MSec Operations
27 posts







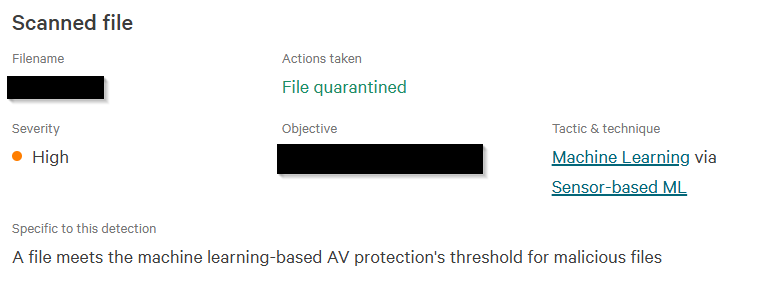







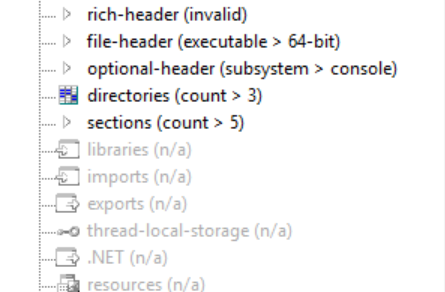
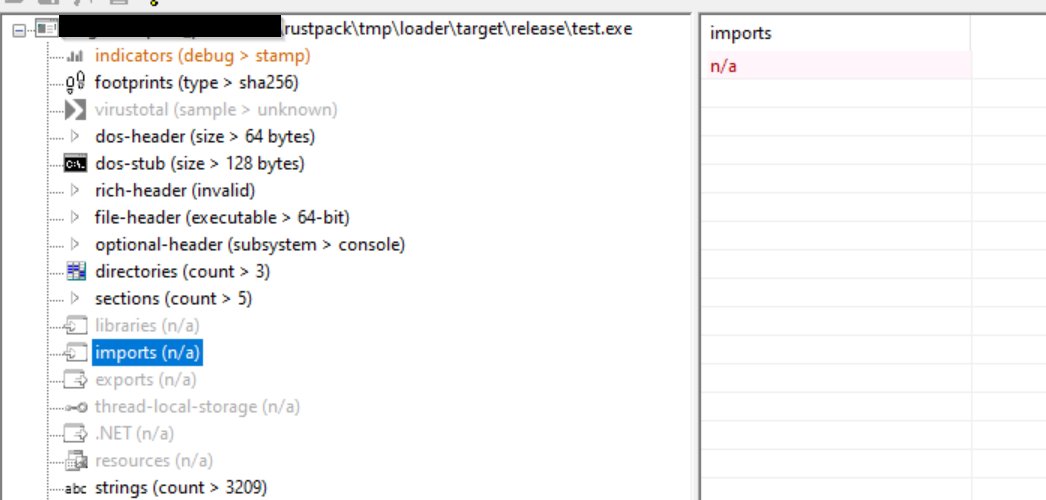
The Ruy-Lopez technique sometimes helps a lot with evasion. The technique was published and open sourced by our founder @Shitsecure two years ago. In #RustPack version 1.3.1 we added a custom, non-public version of this technique that is much more OPSec safe than the public version. The original release only allowed spawn/inject, which is relatively limited. If you wanted to stay in your local process or sideload binary, you could not use it. In RustPack you can use Ruy-Lopez for local execution AND spawn/inject for both executables and DLL payloads. And it will prevent userland EDR DLLs from loading on top of amsi.dll. 🤠 For a few months now, all Sliver payloads have been flagged by many vendors because of the built-in AMSI patch bypass. Most people stuck to modifying the sliver source to get rid of these detections. Well, if amsi.dll is never loaded at all, the patch won't happen either, and you can get rid of this detection just by using the Ruy-Lopez technique. 💡 The following video shows how to pack a Sliver executable with RustPack to get a fully functional connection without any detections. 🔥 And this is just a small use case. A fully interactive Powershell runspace with all amsi related DLLs blocked and no userland hook DLLs sounds great too, right? Easy to build with RustPack in a few seconds. Execute all those Powershell scripts like it's many years before 2025. 🥳 #RedTeam #Pentest #OST #Malware #Maldev


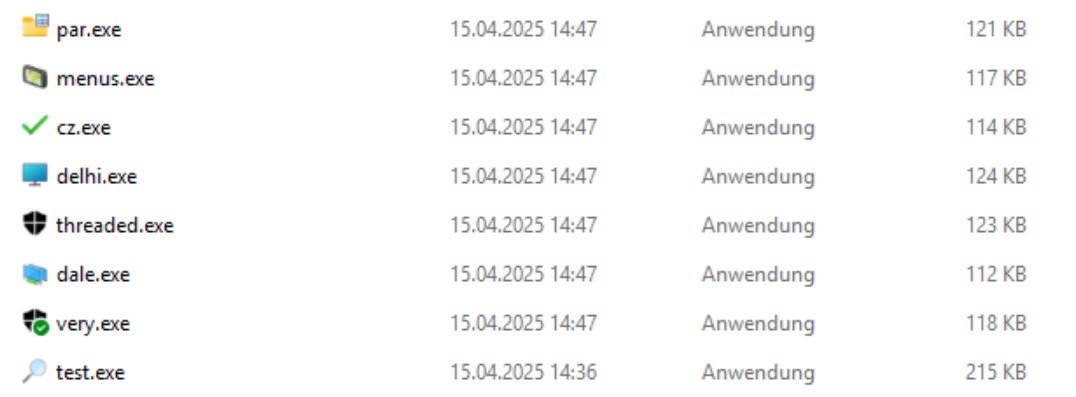

How do you create your payloads in 2025? At MSec Operations we prefer to use DLL sideloading for EDR evasion. This technique allows our malicious code to run within a signed, legitimate executable. Combining this technique with other useful techniques will provide stable execution to fly under the radar. 🛸 The following video demonstrates the use of #RustPack to create such a payload in just a few seconds. The command line usage shows that our input payload is a simple unmodified Apollo C2 executable. We want to clone all the exported functions from the original Windows wininet.dll to create our own library with the same name. The execution of the payload will be delayed by ~5 seconds in this case, without using the Win32 sleep function, but by performing random calculations. ⏲️ Hardware breakpoints are used to bypass the Antimalware Scan Interface (AMSI). Without an AMSI bypass, Apollo would be flagged as a C# assembly when loaded. 🎓 Our payload will only fire on a domain joined system, this basically prevents it from running in e.g. sandbox environments. 🤠 Last but not least, in this example, the encrypted payload itself is stored in a separate file on the target system and not even in the same folder as our malicious DLL. Anyone analysing just the DLL will never be able to find out what the payload is. Automatic sample submissions for cloud analysis usually only upload the executable or DLL, emulators won't see the real payload either. 🤠 Tired of creating such payloads yourself? With #RustPack it's really easy, and payloads always look completely different, even if the same payload is packed twice to avoid signature-based detection Contact us via info[at]msecops.de for more information! 👍