🐸Smart🐸Contract🐸Programmer🐸
2.5K posts

🐸Smart🐸Contract🐸Programmer🐸
@ProgrammerSmart
https://t.co/1QN0tguH9c https://t.co/9Is13KVO2c https://t.co/k6t3JMxZen https://t.co/LLkIeiANtk
Inscrit le Nisan 2019
238 Abonnements27K Abonnés

Clever way to reverse 32 bytes
simple method -> 32 iterations
clever method -> 5 iterations
# input
A B C D E F G H
# swap 1 byte
B A D C F E H G
# swap 2 bytes
D C B A H G F E
# swap 4 bytes
H G F E D C B A
Code
#L23-L44" target="_blank" rel="nofollow noopener">github.com/risc0/risc0-et…

HT
🐸Smart🐸Contract🐸Programmer🐸 retweeté

PLONKish arithmetization is the constraint framework used in the PLONK polynomial IOP.
It's the approach used to turn computations into polynomial constraints that a proof system can verify.
Heard the term before but never really understood what "PLONKish arithmetization" actually means?
In Episode 5 of my series 🎬 I break it down step-by-step.
Check it out here: youtube.com/watch?v=9CWS1H…
YouTube
English

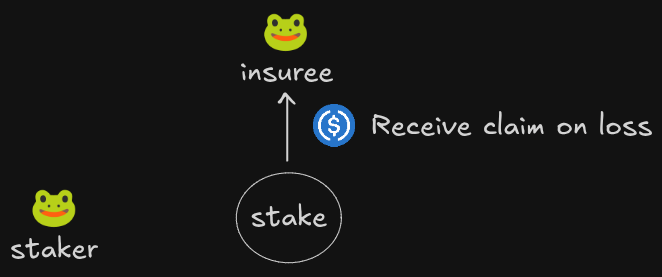
Protocol insurance
1. Insuree pays premium to stakers
2. In a bad event, contracts are halted and stakers pay the insuree
3. Staker withdrawal are queued to prevent bank runs
Code
github.com/t4sk/defi-cook…
Deployment tx
tx-graph-eight.vercel.app/tx/0x5376c0918…


English

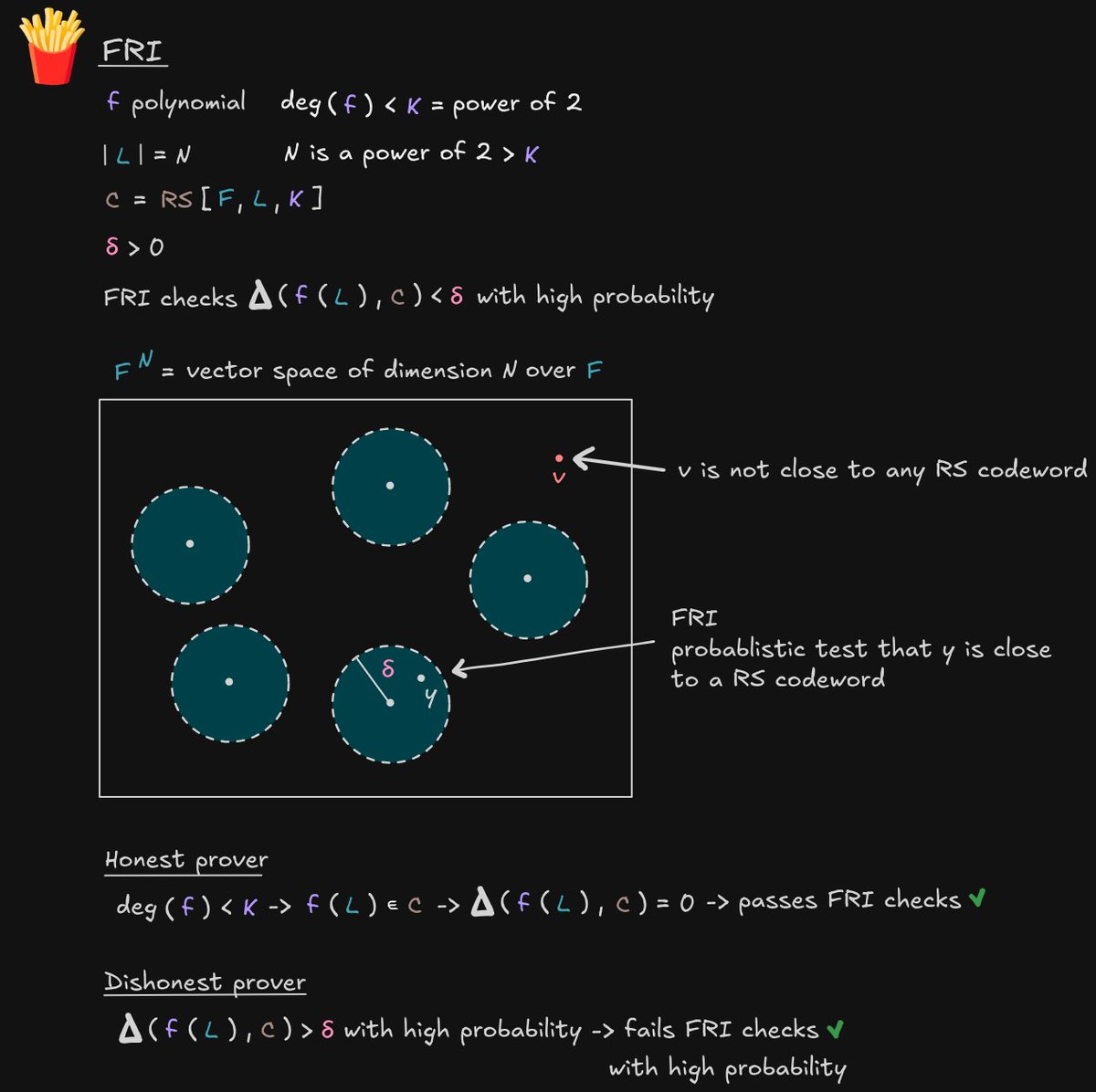
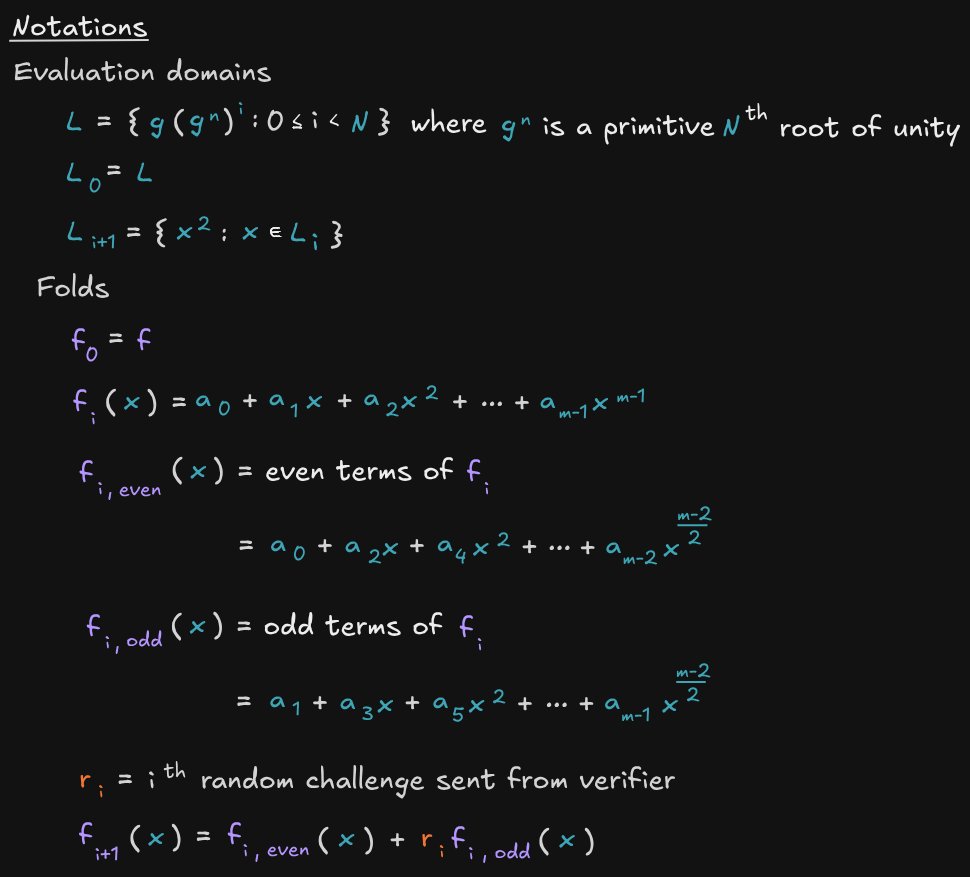
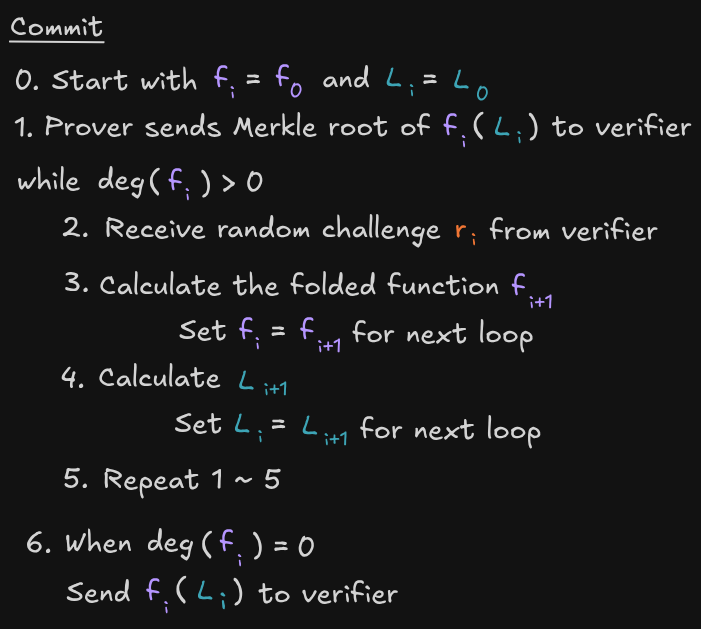
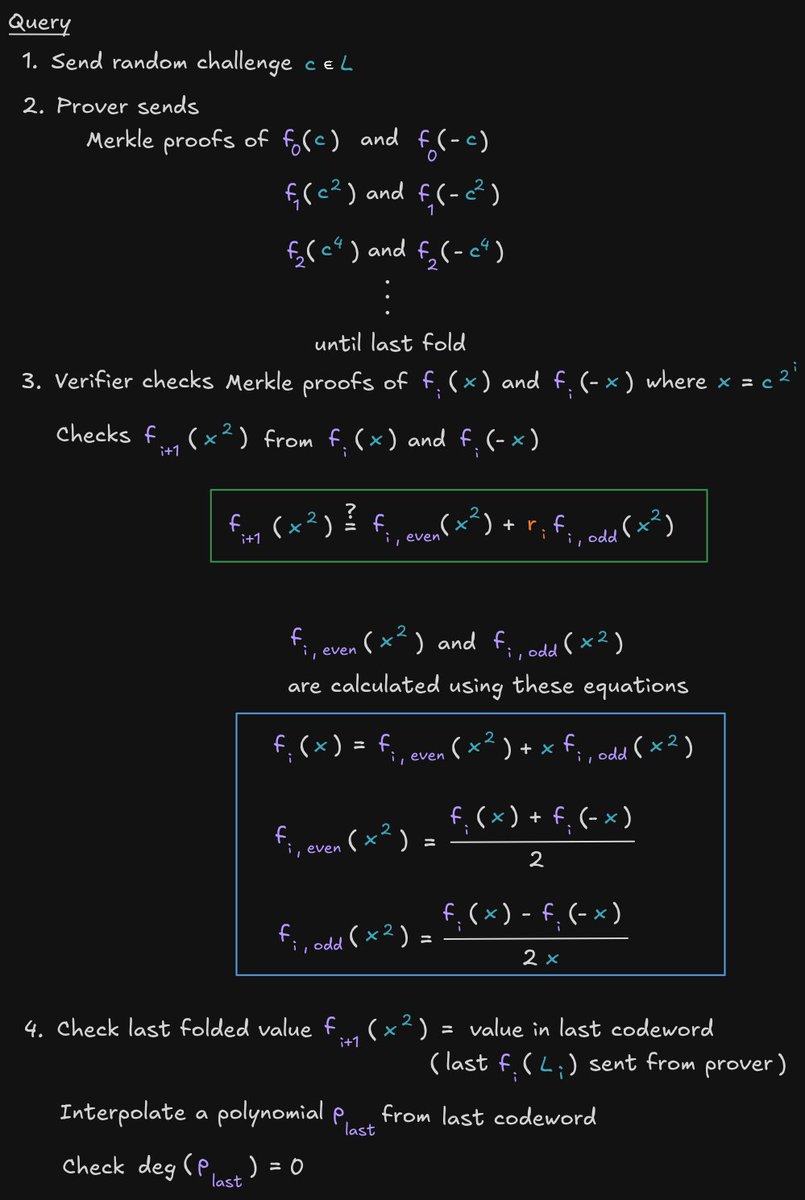
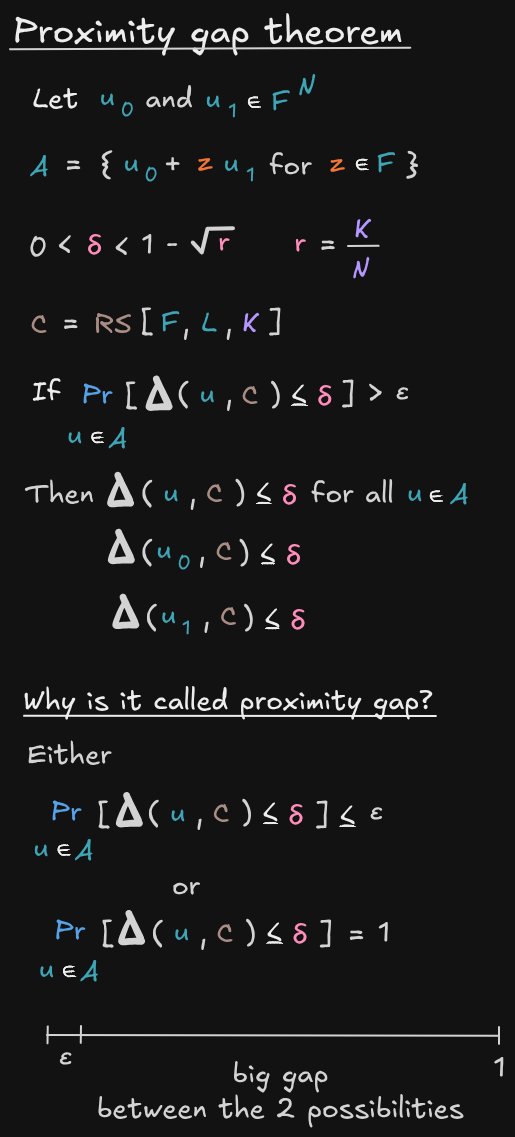
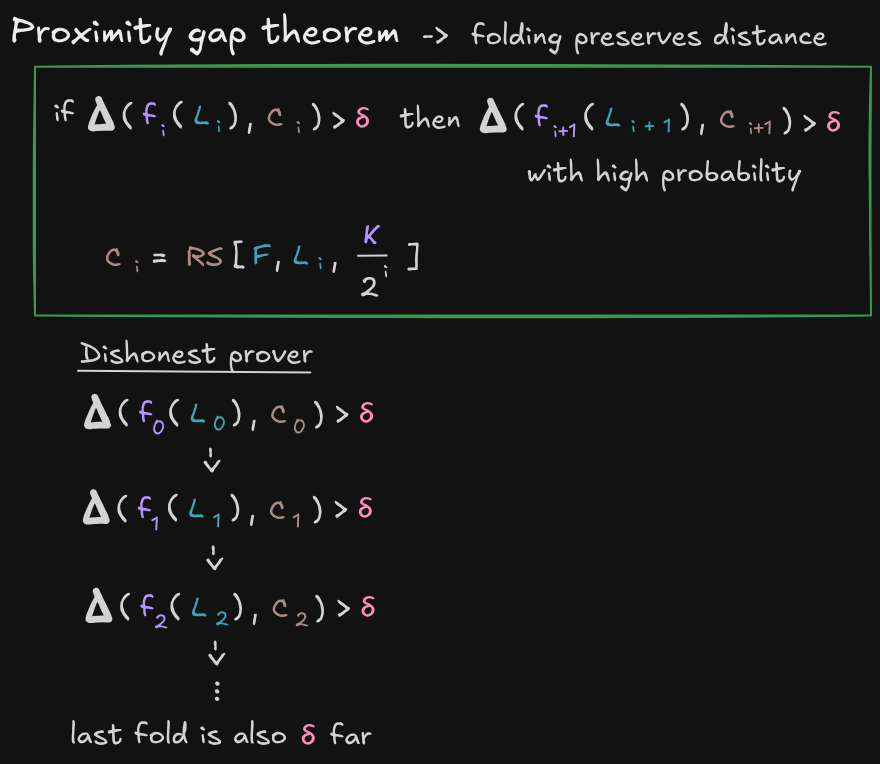
ZKSTARK
Why FRI detects a dishonest prover
- Proximity gap theorem (optional)
- Distance preservation under fold
- Honest and dishonest prover
Notes
github.com/t4sk/notes/tre…

English

KZG Polynomial Commitment Scheme | Zero Knowledge Proofs for Developers ... youtu.be/SHtW-1IYfC8?si… via @YouTube
YouTube
English
🐸Smart🐸Contract🐸Programmer🐸 retweeté

I Saved Injective's $500M. They Pay Me $50K.
I like hunting bugs on @immunefi . I'm decent at it.
- #1 — Attackathon | Stacks
- #2 — Attackathon | Stacks II
- #1 — Attackathon | XRPL Lending Protocol
- 1 Critical and 1 High from bug bounties (not counting this one)
Life was good. Then I found a Critical vulnerability in @injective .
This vulnerability allowed any user to directly drain any account on the chain. No special permissions needed. Over $500M in on-chain assets were at risk.
I reported it through Immunefi. The next day, a mainnet upgrade to fix the bug went to governance vote. The Injective team clearly understood the severity.
Then — silence. For 3 months. No follow up. No technical discussion. Nothing.
A few days ago, they notified me of their decision: $50K. The maximum payout for a Critical vulnerability in their bug bounty program is $500K. I disputed it. Silence again. No explanation for the reduced payout. No explanation for the 3 month ghost. No conversation at all. To be clear: the $50K has not been paid either.
I've seen others share bad experiences with bug bounty payouts recently. I never thought it would happen to me. I can't force them to do the right thing. But I won't let this be forgotten.
I will dedicate 10% of all my future bug bounty earnings to making sure this story stays visible — until Injective pays what I deserve.
Full Technical Report: github.com/injective-wall…
English


@EChinagozim Have you tried
solidity-by-example.org
English

@ProgrammerSmart Any rich lessons to comprehensively digest solidity
I am aware of cyfrin , I find it difficult to understand
English


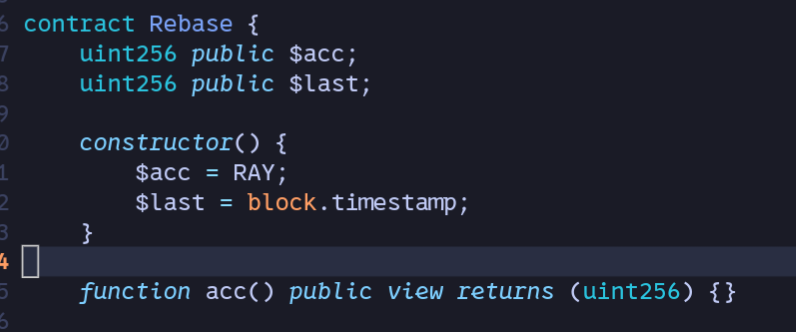
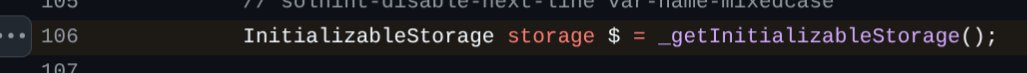
@EChinagozim Namespace for storage variables without clever code like this
#L106" target="_blank" rel="nofollow noopener">github.com/OpenZeppelin/o…
After a little experiment, I concluded that it was indeed confusing since Solidity creates read only functions for public state variables, these functions will have $ prefix.
English

bro is reinventing php from first principles
🐸Smart🐸Contract🐸Programmer🐸@ProgrammerSmart
Like or dislike? Prefix storage variables with $
English
🐸Smart🐸Contract🐸Programmer🐸 retweeté
🐸Smart🐸Contract🐸Programmer🐸 retweeté

We are hiring a DeFi Risk & Strategy Lead!
- 2 to 5 years of deep, hands-on DeFi experience
- Can design leveraged yield strategies end-to-end: collateral → borrow → deploy → monitor → unwind
- Strong lending protocol knowledge at the parameter level (Aave, Compound, Morpho, Euler)
- Strong on-chain analytics + risk judgment (Dune SQL, Python/web3.py, Solidity reading, liquidation mechanics, RWAs)
Apply now (link in comments) or refer a friend!

English
🐸Smart🐸Contract🐸Programmer🐸 retweeté

@ProgrammerSmart I've made a short video about this recently, but for sha256 precompile x.com/i/status/20251…
typicalHuman@typicalHumanDev
How SHA256 works in Solidity? Youtube version: youtube.com/shorts/V4nE1zG…
English

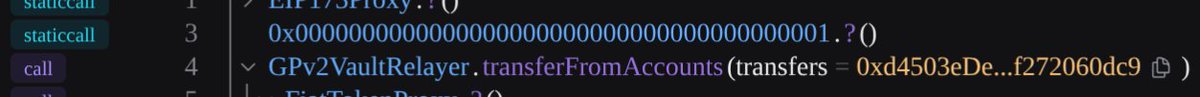
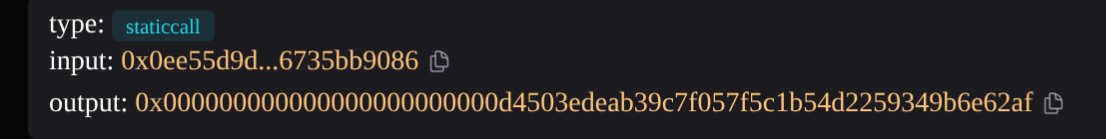
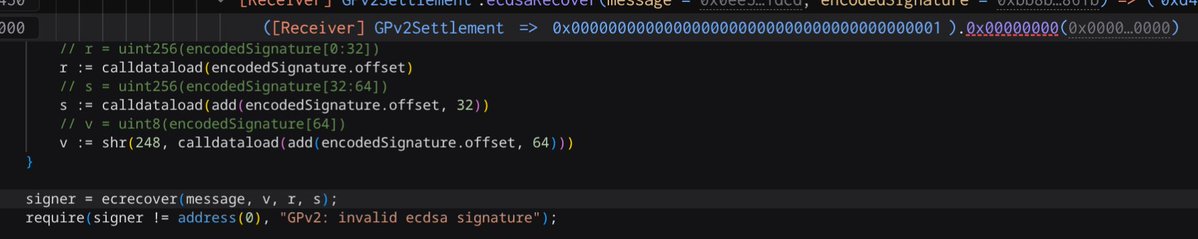
How is it possible that a call to address(1) returns data?
Precompiles
address(1) = call to ecrecover
transaction
tx-graph-eight.vercel.app/tx/0x1a696cad4…
English