
SOCLabs
102 posts


SOCLabs
@DetectionLabs
The world's first training platform for detection engineers, supporting multiple SIEM languages and using real logs to hone threat detection skills!










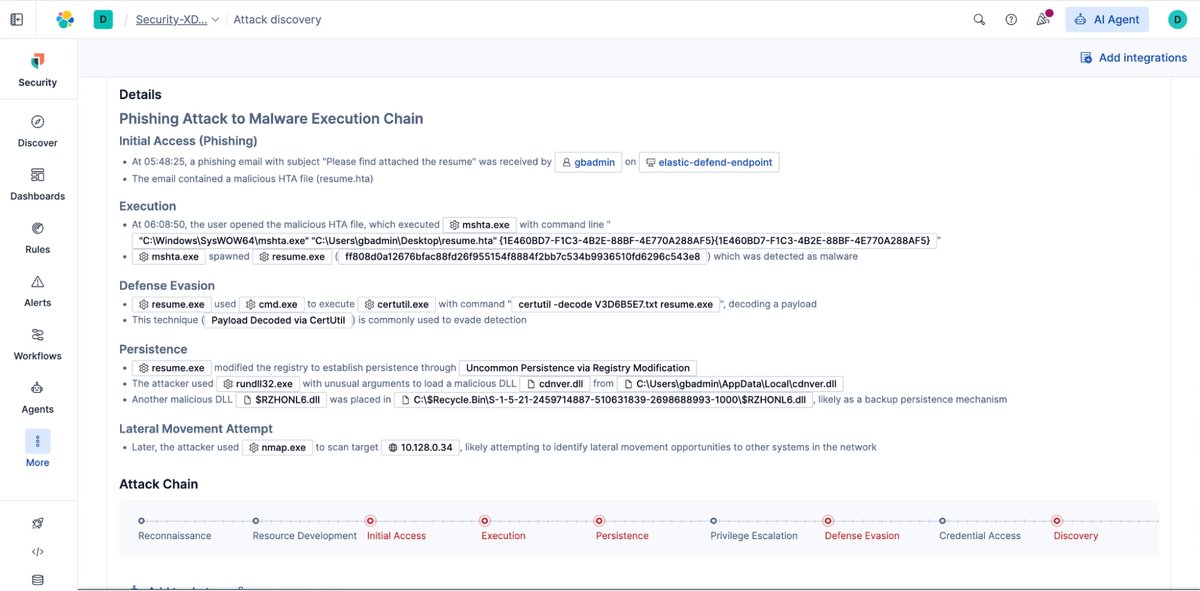







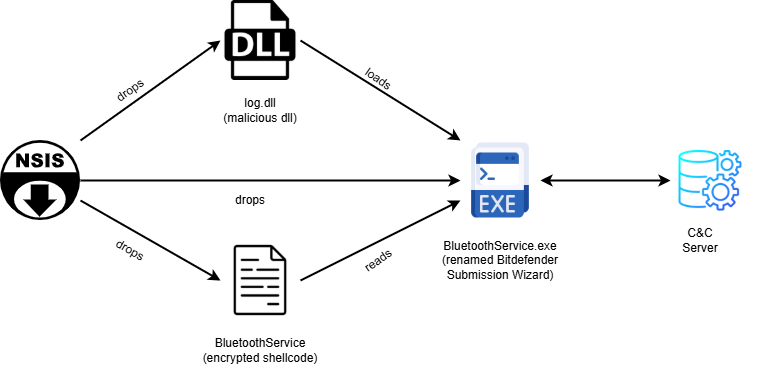
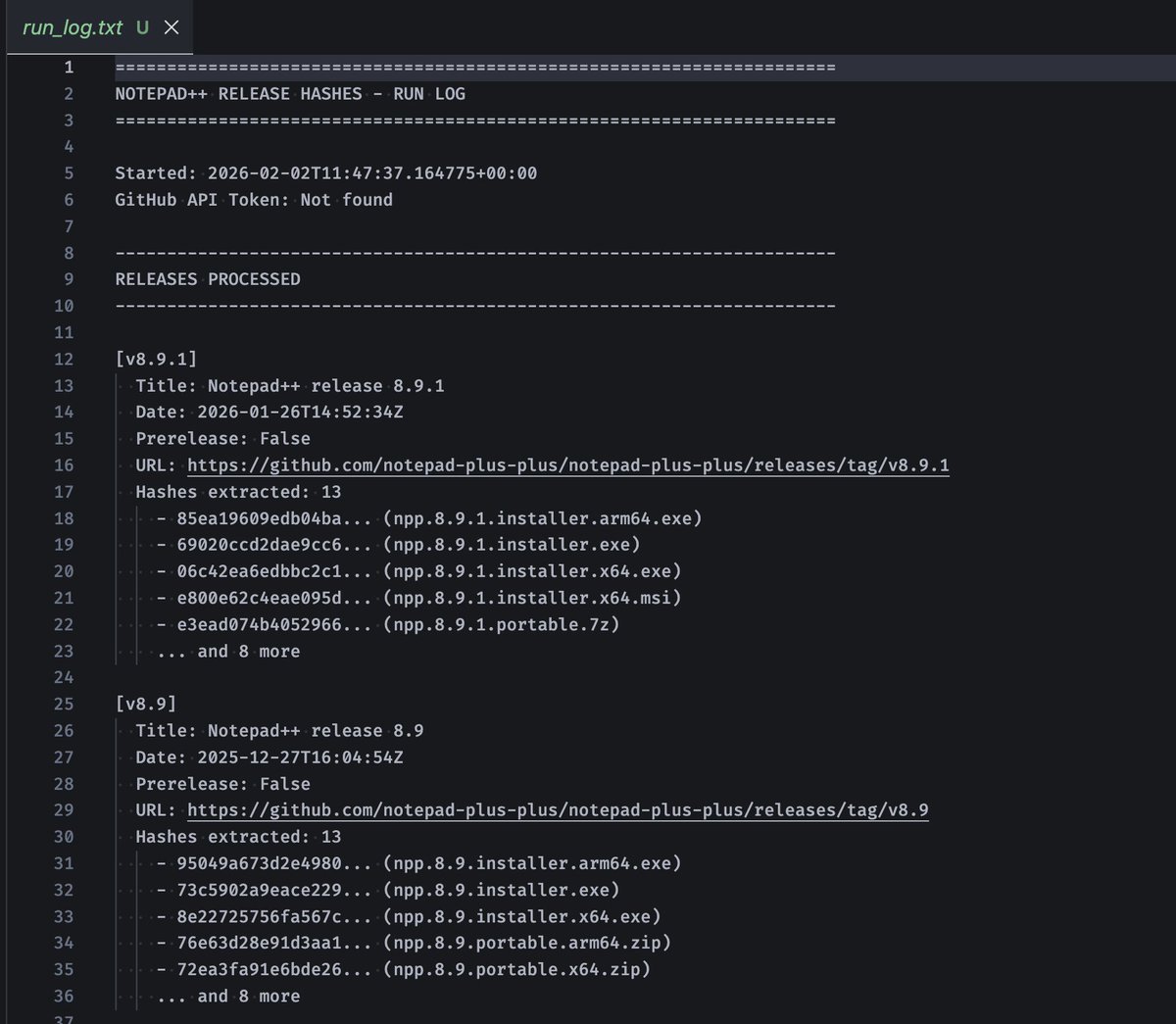
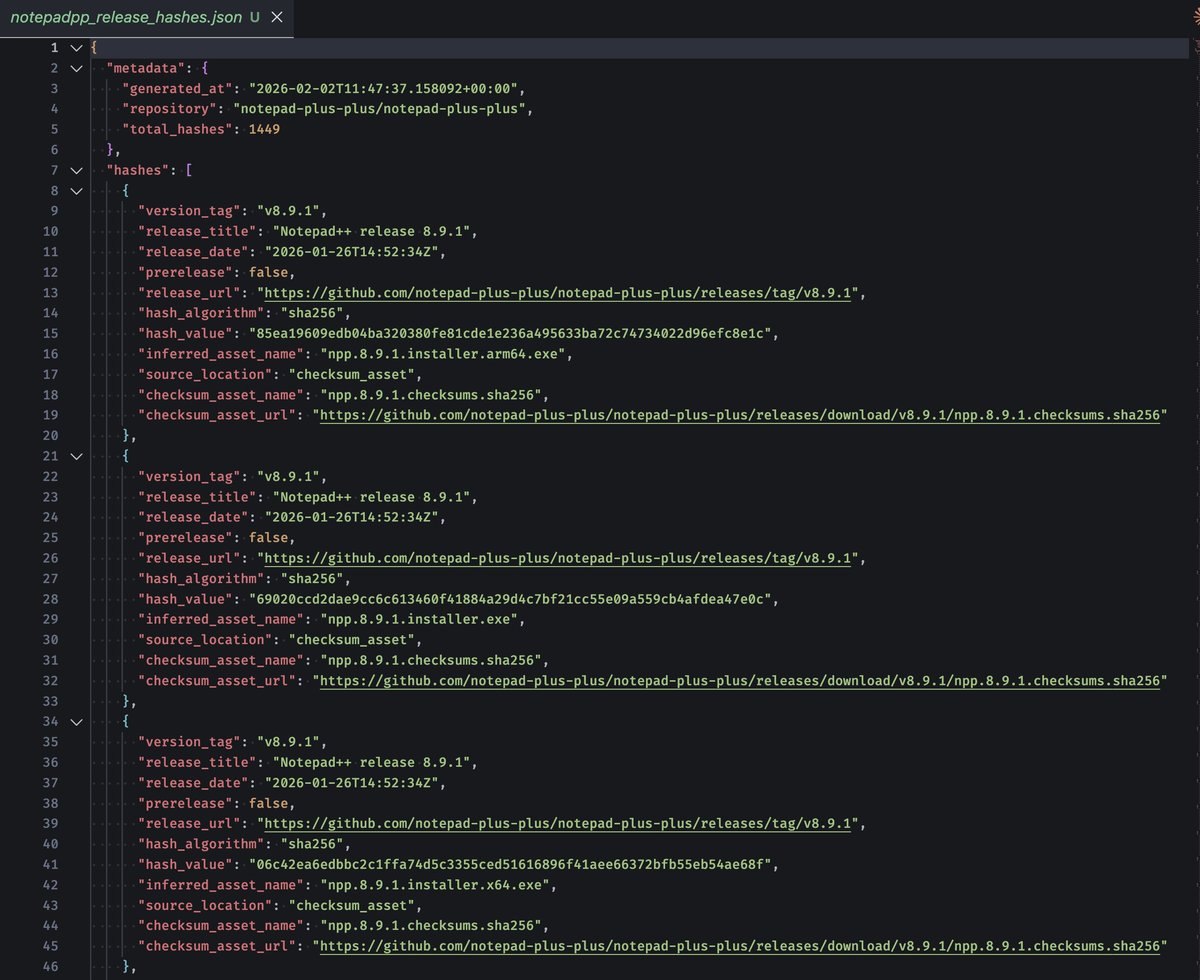
Rapid7 dropped a write-up on the Notepad++ update-chain abuse and - finally - it comes with real IOCs - update.exe downloaded from 95.179.213[.]0 after notepad++.exe -> GUP.exe - file hashes for update.exe / log.dll / BluetoothService.exe / conf.c / libtcc.dll - network IOCs incl. api[.]skycloudcenter[.]com (-> 61.4.102[.]97), api[.]wiresguard[.]com, 59.110.7[.]32, 124.222.137[.]114 by @rapid7 rapid7.com/blog/post/tr-c…


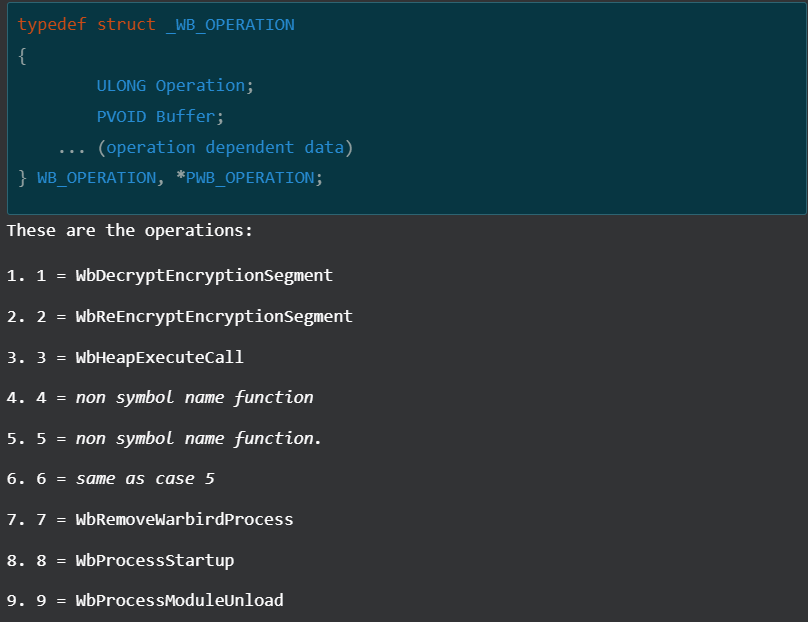
🔎 Rapid7 Labs, alongside our MDR team, has uncovered a sophisticated campaign attributed to the Chinese APT group #LotusBlossom. Find a deep technical analysis of the custom backdoor 'Chrysalis', Notepad++, Warbird, and more in our latest blog: r-7.co/4kaerPA



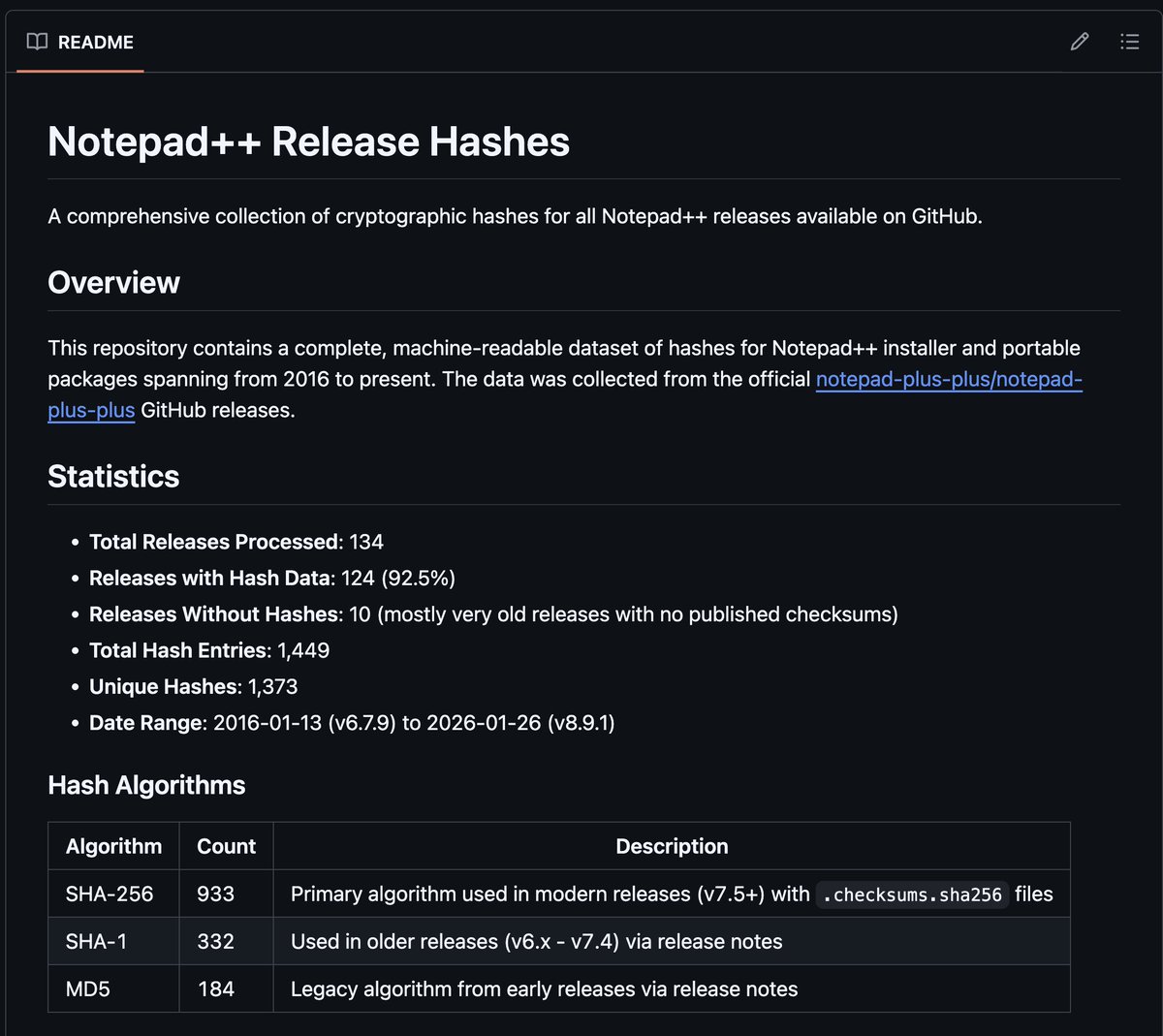

This is bad. Putty level bad. notepad-plus-plus.org/news/hijacked-…
