Предраг Цујановић � P𝗿𝐞ⅆr𝚊ⓖ Ⅽ𝗎𝐉an𝚘𝕧ⓘć
13.6K posts


Предраг Цујановић � P𝗿𝐞ⅆr𝚊ⓖ Ⅽ𝗎𝐉an𝚘𝕧ⓘć
@cujanovic
Follows you Life is like spaghetti It's hard until you make it No stresso, no stresso It's gonna be espresso




@feross Is there a reason why supply chain attacks are seemingly on the rise? Is AI playing a role?










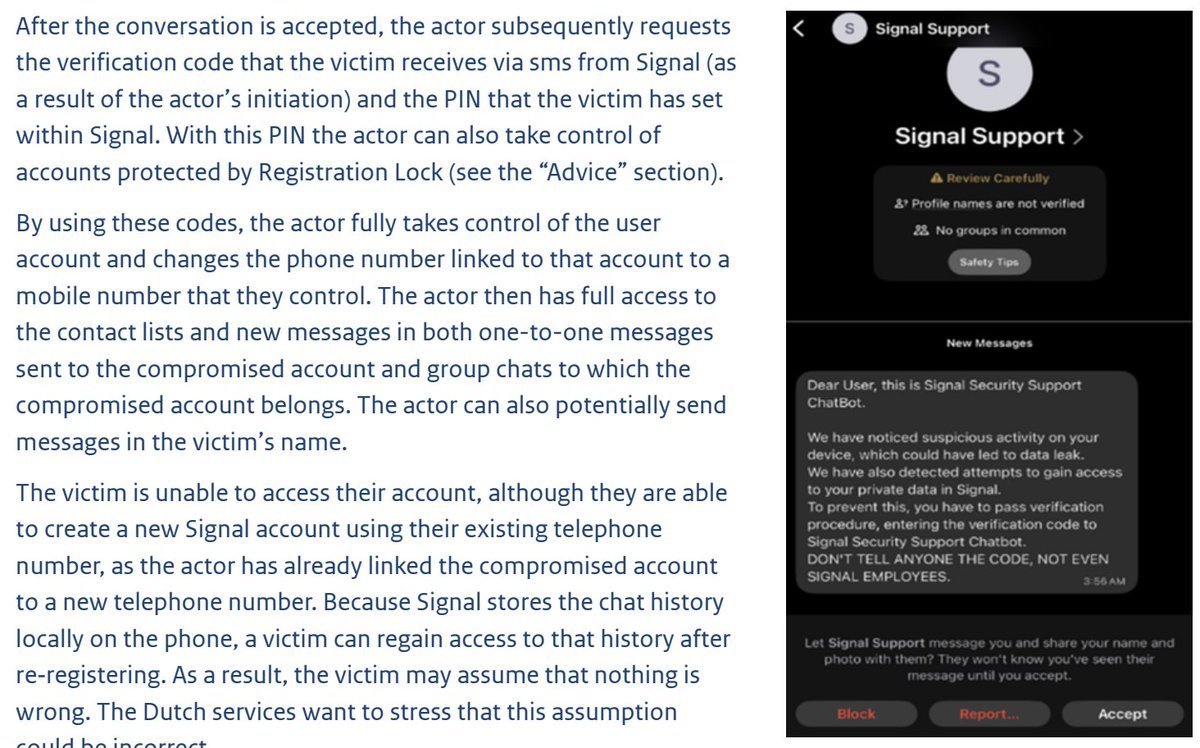
"Russian state hackers are engaged in a large-scale global cyber campaign to gain access to Signal and WhatsApp accounts belonging to dignitaries, military personnel and civil servants" -- MIVD/AIVD english.aivd.nl/documents/2026…



Point-in-time pentests can’t keep up, while fully autonomous testing creates noise. The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory. This 50-second video shows you how it works.