Tweet épinglé

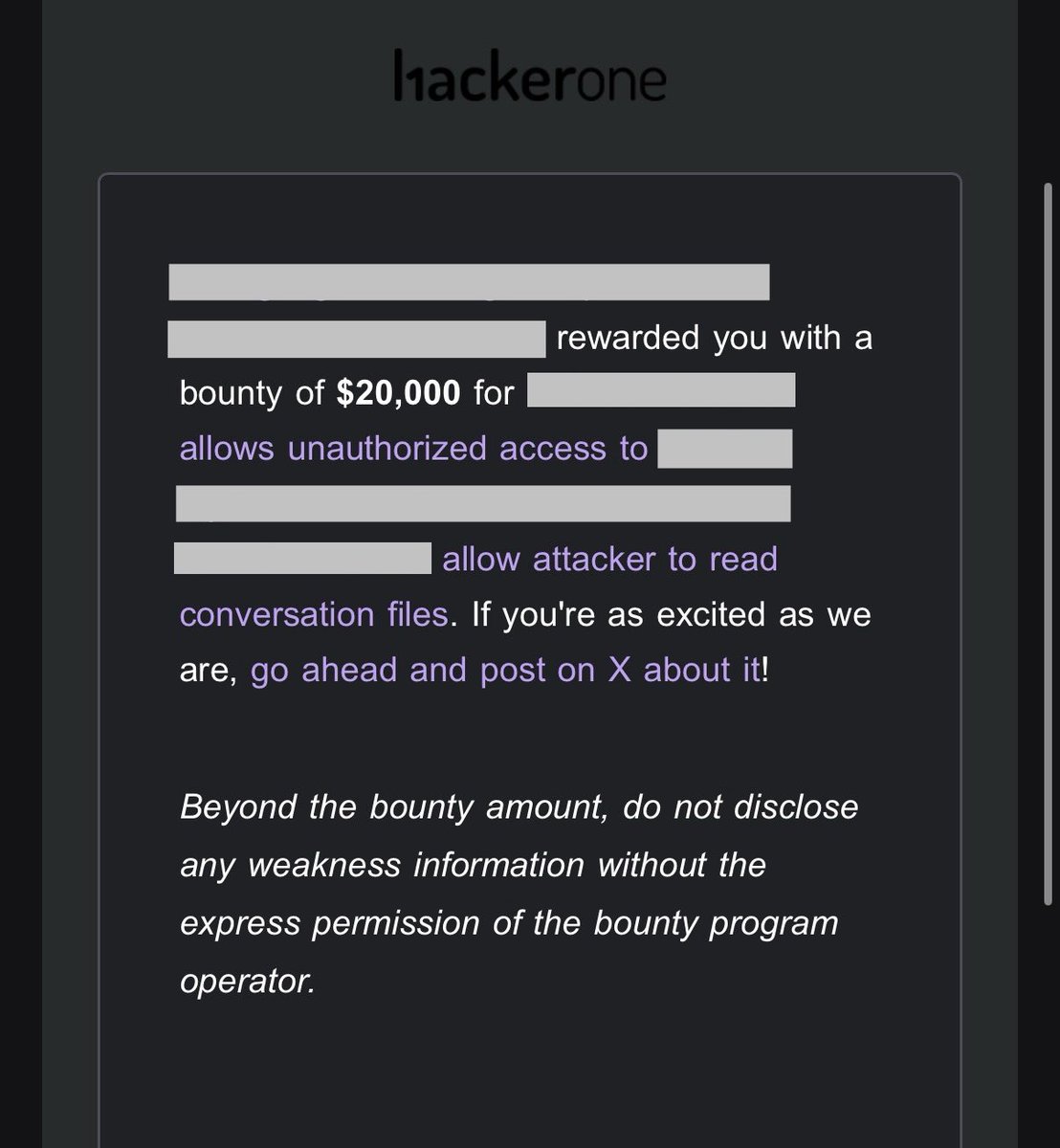
Yay, I was awarded a $25,000 bounty on @HackerOx01! #TogetherWeHitHarder
Severity: Critical
#hackerone #BugBounty #bugbountytips #bugbountytip #infosec #CyberSec #bughunter #API #apisecurity #cybersecuritytips #ethicalhacking #Pentester #Hacking

English