Tweet épinglé

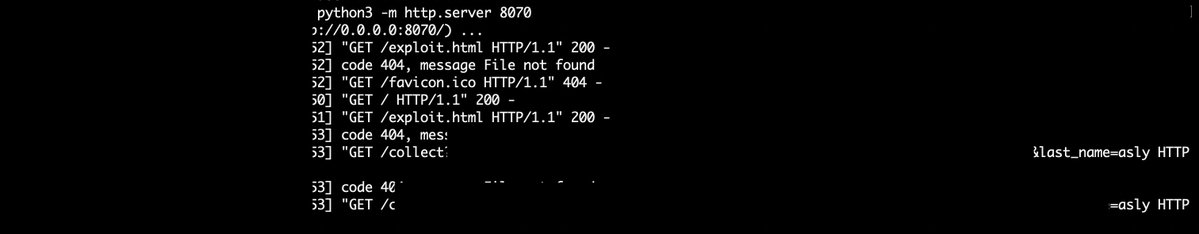
Hey Everyone, do checkout how me and my brother @Zero2Infinity_ bag our 1st $$$$ bounty individually.
v3d.medium.com/story-of-bount…
#bugbounty #bugbountytips #bugbountytip #bughunter #hacker #cybersecurity #hackerone #bugcrowd

English