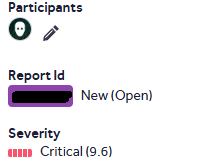
Well the only fun thing I can do now is complete and publish a write up of this attack chain. It used a really fun POST self XSS via a blind form submission on an application that required a login to use but i was able to bypass the login by sending the POST request directly.
Clover @actuallyclover
This H1 triager has always caused issues with my reports. This report was closed because the endpoint I had in my chain wasn't explicitly "owned" by the company yet their scope policy says they're lenient when impact is shown. The endpoint is literally their domain and branded?!
English