Maher Azzouzi
153 posts


Maher Azzouzi
@maherazz2
Vulnerability Research & Exploit Development
Inscrit le Eylül 2022
420 Abonnements1.2K Abonnés

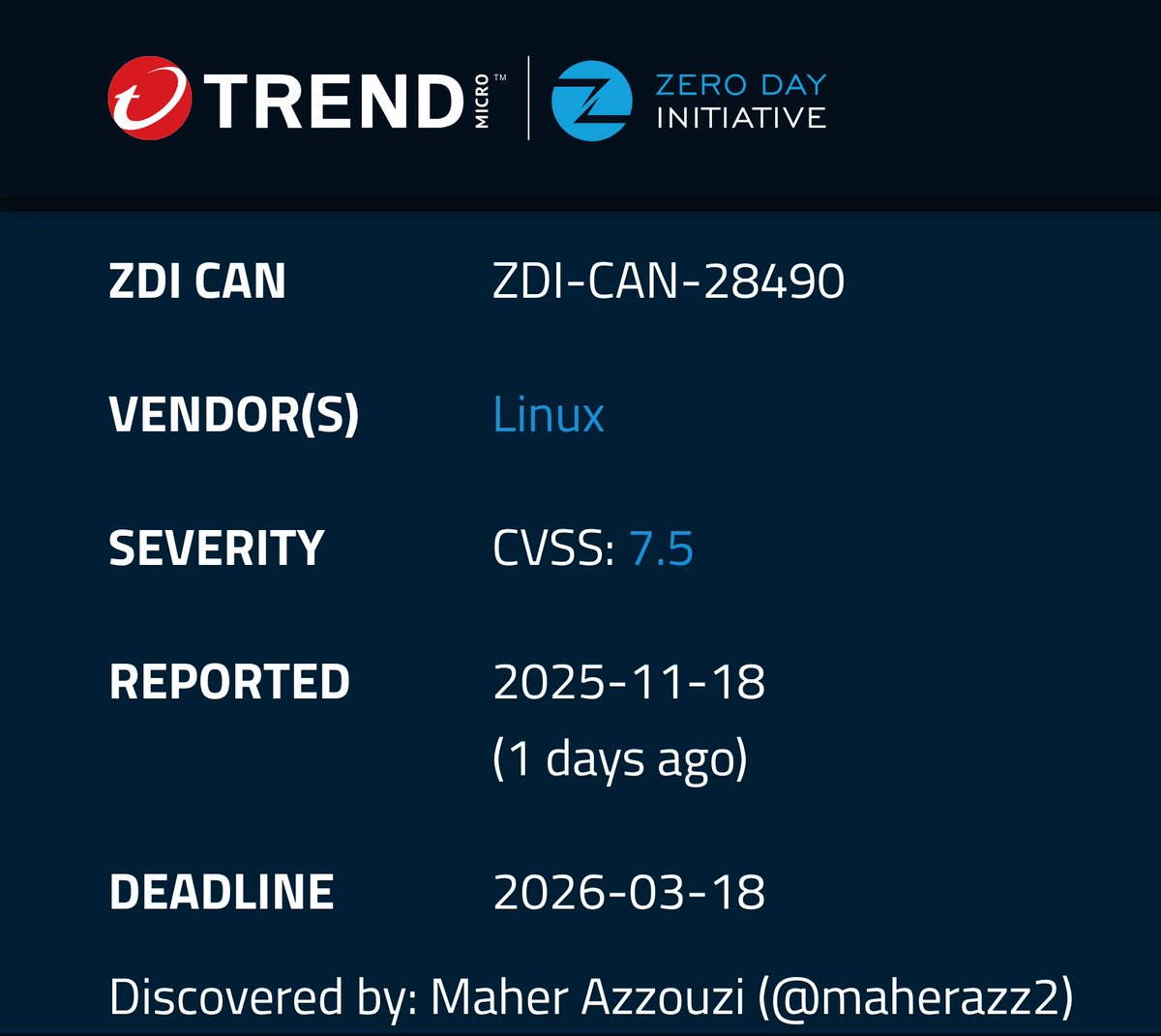
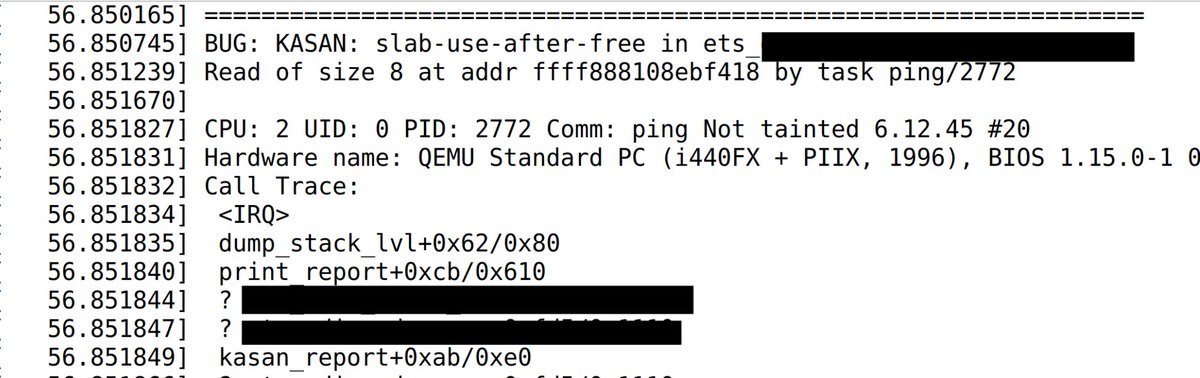
Technical details for a kernel UAF vulnerability I reported earlier (analysis + PoC).
kernel.googlesource.com/pub/scm/linux/…
Dansk

@Michaelelkamika Thank you! No fuzzing involved, all auditing.
English

No more POC tickets? @POC_Crew. Wanted to visit this year’s edition, it seems im a bit late
English

AMD August 2025 Security Bulletins (AMD-SB-6018 and AMD-SB-5007) feature my discovery CVE-2024-36342, a heap overflow in the @AMD GPU driver, rated with the highest severity in AMD-SB-5007 and listed among the most severe vulnerabilities in AMD-SB-6018.
amd.com/en/resources/p…
English

@a13xp0p0v @PwnieAwards Thanks a lot for sharing, really appreciate your time, the blog, and all the effort you put into it!
English

@maherazz2 @PwnieAwards For winning races, I usually employ this trick: I empirically define min timeout, max timeout, and step value. Then I try hitting the race condition in a loop increasing the timeout from min to max adding step. For some races, I can find params giving a sufficient success rate.
English

My new article: "Kernel-hack-drill and a new approach to exploiting CVE-2024-50264 in the Linux kernel"⚡️
I tell a bug collision story and introduce my pet project kernel-hack-drill, which helped me to exploit the hard bug that received @PwnieAwards 2025
a13xp0p0v.github.io/2025/09/02/ker…


English

@a13xp0p0v @PwnieAwards Thank you so much for clarifying! Just curious — was this always reliable for you, or did the interrupt sometimes miss the window? And when you say gradually increasing the timeout, was it in nanosecond-level steps?
English

@maherazz2 @PwnieAwards Thanks for the question! I tried this in a loop gradually increasing the timeout until success.
English

@roddux Hello, yep i stumbled on the same off-by-one. Why this wasn't patched before btw? do you want to discuss it a bit?
English

@maherazz2 I see your name on the mailing list message for this patch ;)
English

This just got fixed a couple days ago: git.kernel.org/pub/scm/linux/…
Nothing says enterprise-grade OS like..: public kernel memory corruption bugs (reachable from unpriv!) remaining unpatched for several months
:^)
roddux@roddux
reachable from unpriv, but you need a network device with hardware offload and >1 txqueue. i looked at veth/hwsim and couldn't figure out how to exploit it lmao
English

A bit late, but I just published my blog post on bypassing Ubuntu’s sandbox! Hope you enjoy it!
u1f383.github.io/linux/2025/06/…
English

I got a new whiteboard, it’s so over for ya’ll

chompie@chompie1337
this Panda Express fortune been keeping me going for weeks
English

Just finished my writeup about CVE-2025-23369, an interesting SAML authentication bypass on GitHub Enterprise Server I reported last year. you can read about it here: repzret.blogspot.com/2025/02/abusin…
English

@azz_maher I wrote one too a decade ago. It was a fun bug if even a bit mind blowing how complicated futex is...
English
I wrote an LPE for CVE-2014-3153 AKA Towelroot, a bug in the Linux Kernel that was used to root Android devices earlier. The original exploit is closed source and protected against reverse engineering.
PoC + mini write-up here:
git.io/Jnazk
English